Top Threats Report
The Top Threats report highlights threats your organization may have been exposed to over a set time and whether they were blocked or allowed.
When no new threats are detected in the set time, a notification appears in the Threat Activity Breakdown.
Note: Not all threats identified by Umbrella have a corresponding threat type. You may see activity blocked under Security Activity but not see anything blocked under Top Threat Types. This is normal when a threat does not currently have a threat type associated with it.
Table of Contents
- Prerequisites
- View the Threats Report
- View Top Threat Types in the Threat Activity Breakdown
- View How Threats Impact Your Environment
- Search for Threats in Activity Search
Prerequisites
- A minimum of Read Only access to the Umbrella dashboard. See Manage User Roles.
View the Threats Report
- Navigate to Reporting > Core Reports > Top Threats.
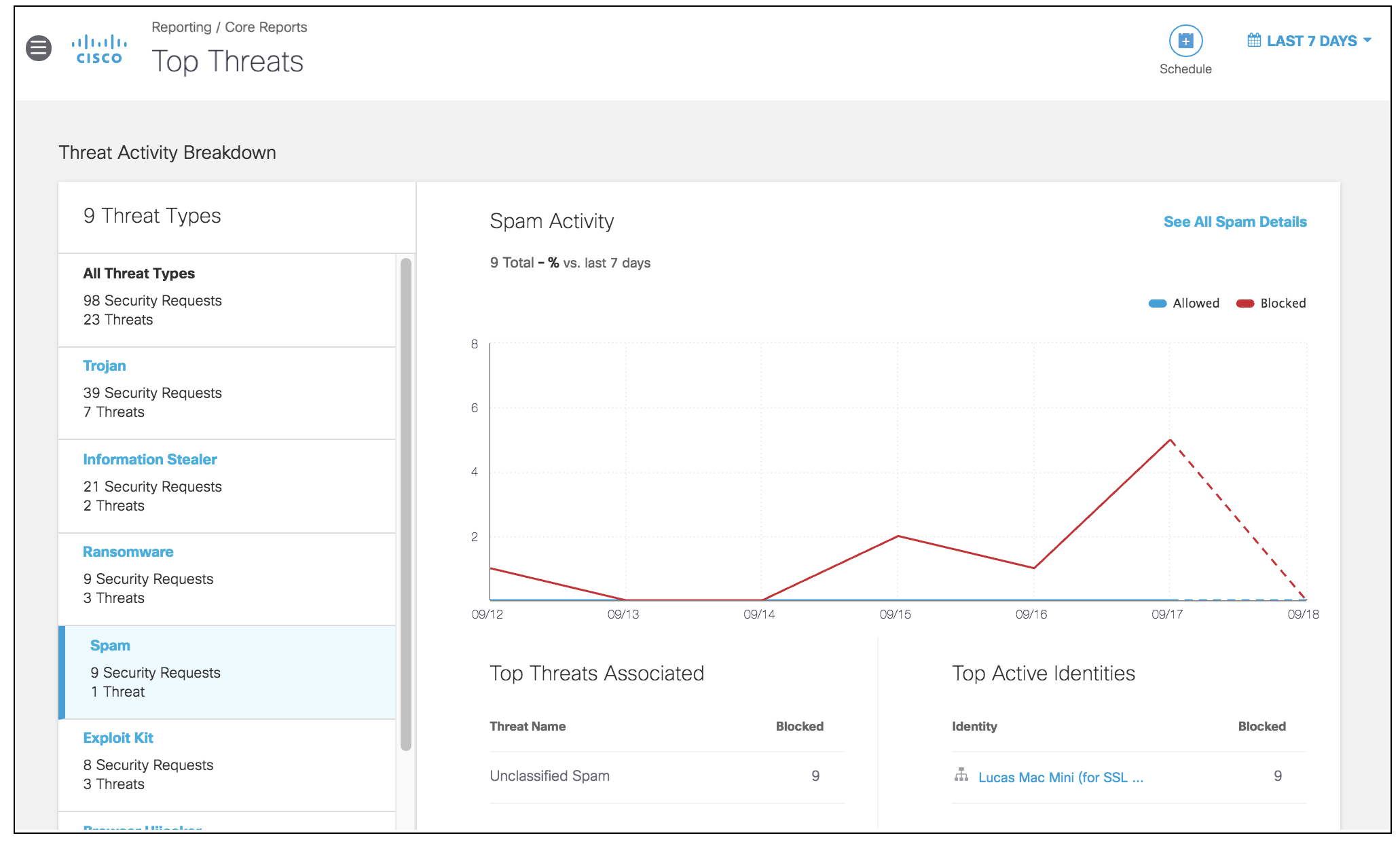
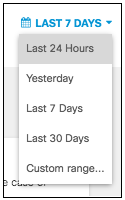
- Select a time frame to view the results of the report.
You can select results for the last 24 hours, the previous day (yesterday), the last week, the last 30 days, or a custom range within the last 30 days.
View Top Threat Types in the Threat Activity Breakdown
The Threat Activity Breakdown enables you to assess the top threat types and their activities over a selected time period. The breakdown provides an overview of the top threat types and activities, but you can also select individual threat types to see their activities and associated threats.
- Navigate to the Threat Activity Breakdown.
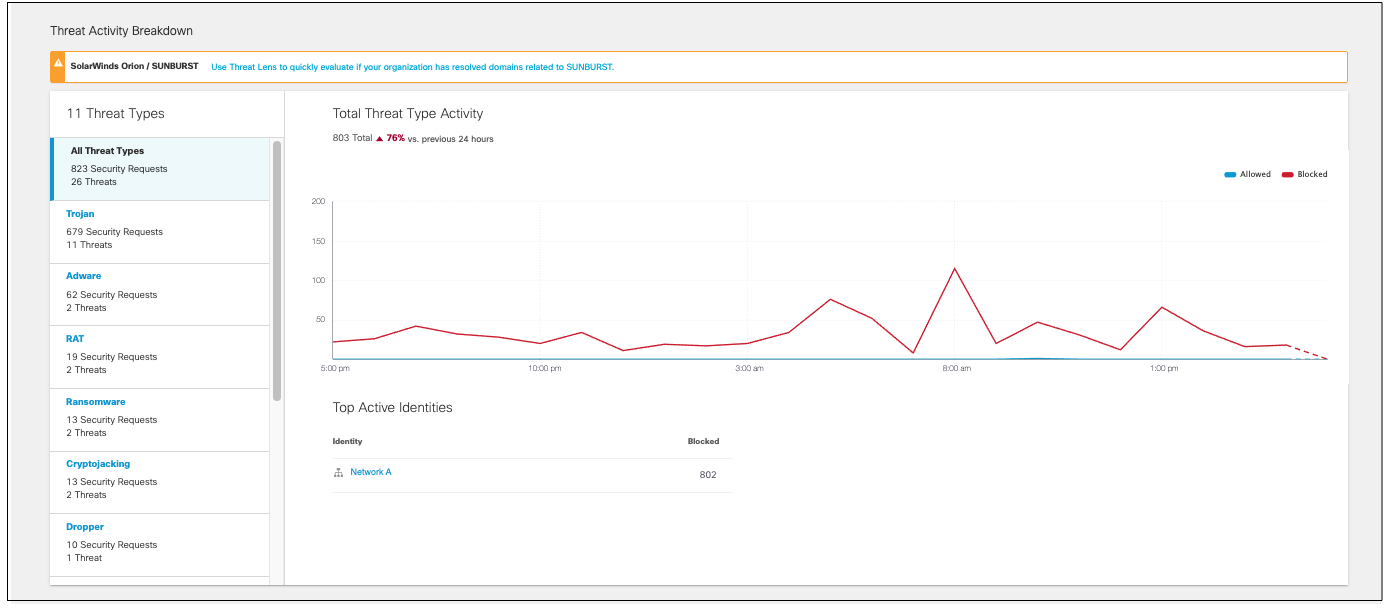
- Choose a threat type from the left to view only data for that threat type.
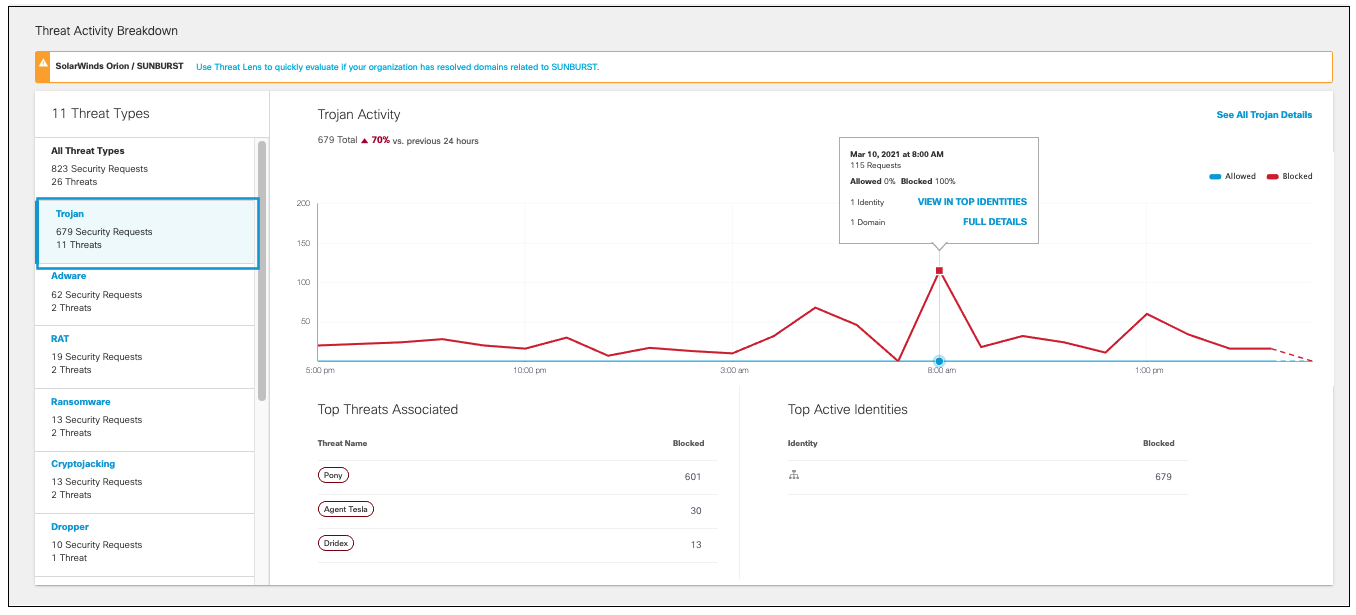
- Choose to view all data, only Blocked threats, or only Allowed threats. By default, both allowed and blocked are shown. Click either name to hide those threats in the graph.
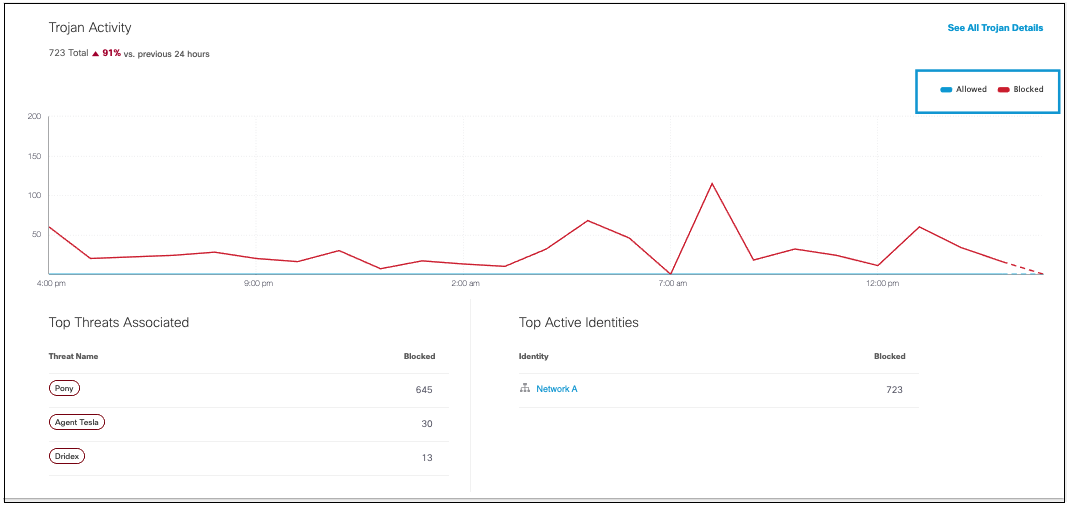
- Click on any point on the graph to view information about allowed or block threats for that date and time.
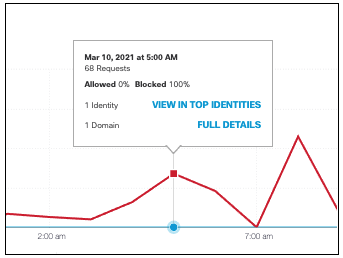
Click View in Top Identities for details about the identities involved, or Full Details to see more information for that threat type for the selected date range.
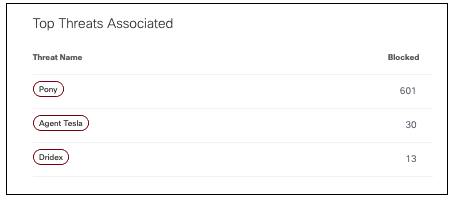
- View the top threats associated and blocked with this threat type. Clicking on a threat name will bring you to its details.
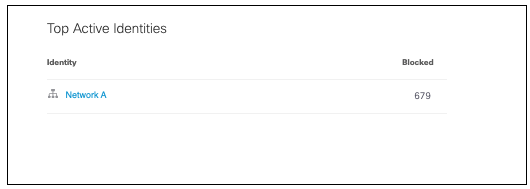
- View the identities most active with this threat type and the number of blocked threats for each identity.
View How Threats Impact Your Environment
- Navigate to Reporting > Core Reports > Top Threats > Impact.
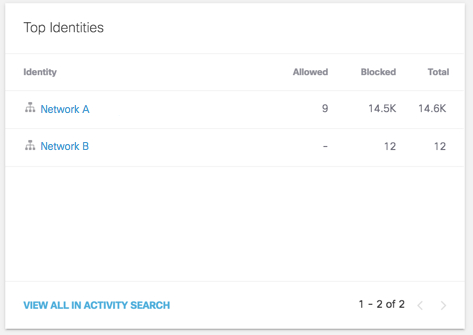
- View the identities with the most threats.
The chart lists the identities, the total threats associated with that identity for the time frame, and how many threats were blocked and allowed.
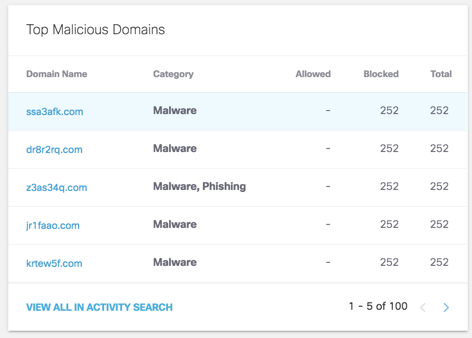
- View the top malicious domains.
The charts lists the domains where threats are most prominent, the threat category associated with
the domain, and the number of blocked and allowed requests.
Click on an identity's name or View in Activity Search to view details in the Activity Search with the appropriate filters.
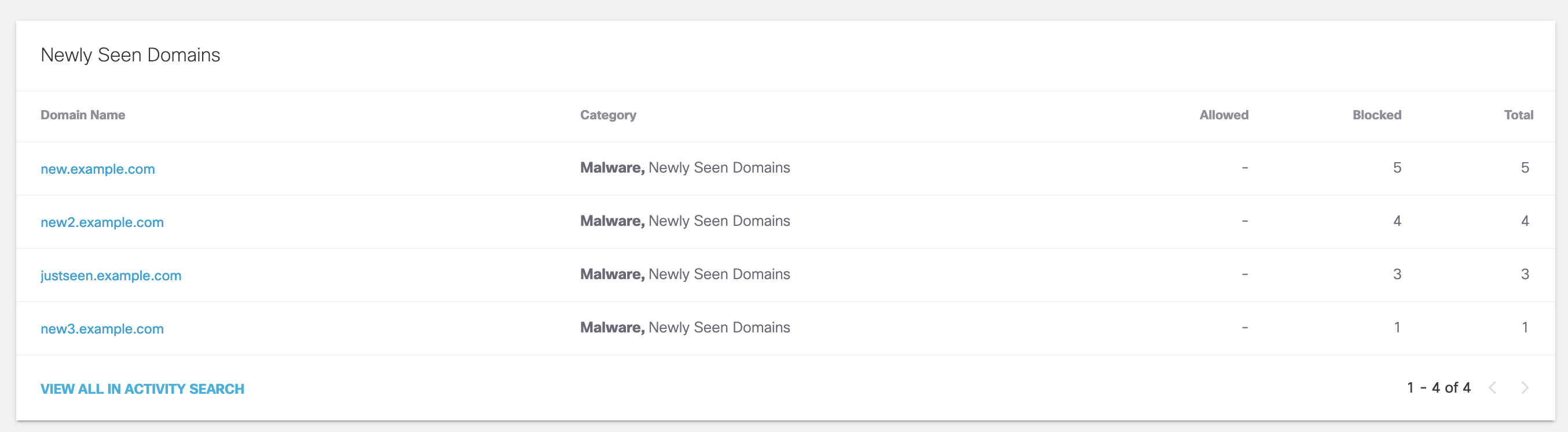
- View domains that have recently been seen by Umbrella's resolvers for the first time, and whether they've been allowed or blocked.
Newly Seen Domains are not blocked by default. To learn more about the Newly Seen Domains category, see Newly Seen Domains Security Category.
Search for Threats in Activity Search
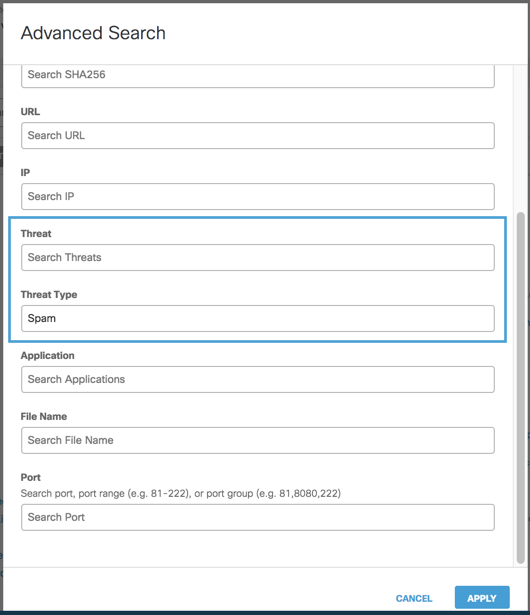
- Navigate to Reporting > Core Reports > Activity Search.
- In the search field, click Advanced to open more options for searching in Activity Search report. You can search by Threat and Threat Type.
Block Apps < Top Threats Report > Threat Type Details
Updated almost 2 years ago
