Configure Okta for SAML
Okta for SAML configuration can be authenticated in one of two ways: By uploading the identity provider's (IdP) metadata file or by manually configuring with specific IdP fields. For provisioning Okta after configuration, see Provision Identities from Okta.
Table of Contents
Prerequisites
- id.swg.umbrellagov.com must be sent to the Umbrella secure web gateway (SWG) and not sent directly to the internet.
- SAML metadata must have a signing key.
- Ensure that your IDP Endpoint (the URL used to communicate with your identity provider) bypasses the Umbrella proxy to avoid an authentication loop.
- Configure SAML with your identity provider (IdP) that supports SAML 2.0 POST profiles.
- Download your IdP's metadata file in XML format.
- Enable cookies for your browser.
- Enable SAML and HTTPS inspection on a Ruleset that includes the Network and Tunnel identities from which the user traffic arrives.
Configure Okta for SAML with Metadata Upload
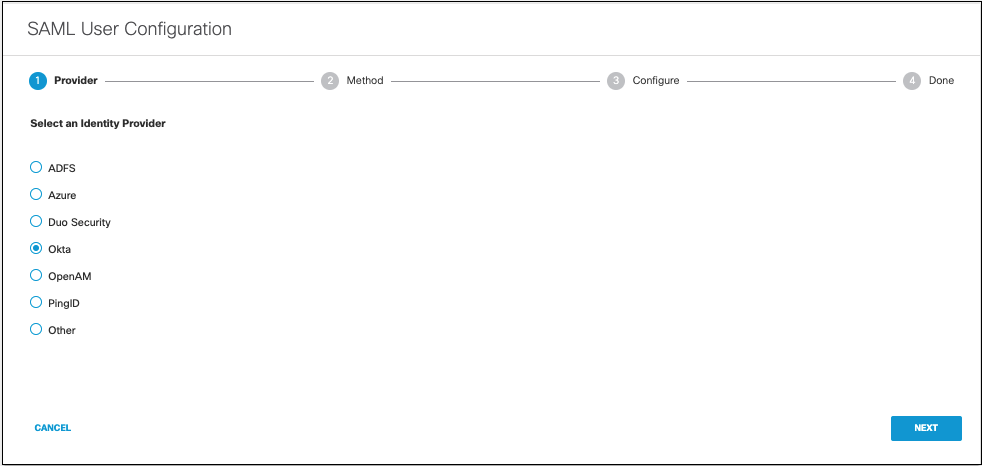
- Navigate to Deployments > Configuration > SAML Configuration and click Add.

- Select Okta and click Next.
- Select XML File Upload.
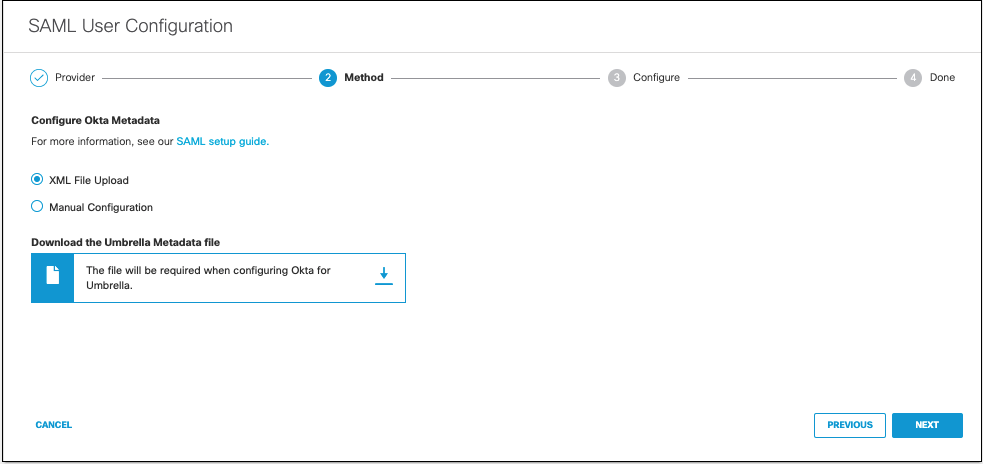
- Download the Umbrella metadata file (SP metadata file) and click Next.
Do not use the Cisco Umbrella application within Okta.
This application is designed for the Umbrella dashboard and not for Secure Web Gateway users. You must configure Umbrella as a generic SAML 2.0 application within Okta. Okta does not provide a method to upload Umbrella metadata for automatic configuration. Extract the EntityID and AssertionConsumerService URLs from Umbrella metadata and add these to the applicable fields in Okta. Contact Okta support for assistance.
The Umbrella SP metadata includes the Service Provider Issuer ID, the assertion consumer endpoint URL information, and the SAML request signing certificate from Cisco Umbrella. This metadata is required when configuring your IdP for Umbrella.
Note: Your IdP must send the Cisco Umbrella User Principle Name in the NameID attribute in the SAML assertion. For more information on configuring your IdP, exporting your IdP metadata, obtaining your IdP details, or downloading your IdP signing certificate, refer to your vendor's documentation.
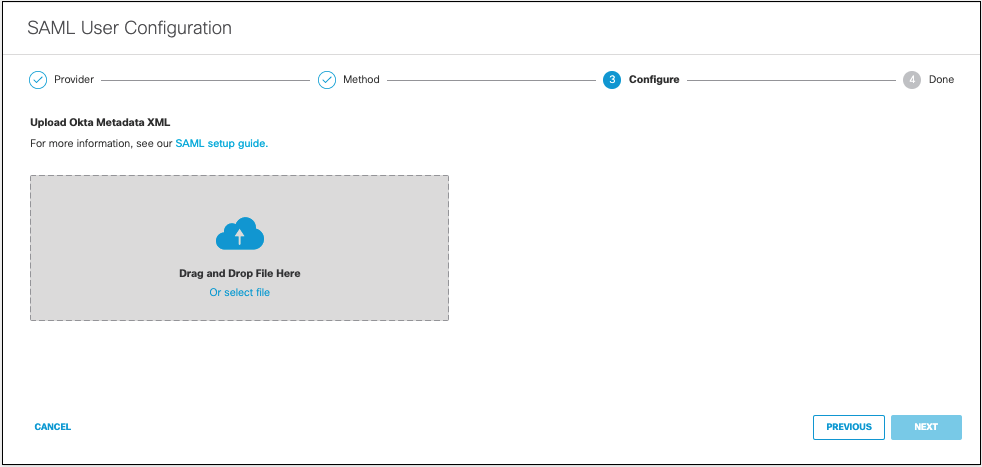
- Upload your IdP's metadata file in XML format and click Next.
- From the Re-Authenticate Users drop-down list, choose how often Umbrella re-authenticates users: * Daily, Weekly, or Monthly.
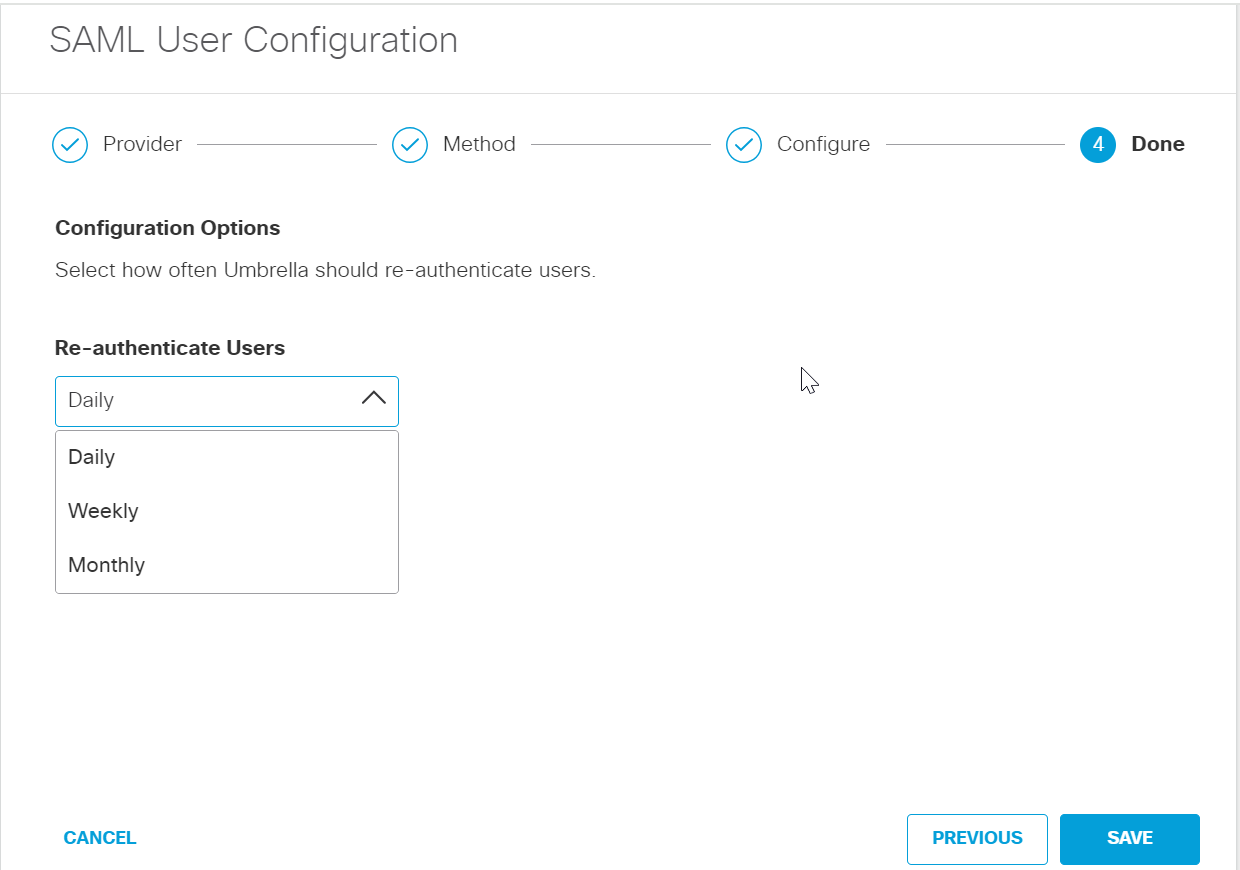
- Click Save. Your new configuration appears as SAML Web Proxy Configuration.
Configure Okta for SAML Manually
- Navigate to Deployments > Configuration > SAML Configuration and click Add.

- Select Okta and click Next.

- Select Manual Configuration.
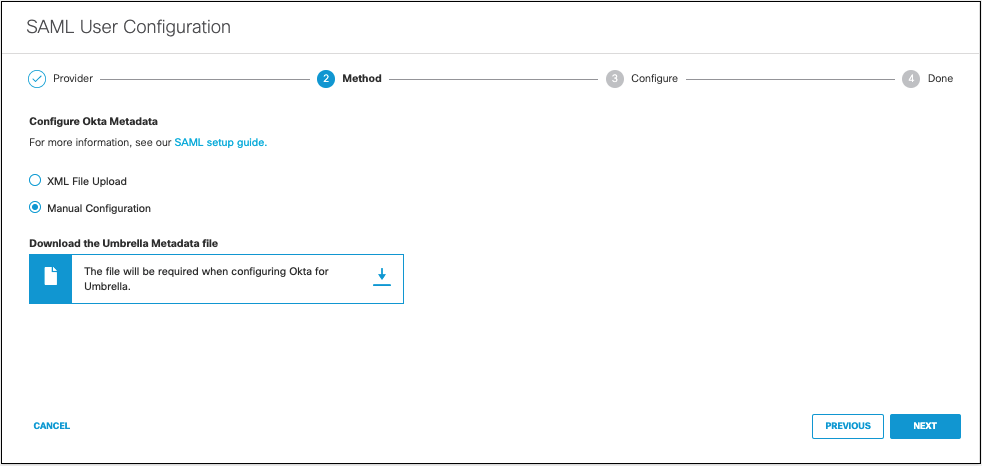
- Download the Umbrella metadata file (SP metadata file) and click Next.
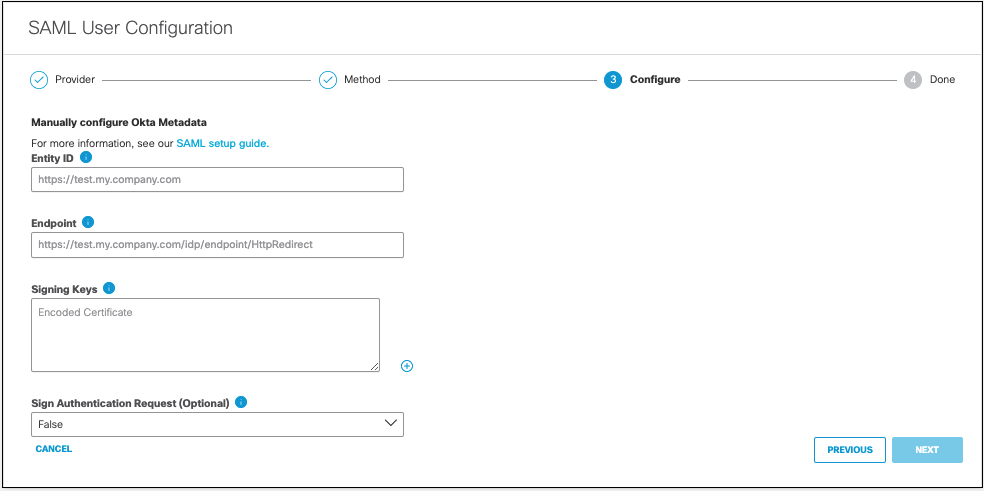
The Umbrella SP metadata includes the Service Provider Issuer ID, the assertion consumer endpoint URL information, and the SAML request signing certificate from Cisco Umbrella. This metadata is required when configuring your IdP for Umbrella. - Enter the appropriate information to configure Okta's provider metadata and click Next.
- Entity ID—A globally unique name for an identity provider
- Endpoint—The URL used to communicate with your identity provider.
- Signing Keys—Your identity provider’s x.509 certificate used to sign the authentication request.
- Signed Authentication Request (optional)—You can sign the authentication request for this IdP.
- From the Re-Authenticate Users drop-down list, choose how often Umbrella re-authenticates users: Daily, Weekly, or Monthly.
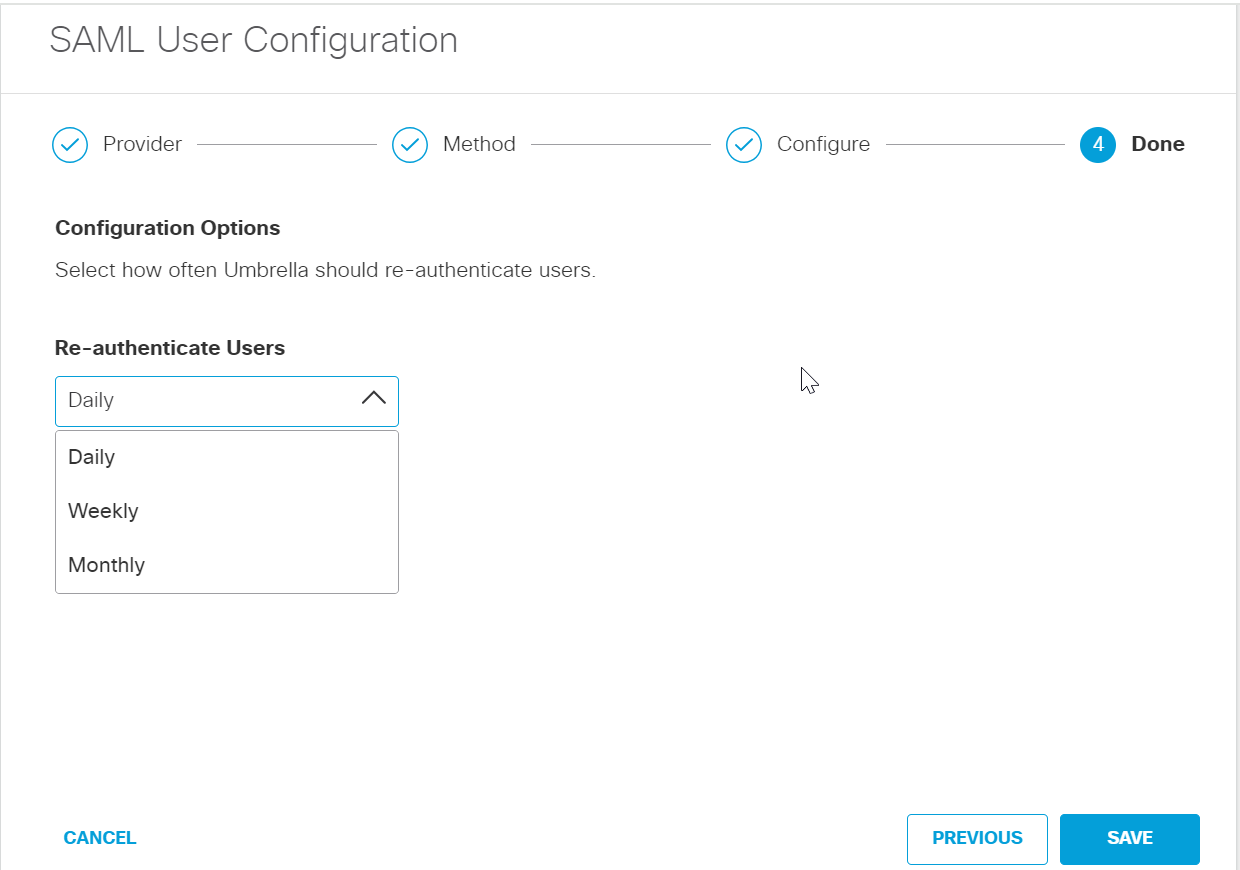
- Click Save. Your new configuration appears as SAML Web Proxy Configuration.
Configure Azure AD for SAML < Configure Okta for SAML > Configure AD FS for SAML
Updated about 1 year ago
