Deployment Guidelines
For the vast majority of deployments, at a high level, an Umbrella virtual appliance (VA) configuration is as follows:
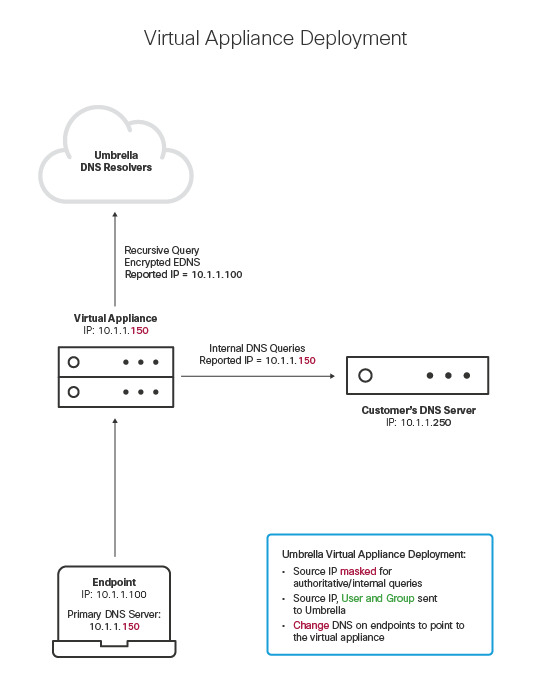
Note: Internal Domains must be configured correctly, and endpoints must be using the VA as the primary DNS server. Two VA are required for high availability.
Virtual Appliance Deployment Best Practices
Redundancy
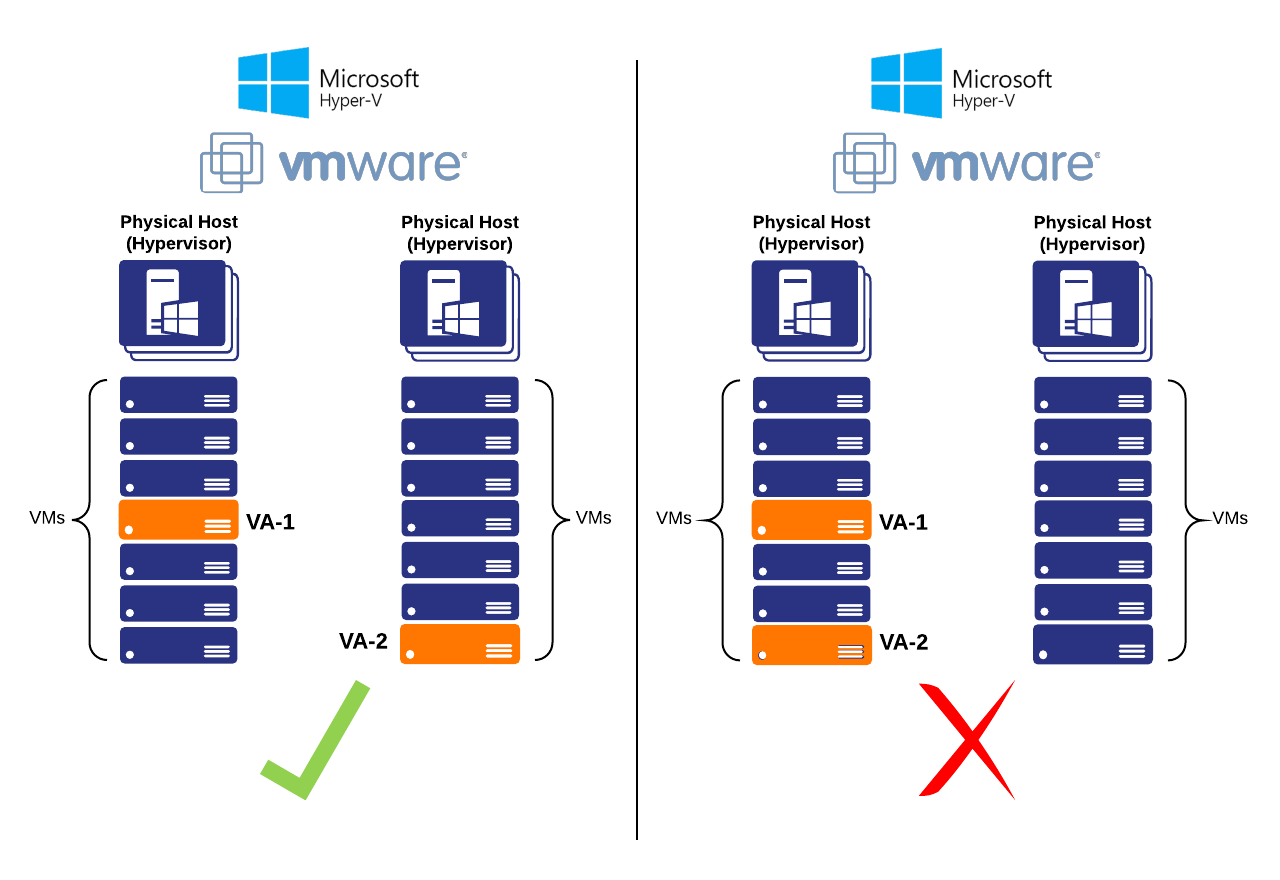
VAs must always be deployed in pairs. Running two or more VAs offers high redundancy in case of system updates. This ensures that there is no interruption in Internet service during an update, and allows you to schedule updates for scheduled maintenance windows or off-hours. See Importance of Running Two VAs.
Whenever possible, deploy VAs on separate physical hypervisor hosts. If a hypervisor hosting a VA becomes unavailable, the second VA will continue serving DNS requests without interruption.
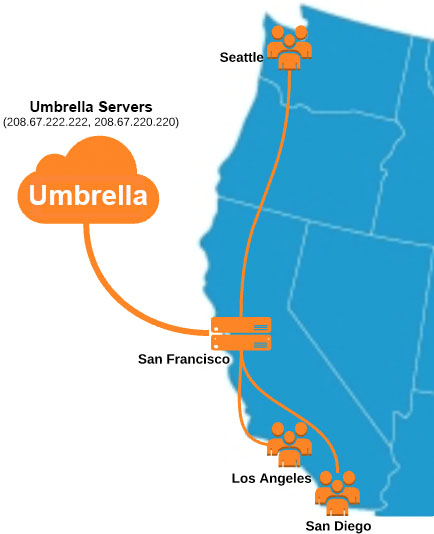
Multiple DNS Egresses
In most cases where multiple offices or points of presence exist, each office sends and receives its own DNS traffic. As seen below, four offices are independently sending DNS queries directly to Umbrella.
In this case, each office requires their own pair of VAs.

This diagram represents the necessity for deploying VAs at multiple offices. When using Cisco Umbrella, DNS queries will always route to the closest Umbrella data center.
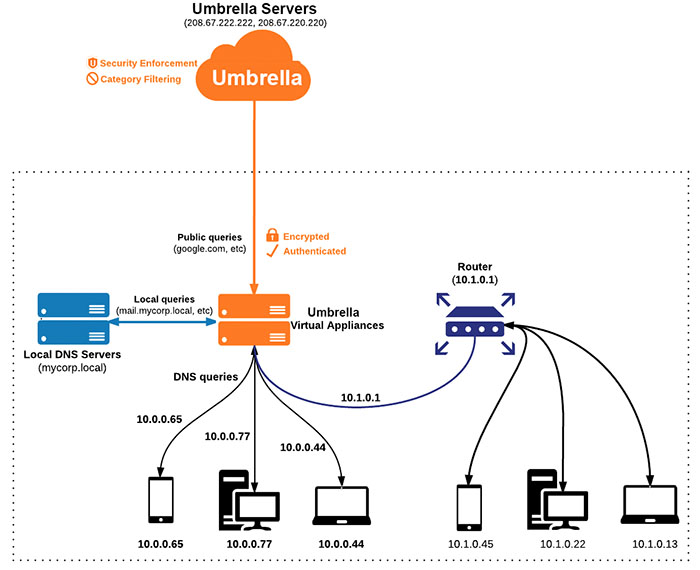
Single DNS Egress
In some cases, especially if the networks are geographically close to one another, a single egress may handle all DNS traffic originating from multiple networks. This topology is typically used to route traffic through security appliances, Active Directory Domain Controllers, or other network and security devices at a central location to avoid deploying and managing them at every location. This is usually accomplished with a Site-2-Site VPN or an MPLS circuit.
In this case, only the office which sends and receives public DNS queries requires Virtual Appliances.
Double NAT
Endpoints residing behind a separate Network Address Translation (NAT) from that of the VAs will result in the VAs seeing the IP address of the NAT device itself.
A double NAT situation is not advisable with the VAs, as it limits both the ability to create granular policies and endpoint-level reporting in the Umbrella dashboard. However, you can still create a separate policy for the NAT IP address, which would be useful for Guest Wi-FI situations, where knowing the endpoint IP address may not necessarily be helpful, but having a separate policy for that group of endpoints is important.
Prerequisites < Deployment Guidelines > Importance of Running Two VAs
Updated about 1 year ago
