Add IP Layer Enforcement
Note: IP Layer Enforcement is not available to all Umbrella packages. If you encounter a feature described here that you do not have access to, contact your sales representative for more information about your current package. See also, Cisco Umbrella Packages.
IP Layer Enforcement requires that a version 2.0.1 (or above) of the Umbrella roaming client be available to your organization before the feature can be enabled, both for Mac and Windows. If Umbrella roaming clients are not automatically upgrading to this version, they may be offline or the installation may be broken.
Table of Contents
- Overview
- Prerequisites
- Enable IP Layer Enforcement for the Umbrella Roaming Client
- Test to Ensure IP Layer Enforcement is Functional
Overview
Cisco Umbrella already provides some of the most advanced threat protection and predictive security in the world but there are times when malware authors will use an IP address instead of a fully qualified domain name to host their malware. Since Umbrella protects against malicious domains and URLs primarily, we saw this as an area we needed to address.
Malware authors might use IP addresses that bypass DNS lookups when creating a threat. For instance, one of your users might receive a phishing email with a URL that has an IP address in it, eg: http://x.x.x.x/malware.exe while they're not in your office and protected by your firewalls. Or, a user may go home, insert an infected USB stick into their computer to look at their children's homework, and execute malware that contacts http://x.x.x.x:3000/malicious/bad.exe.
Normally, malware authors use domain names and not IP addresses. There's a good reason for that: IP addresses that host malware are quickly blocked or taken down by the ISP that owns them, but a domain name can always resolve to a new IP address. However, there are exceptions and we recognize that in order to provide the best possible security coverage, we'd need to block IPs in certain circumstances. Some IP addresses are simply known to be bad. Other IP addresses may host valid content on non-HTTP ports, while the web ports host malicious content. The inverse is also true; IP addresses can host legitimate HTTP websites but also host malicious command and control hosts on a non-standard port. The IP Layer Enforcement feature handles all of these scenarios.
Note: IP Layer Enforcement is only available for IPv4.
Prerequisites
- The Umbrella roaming client for Windows or Mac should be installed and functional, showing encrypted and protected in the local UI and in the Umbrella dashboard, running version 2.0.1+ for both Windows and Mac OS X.
- Compatible versions of Windows: 7, 8, 8.1 and 10
Note: Umbrella IP Layer Enforcement is compatible with Windows 10 version 1511 or later. If IP Layer Enforcement does not work, it would fail gracefully—network connectivity and DNS Layer protection will not be affected. - Incompatible versions of Windows: Windows XP, Vista
- Supported versions of MacOS: 10.11.6 and above.
IPv6 Support
Currently, the Umbrella roaming client only supports dual stack IPv4/IPv6 for the Mac OS. Stand alone support for IPv6 for both the Mac and Windows operating systems is not supported. For more information, see Umbrella Roaming Client: IPv6 Support.
- If the Umbrella roaming client is behind a virtual appliance (VA), the policy applied to the Umbrella roaming client will come from the VA identity rather than the policy for the Umbrella roaming client identity and testing will be difficult. For more information, please see the next section of this guide.
- Internet Protocol Security (IPSec) traffic must be allowed through firewalls. The following ports and protocols must be allowed:
- Protocol 50 (ESP)
- Protocol 51 (AH)
- UDP Port 500
- UDP Port 4500
IPSec uses IP protocol 50 for Encapsulated Security Protocol (ESP), IP protocol 51 for Authentication Header (AH), and UDP port 500 for IKE Phase 1 negotiation and Phase 2 negotiations. UDP port 4500 is also used.
To restrict IPSec to only the Umbrella servers providing malicious IP blocking, allow ESP, AH, UDP Port 500 and UDP Port 4500 to these IP ranges only:
67.215.82.0/23 67.215.84.0/23 67.215.86.0/24 204.194.237.0/24 204.194.238.0/23 208.67.216.0/23 204.194.239.0/24 208.69.32.0/22 208.69.36.0/23
If you would like to simply allow access to all of the Umbrella ranges used:
67.215.64.0/19 204.194.232.0/21 208.67.216.0/21 208.69.32.0/21
Note: A full list of the exact IP addresses—not just the ranges—can be found in a text file you can download here.
Enable IP Layer Enforcement for the Umbrella Roaming Client
Note: Inspect Files is only available with the Cisco Umbrella for MSPs Advanced package. For more information, see Enable File Inspection.
- Navigate to Centralized Settings > Advanced Settings and click Add A Setting or expand an existing setting.
- Toggle Enable Intelligent Proxy.
- Check Enable IP-Layer Enforcement.
- Click Next until you can Save.
Test to Ensure IP Layer Enforcement is Functional
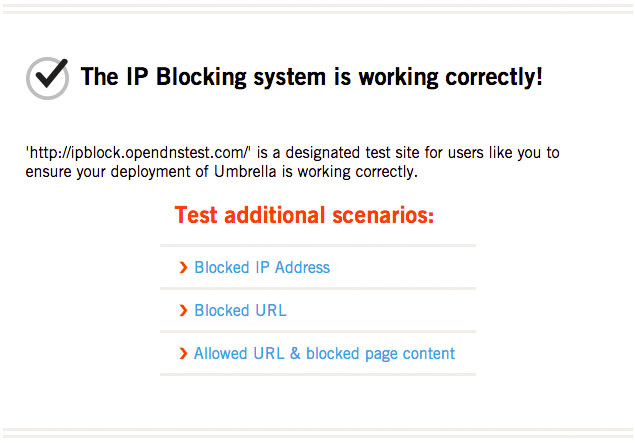
To test whether you're blocking malicious IPs with the IP Layer Enforcement, we've set up a test page at: http://ipblock.opendnstest.com/
This page displays correctly when the feature is enabled and working for the Umbrella roaming client installed on the computer. Feel free to test the additional scenarios to get a sense of how the feature will behave when blocking a malicious IP address.
If things are not working as expected or the feature is not enabled on the Roaming Computer that you're testing with, this is what you will see:
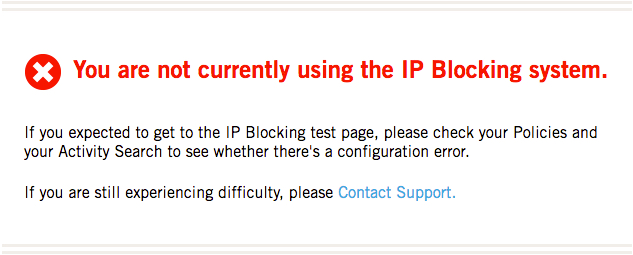
If your policy is correctly configured as best as you can determine and the test page is still not reflecting that IP Layer Enforcement is enabled, this could be because the policy applied to this Roaming Computer does not have the IP Layer Enforcement feature enabled. Double-check the order of policy precedence for this identity in the dashboard.
To start troubleshooting, it's worth checking to ensure these outbound ports are set to allow encrypted DNS requests to be routed through the Umbrella Global Network:
- Port 53 TCP/UDP to opendns.com
- Port 443 TCP to opendns.com
Double-check the system requirements for this feature and ensure they've been met.
If problems persist beyond this point, or if there are any unexpected or unusual behaviors when the IP Layer Enforcement feature is enabled, we'd like to hear about it. Please e-mail us at [email protected].
Verify Operation < Add IP Layer Enforcement > Frequently Asked Questions
Updated about 6 years ago
