Add a New Policy
Best practices for Easy Protect are to only apply the Default policy to your identities; however, you can create a new policy for testing purposes only.
If your organization has unique protection requirements (for example, blocking a destination), update the Default policy to meet those needs so that all of your identities are protected.
- Select networks to protect.
- Configure security settings.
- Select destination lists.
- Configure block pages.
- Review and save your policy.
1. Select Networks to Protect
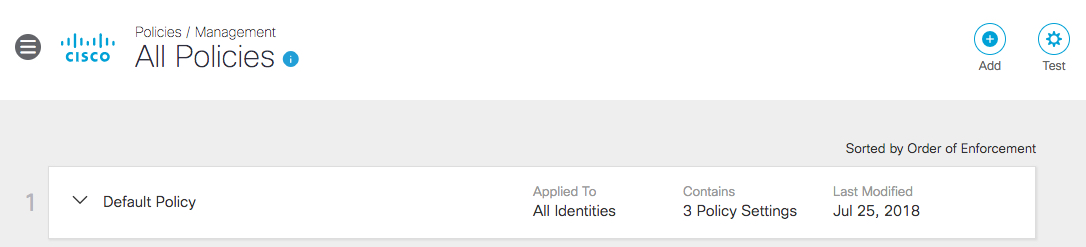
- Navigate to Policies > Management > All Policies and click Add.
When the All Policies page opens for the first time, it only lists the Default policy. You can add a new policy or edit the Default policy. If you edit the Default policy, the Summary page opens, from which you can edit the Policy.
Note: The Default policy applies to all identities. You cannot remove identities from the Default policy.
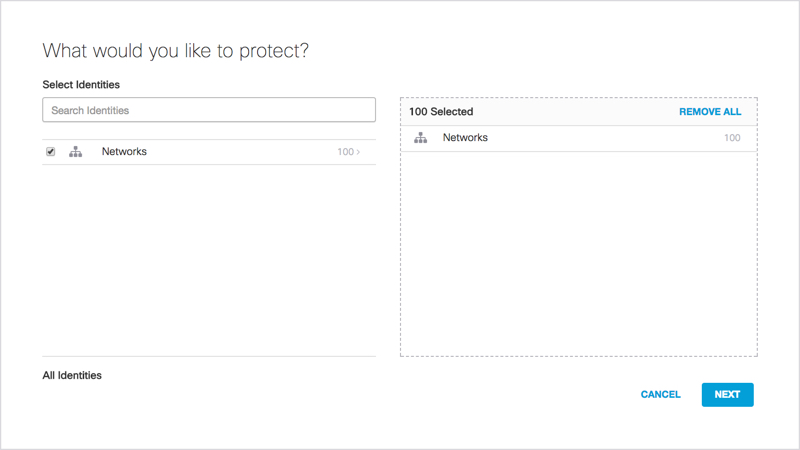
- Select the identities you wish to apply this policy to and click Next.
This can be a subset of the Network identities available to you.
- Expand your list of identities and select the ones you'd like to apply this policy to. To expand your list so that identities are available for selection make sure that Networks is not selected when you expand the list.
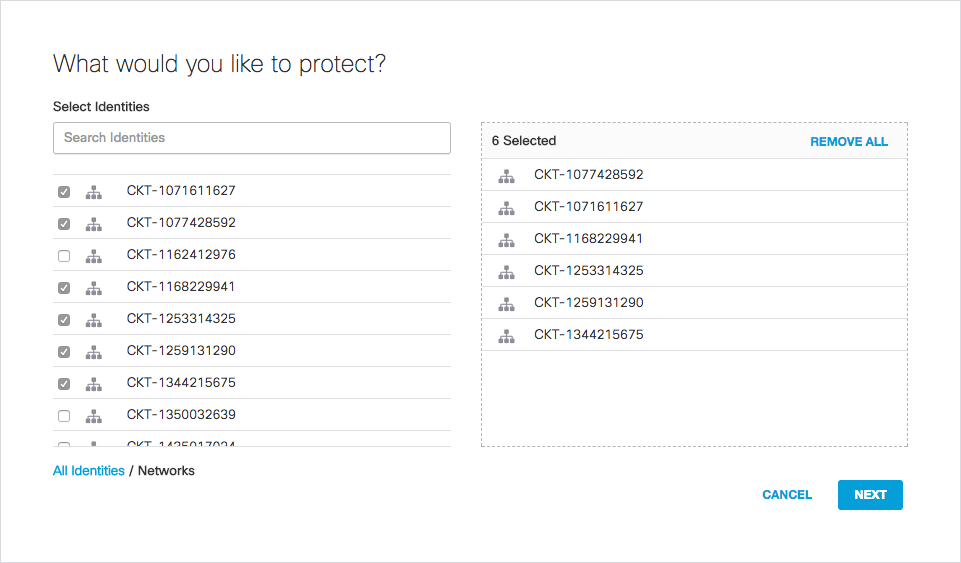
- Click Next.
- Answer the question "What should this policy do?"
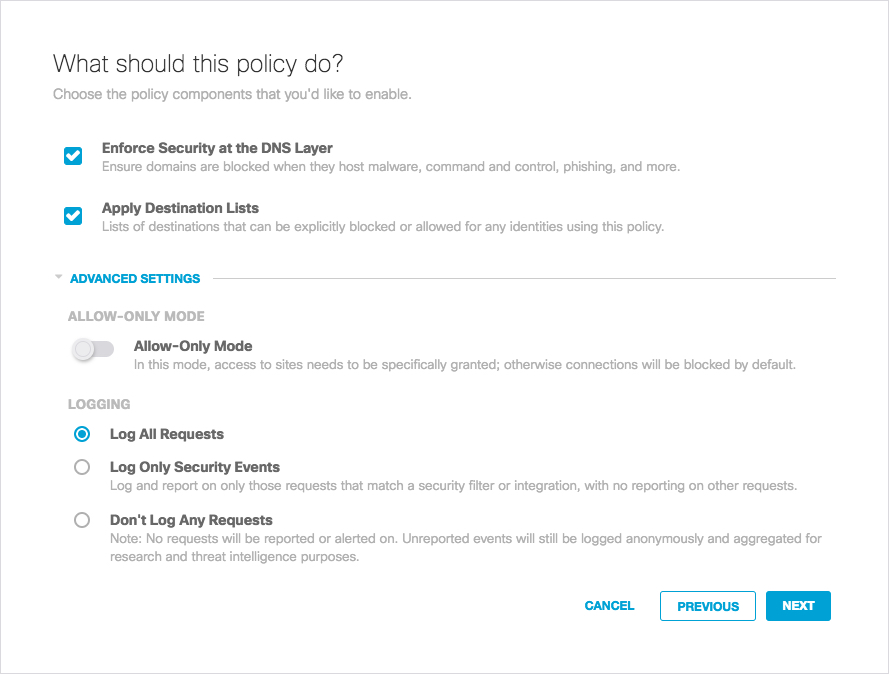
Options are:
- Enforce Security at the DNS Layer—These are settings related to the blocking of domains based on whether they are malicious and provides a base level of security protection. We recommend always selecting this.
- Apply Destination Lists—If you have particular domains you'd like to allow or block, add them to a destination list. There are two by default, block or allow, and you can create more to organize groups of domains. The two defaults are the "Global" lists.
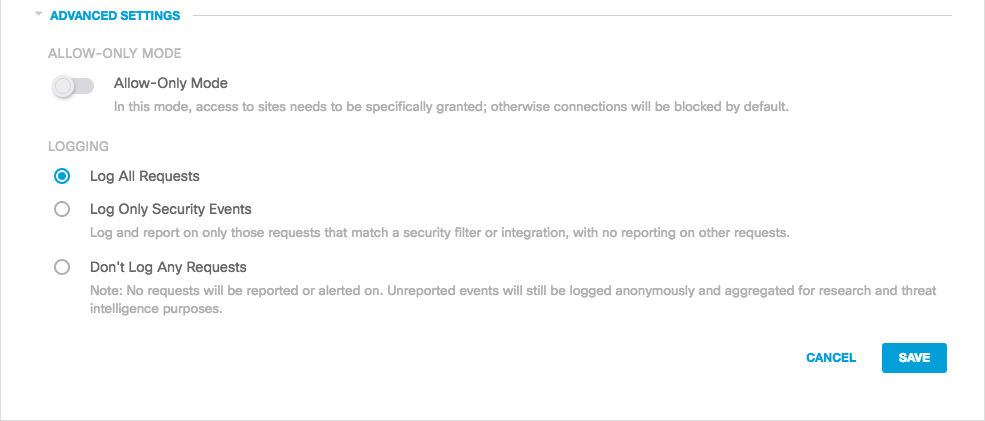
Advanced Settings
- Allow-Only Mode—Blocks access to all sites except those specifically allowed. We recommend that you only enable Allow Only Mode in cases where you wish to allow access to a small subset of domains and block all other domains. Since the result of enabling this feature is to effectively block the internet except for that part you've defined to allow, please use caution if enabling this feature.
Logging—Provides logging for requests and security events. Settings are:
- Log All Requests—For full logging, whether for content, security or otherwise. This option is only available for the default policy, not for newly-created policies.
- Log Only Security Events—For security logging only, which gives your users more privacy.
- Don't Log Any Requests—Disable all logging. If you select this option, most reporting for identities with this policy will not be helpful as nothing is logged to report on.
6. Once you've selected what the policy will do, click Next.
A progress meter appears with the number of steps remaining until you've fully configured the policy.
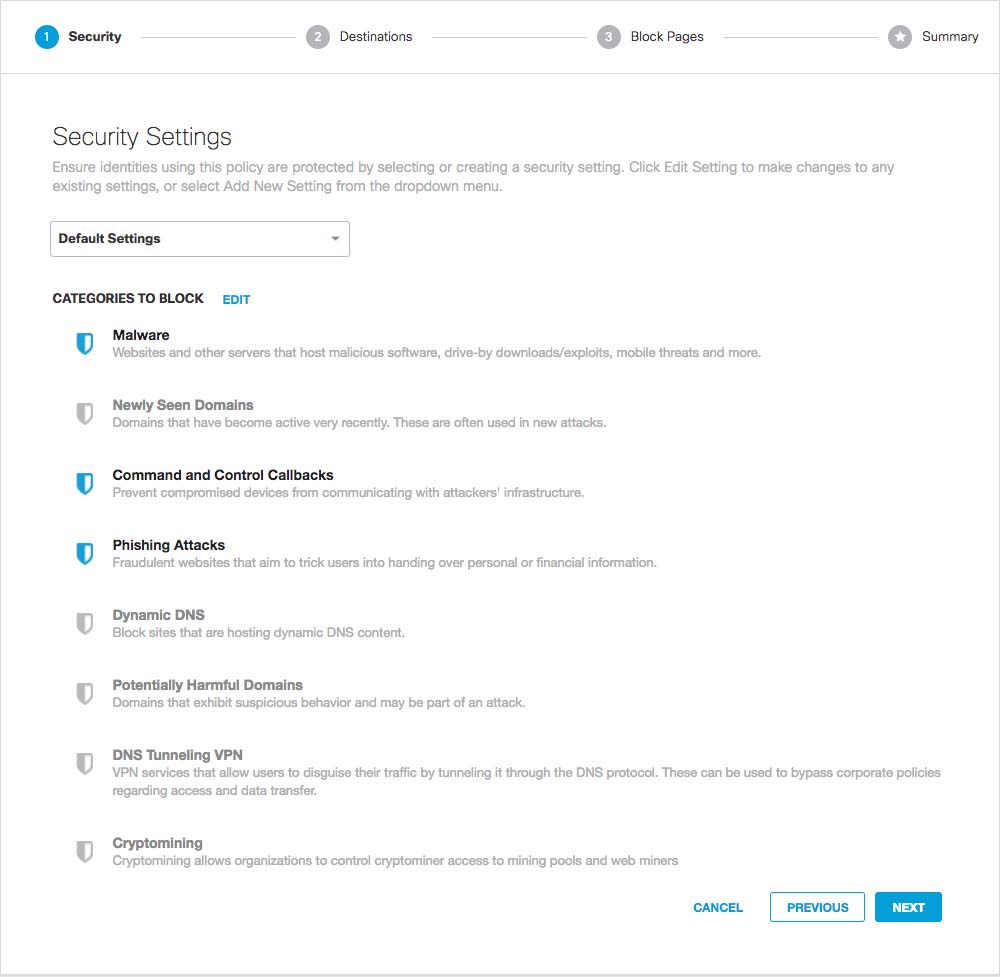
- From the drop-down list at the top of the page, select a previously configured security setting or select Add New Setting to create a new security setting.
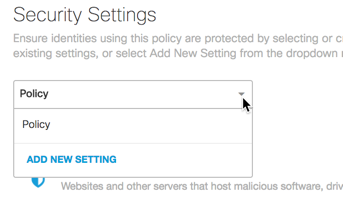
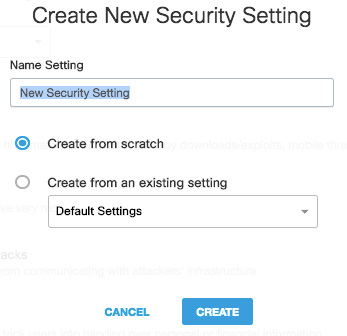
- If you select Add New Setting, in the Create New Security Setting window, give your new setting a meaningful name, select security options and click Create.
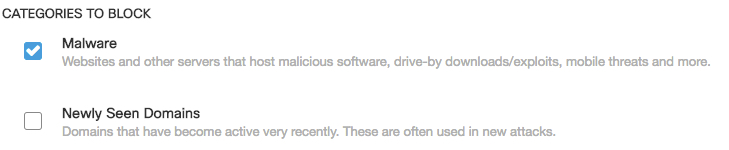
- Optionally, click Edit and select categories to block as needed.
Icons change from shields to checkboxes.
- Once you've configured security settings, click Next.
3. Select Destination Lists
A destination list is a list of internet requests (for example, domain name, URL, or IP address) that is used to manage—block or allow—access to specific internet destinations. When setting up your destination lists, remember that Allow list entries will always take precedence over block list entries. For example:
- Blocking domain.com and adding mail.domain.com to the allowed list will still allow mail.domain.com.
- Adding domain.com to the Allow List and blocking sub.domain.com will still allow sub.domain.com.
- Allowing a domain that has been blocked by either Security or Category settings will also trump those block lists.
- Select destination lists to include in your policy.
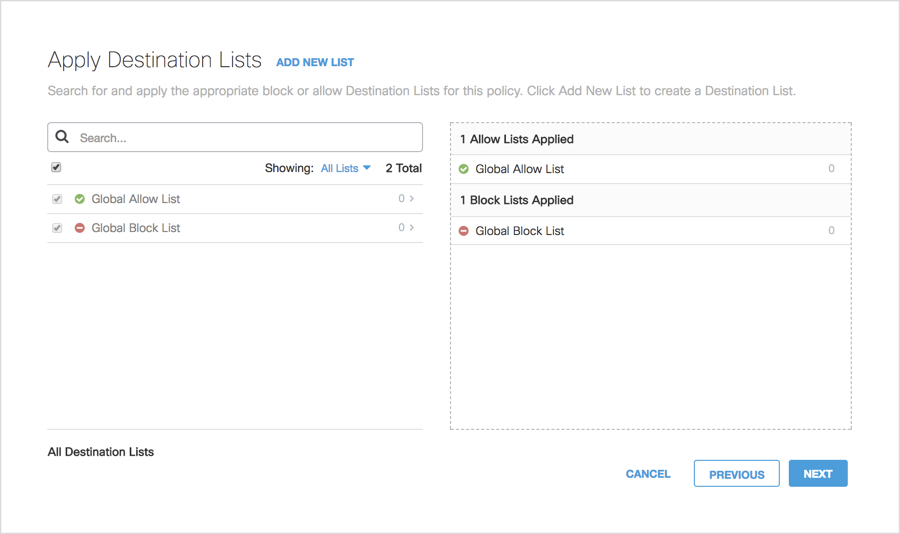
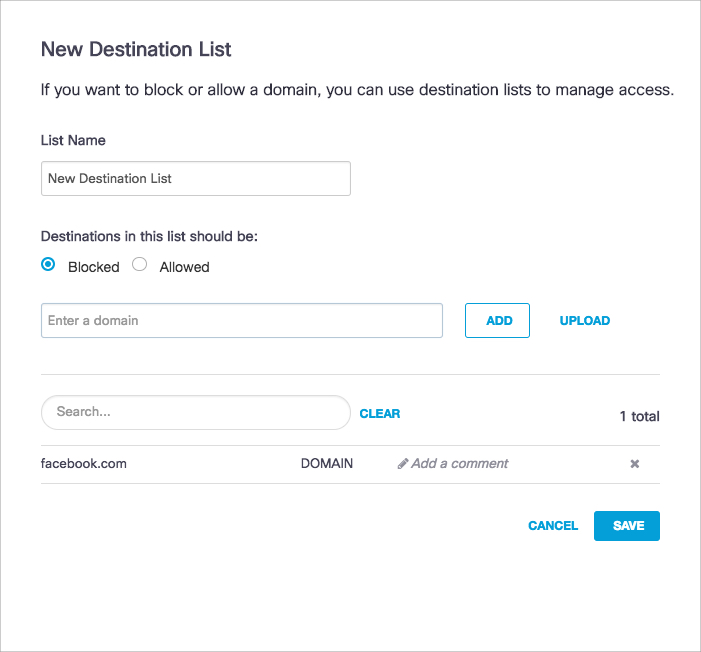
- Click Add New List to create a new destination list.
- Pick the type of list you want, give your list a meaningful name, add the destinations you would like to allow or block, and click Save.
For more information about adding and removing destinations, see How To: Add and Remove Destinations from a Destination Lists.
We recommend adding domains in the format "domain.com" rather than www.domain.com to ensure .domain.com is included (a wildcard is implicit). However, if you only wish to block subdomain.domain.com, then be more specific when you define your destination.
Note: Destinations added to a destination list are not saved until you click Save; although, the destination appears in the list when you click Add.
- Once you have selected your destination lists, click Next.
4. Configure Block Pages
Block Page Settings let you configure a block page that appears when a request is made to access a blocked page. You can customize the block page's appearance and redirect to a custom domain.
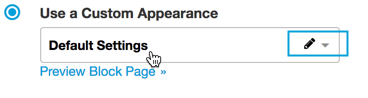
- If you do not wish to change anything, select Use Umbrella's Default Appearance. To create your own block page, select Use a Custom Appearance.
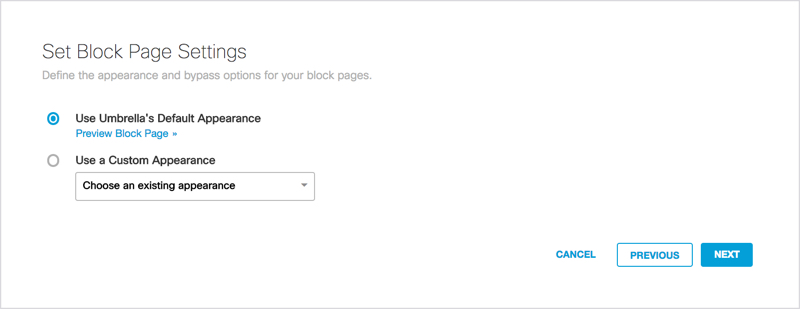
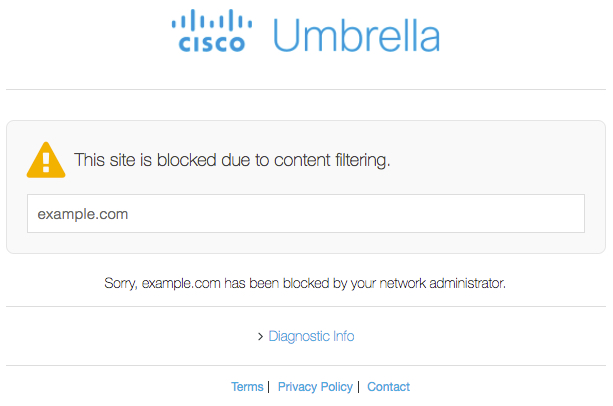
- Click Preview Block Page at any time to see what your Block page will look like. For example:
- You can edit an existing block page by hovering over the name and clicking the Edit pen icon.
- If you select Use a Custom Appearance, select Create New Appearance from the drop-down list.
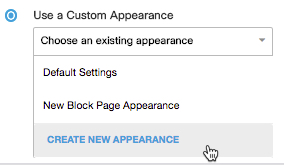
- When you create a new custom block page, first give it an easy to remember name.
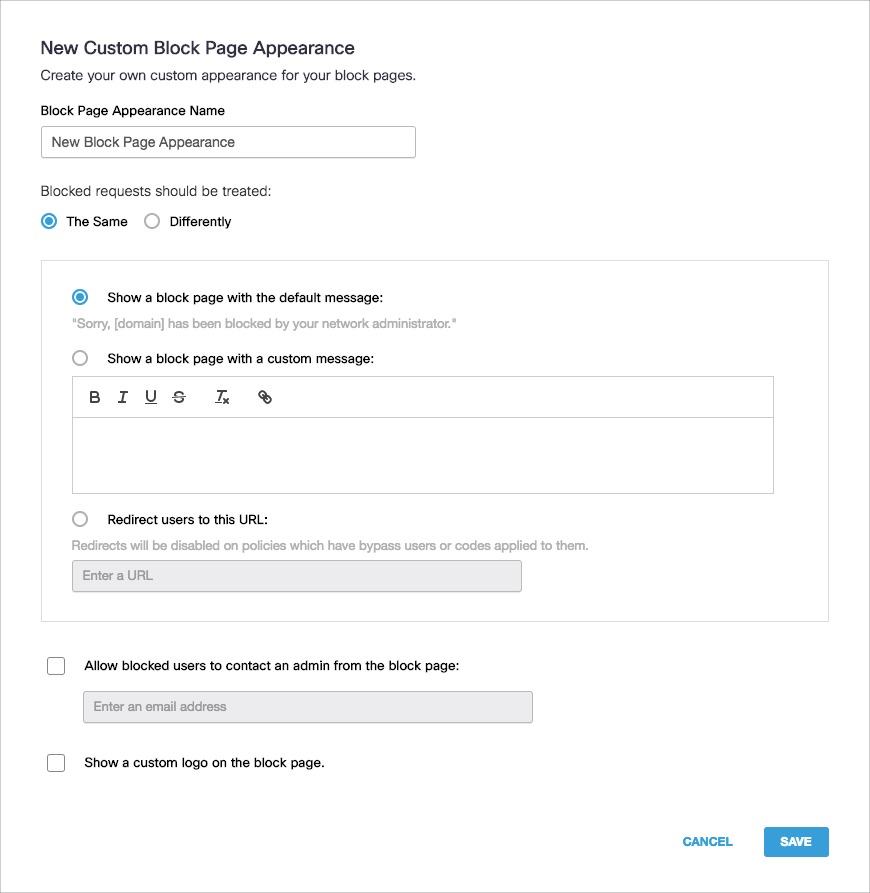
- Choose a generic message that all block pages will use, or customize the message based on the type of block page by selecting whether Blocked requests should be treated The Same or Differently.
If you set a custom message, you may insert the [domain] variable into a custom message, which is substituted with the actual domain name that the end user attempted to browse to. You may also insert the [client_ip] variable, which shows the external IP address of the client that is hitting the block page.
If you set a custom message, you may insert the [domain] variable into a custom message, which is substituted with the actual domain name that the end user attempted to browse to.
The block can also redirect to a custom URL. - If not redirecting to a custom URL, a contact form can be added to allow blocked users to contact the administrator at the email provided.
- Finally, a custom logo can be uploaded to be displayed on the block page in place of the Umbrella logo.
- Click Save.
- Once you've set your block page, click Next.
5. Review and Save Your Policy
Lastly, you'll reach the Policy Summary page. It lists all of the configurations to the policy you just made.
- Give your policy a meaningful name.
- If you want to change anything, click Edit under that setting summary and you'll jump to that setting. Click Disable to disable that setting.
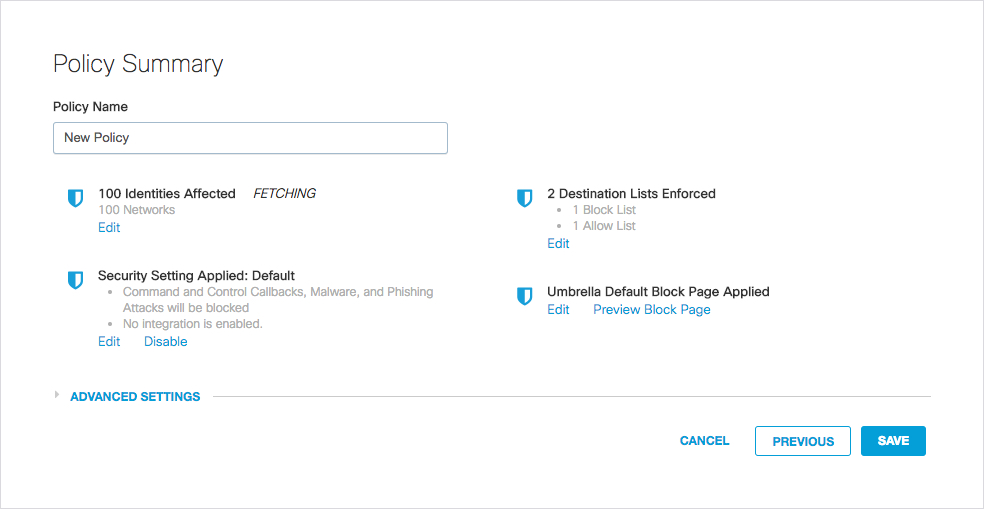
- When you've made the change, click Set & Return.
- You can also modify any advanced settings directly from this page.
- Once you've got everything the way you want it, click Save.
And that's it! Your policy is set. When you open a policy, the Summary page opens, and you can jump between steps in order to make changes without having to redo the entire wizard.
Change Default Policy < Add A New Policy
Updated over 5 years ago
