Domain Summary
The Investigate Domain Summary is displayed whenever you search for a domain name in the Smart Search or Pattern Search. You can specify a fully-qualified domain name (FQDN), for example: subdomain.subdomain.domain.com. Umbrella Investigate is protocol agnostic.
Note: You should not include the protocol or any URL information in the search query.
Table of Contents
About Domain Summary
The Domain Summary lists the Investigate Domain Risk Score, sub-scores, security categorizations, content categorizations, and key domain notifications. When a domain is malicious, Investigate displays additional domain details associated with the security category.
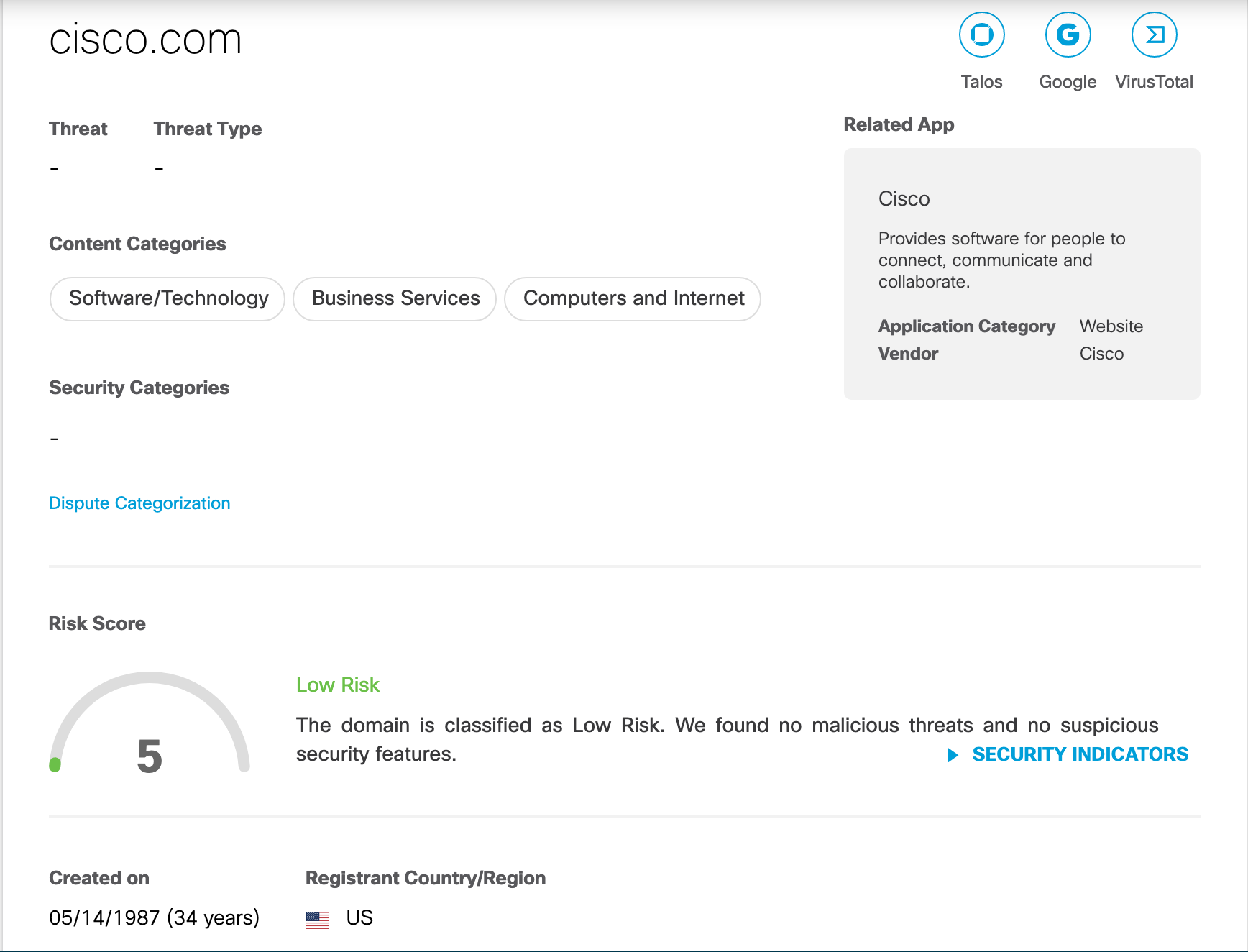
Investigate Domain Risk Score
The Investigate Domain Risk Score is based on an analysis of the domain name, the DNS query behavior of the domain, and analyst reviews of the domain.
An Investigate Domain Risk Score falls into one of these ranges:
- High Risk—(90 to 100)
- Medium Risk—(40 to 90)
- Low Risk—(0 to 40)
An Investigate Domain Risk score emphasizes the lexical characteristics of domain names along with some key behavioral components. These risk scores are synthesized into one overall score—much like a credit score is made of account balances, lending history, debt ratios, and other components. The DNS behavioral components are:
- Lexical
- Keyword Score
- Lexical Score
- Behavioral
- TLD Rank Score
- Geo Popularity Score
Sub-Component Scores
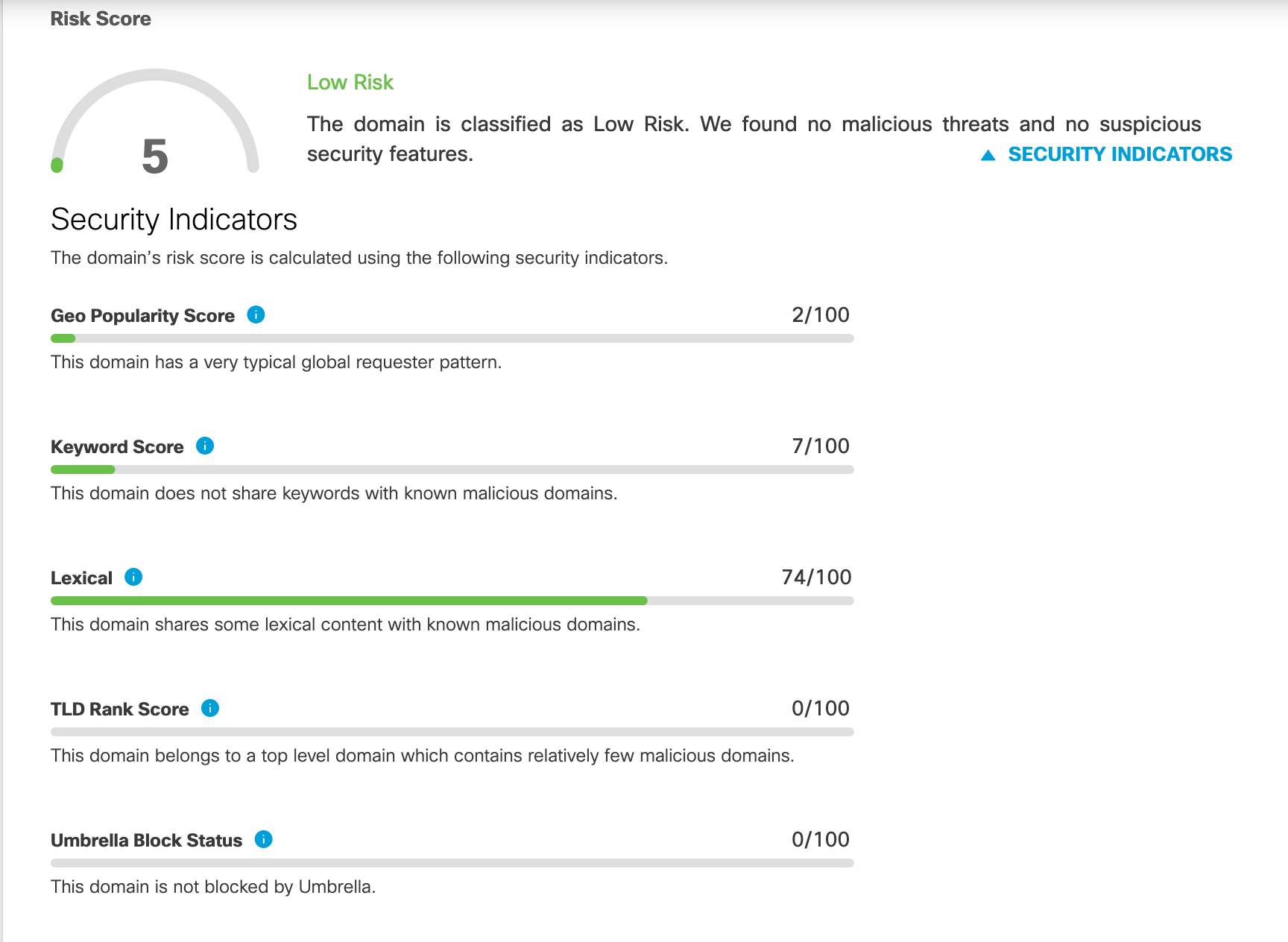
The behavioral component scores are:
- Keyword Score
- Lexical Score
- TLD Score
- Geo Popularity
Note: The Umbrella Investigate overall risk score is created from many indicators.
Keyword Score
Many phishing attacks try to take advantage of the weakest link in the security chain: people. If a domain name contains words related to legitimate companies and services, it is more likely to trick people into clicking. This style of social engineering continues to be a common technique of attackers.
Lexical Score
A mainstay of communication between infected machines and command and control servers are domains created using Domain Generation Algorithms (DGAs). A DGA circumvents any need to embed the location of control servers directly in the malware, and it enables attackers to regain control of their botnets even in the face of sink holing and takedowns. Using a generalization of the method behind the Cisco Umbrella DGA score, we can reliably predict when hostnames were generated without having to rely on developing models of what lexical patterns to look for.
TLD Score
Not all top level domains (TLDs) are created equal. Over the years, the TLDs of choice for spammers have changed according to the following factors: cost, ease of batch registration, verification of registrant identity, and abuse complaint policies. Using our global reach, we can assess the risk indicated by the currently observed abuse levels, and, combined with our other indicators, help security analysts make more informed decisions.
Geo Popularity
Umbrella's global complement of data centers gives us visibility into DNS requests made by clients around the world. Is a domain getting requests from a country where it typically doesn't? Did the number of countries requesting a domain suddenly change? By analyzing requests to domains across all countries in the world, patterns emerge that allow us to detect anomalous behavior and identify increased risk.
Manage Investigate API Keys < Domain Summary > Dispute a Content Categorization
Updated almost 2 years ago
