Enable SSL Decryption
Note: Support for the intelligent proxy is deprecated and only available for legacy deployments of the MSP console. The intelligent proxy is not available for new deployments of the MSP console.
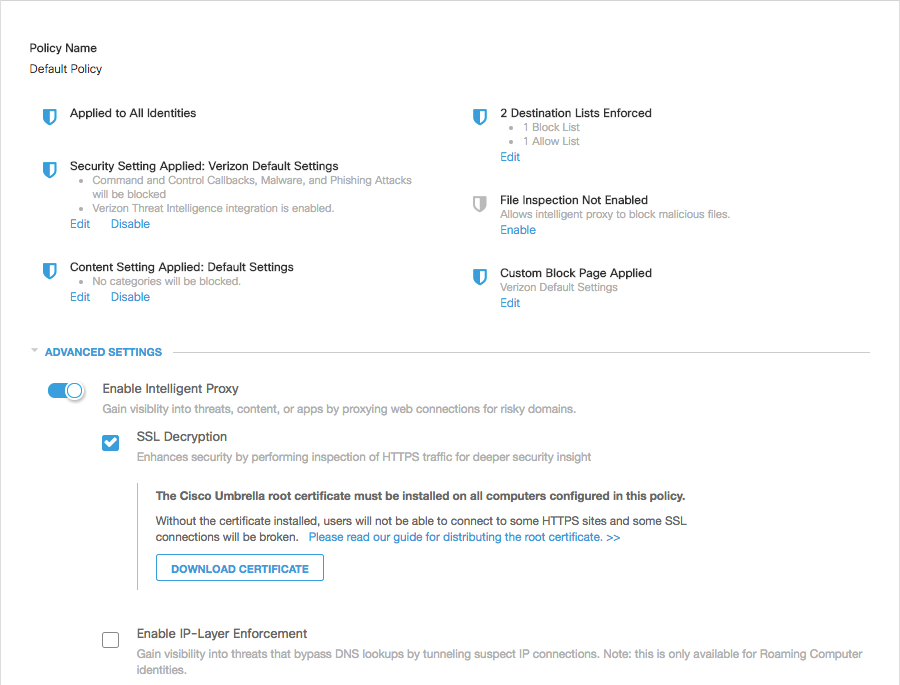
Because SSL decryption is part of the intelligent proxy, intelligent proxy functionality must be enabled first.
- In the Policy wizard, navigate to Step 2, "What should this policy do?".
- Expand Advanced Settings and click SSL Decryption.
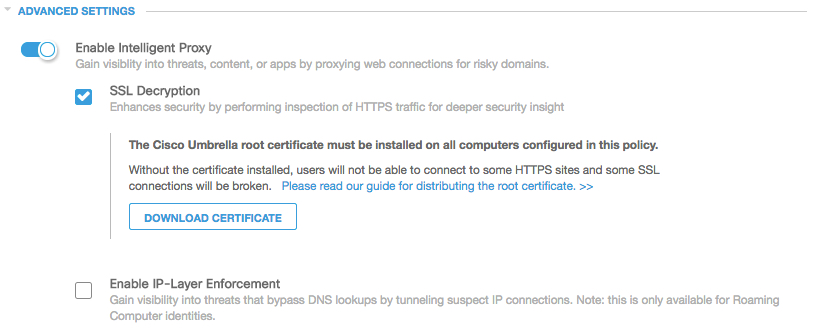
For an existing policy, SSL Decryption can be enabled from the Summary Page by clicking Advanced Settings.
Testing SSL Decryption
Once you’ve deployed the Cisco Root CA to your client machines and configured the feature, you’ll want to confirm it is working. We’ve created the following URL to allow you to test this:
https://ssl-proxy.opendnstest.com
This leads to a page advising if your request was successfully proxied or not.
What is being decrypted and proxied?
Some solutions, such as deep packet inspection solutions on the gateway of a network, will inspect all of the traffic sent through at it a granular level to look for information, such as strings of malicious code, or confidential information. This is not what the SSL decryption for the intelligent proxy does, instead, this is really just the intelligent proxy for SSL websites. The only thing that is being inspected are the requested URLs and domain names that are considered suspicious to begin with and are on our 'grey list', and we will block HTTPS URLs if they're considered malicious in our ruleset. We are not recording (or even looking) at anything beyond the URLs, possibly malicious files (and checksums) and the domain names themselves.
If File Inspection is enabled, then our proxy also inspects files attempted to be downloaded from those risky sites using anti-virus (AV) engines and Cisco Advanced Malware Protection (AMP), providing comprehensive protection against malicious files. Having SSL Decryption enabled along with File Inspection protects against sites using valid HTTPS but serving malicious files along with innocuous ones.
Reporting and the Intelligent Proxy < Enable SSL Decryption
Updated about 6 years ago
