Status, States, and Functionality
Table of Contents
- Status in the Umbrella Dashboard
- Roaming Computer Information
- Tray Icon Status
- Probes
- Advanced: Network Access per Service
The status of the Cisco Umbrella roaming client—which displays the current state of the Umbrella roaming client—is shown both in the Umbrella dashboard at Deployments > Core Identities > Roaming Computers and on the local machine through the roaming client's tray icon. For detailed descriptions, see Roaming Computer Information and Tray Icon Status.
The state that the Umbrella roaming client operates in depends on the current networking environment. This state determines how the Umbrella roaming client behaves and determines which Cisco Umbrella policy should be applied. The state of the Umbrella roaming client determines:
- Which Umbrella policy to enforce
- DNS settings
- If DNS encryption is possible.
Probes
Probes are frequent DNS requests performed by the Umbrella roaming client that acts as a health check and analysis of the networking environment. For more information, see Probes.
Status in the Umbrella Dashboard
- Navigate to Deployments > Core Identities > Roaming Computers.
Status is displayed for each deployed roaming client through an icon and adjacent status information.
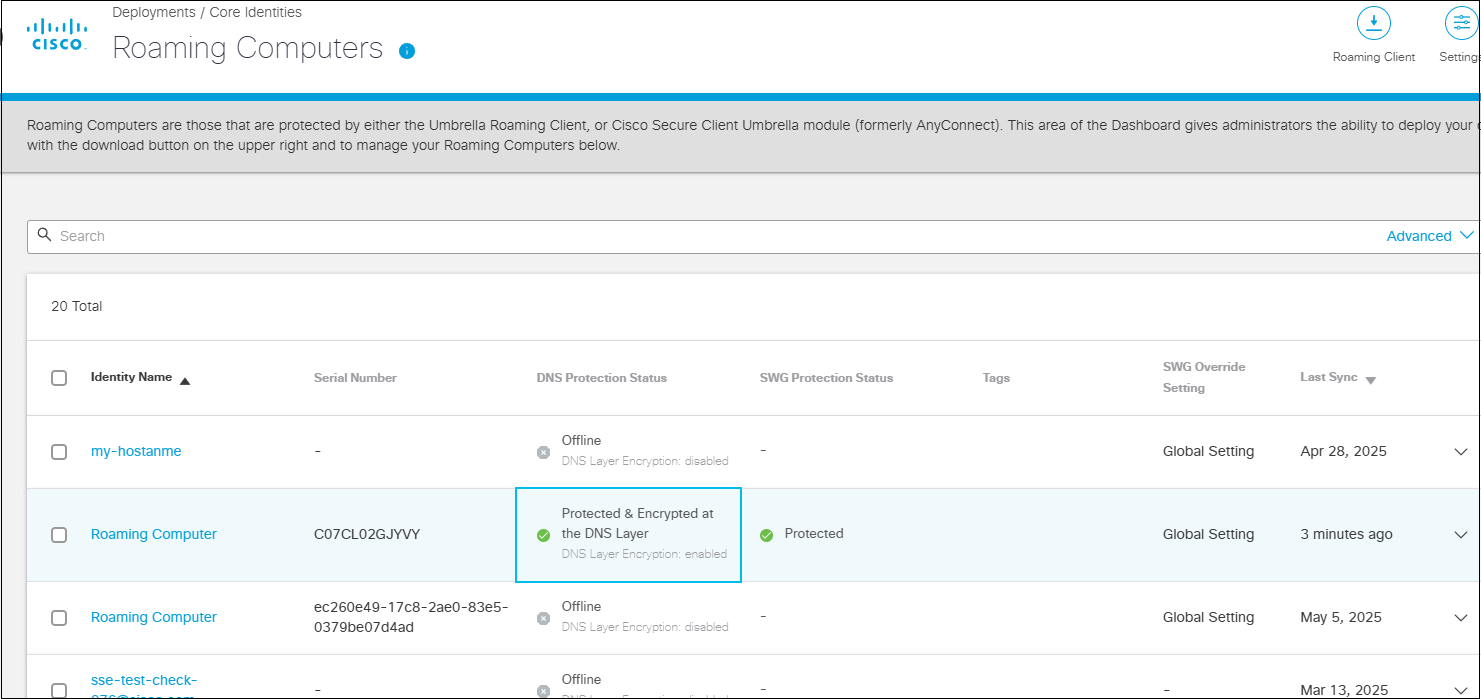
- Expand a roaming computer to review additional information. See also Roaming Computer Information.
- Click Delete to remove the roaming client from the list of machines managed by your organization.
When you delete an Umbrella roaming client from Umbrella while it's still installed on an end-user machine, depending on the version installed it will either re-register automatically or the user will lose all security features and internal domains functionality. To avoid this, Uninstall the Umbrella roaming client from the machine before deleting it from Umbrella. For more information, see Deleting the Umbrella Roaming Client from the Umbrella Dashboard.
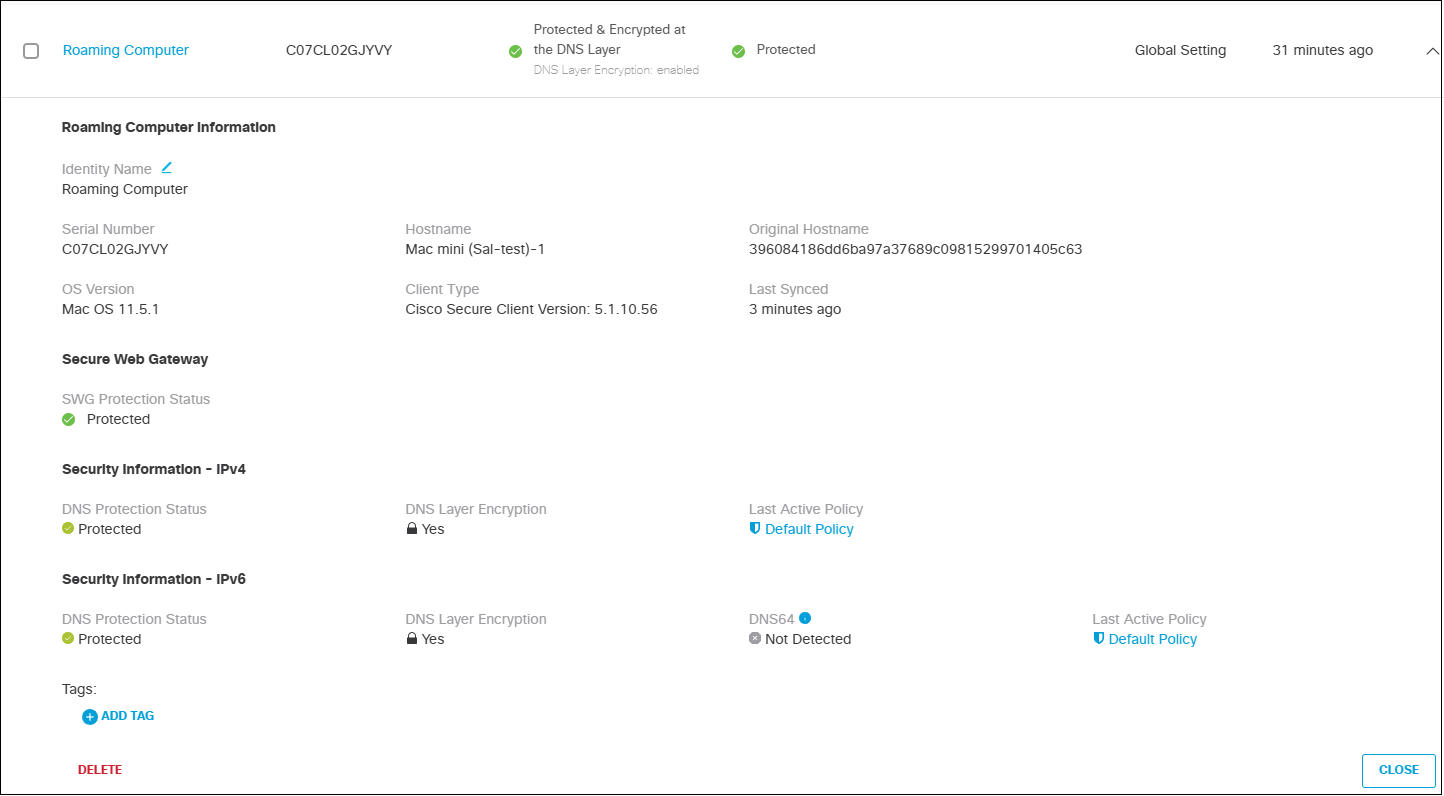
Roaming Computer Information
The Roaming Computer page lists roaming computer information, including security status, for every roaming computer you add to Umbrella.
| Roaming Computer Information | Description |
|---|---|
| Identity Name | The name of the roaming computer as it is listed on the Roaming Computer page and when adding identities to policies. Most often the hostname of the computer. You can change this name at any time. |
| Client Type | The currently installed version of the Umbrella roaming client: AnyConnect or Umbrella RC. Note: No version listing means that the machine (roaming computer) has never successfully synchronized with Umbrella. |
| Last Synced | Lapsed time since the roaming computer last synced with Umbrella's API. Approximately once per hour, the API syncs to check for updates and verify that the internal domain list is up to date. |
| OS Version | The OS version recorded when the client is first installed. |
| Tags | DNS policies only. Indicates any groupings that the roaming computer is a part of. For more information, see Group Roaming Computers with Tags. |
| Security Information - IPv4 | Description |
|---|---|
| Status | The current state of the Umbrella roaming client. *Green states:** _ Protected—The appropriate policy settings in the Umbrella dashboard are being enforced; the computer can communicate with Umbrella's DNS servers. _ Protected & Encrypted at the DNS Layer—Same as protected, but the DNS queries are encrypted in transit. _ Protected by VA at the DNS Layer—The Umbrella roaming client has detected a VA on the network and is deferring to it (can include both DNS and IP Layers). _ Protected by Network—The Umbrella roaming client has detected that the current network has an Umbrella network protection policy in place where the local DNS server and the computer are on the same registered dashboard network registration and the Umbrella roaming client is configured to disable itself while on a protected network—this is a configurable option. *_ Yellow – Unprotected**—The policy is not currently being enforced; the computer is unable to communicate with our DNS servers. _ Grey (Offline)—The computer has been powered down, does not have an active internet connection or the Umbrella roaming client has been improperly installed, or uninstalled while disconnected from the internet. _ Grey (Uninstalled)—The Umbrella roaming client was uninstalled on the endpoint and has not been deleted from the dashboard. It can either be reinstalled on the endpoint or deleted from the dashboard. _ Grey (Disabled)—The Umbrella roaming client was manually disabled by the user. This is a feature for OS X only. For more information, see Umbrella Roaming Client for OS X: Adding an Enable/Disable Option to the Menu Bar Icon. * Red (Unregistered)—The Umbrella roaming client cannot perform initial registration with Umbrella over HTTPS. |
| DNS Layer Security | Yes or No. Displays either a locked or unlocked icon. Indicates whether the DNS requests between the computer and Umbrella are encrypted or not. Note: Umbrella roaming clients behind a Virtual Appliance (VA) is not encrypted. |
| Last Active Policy | The policy assigned to this computer when it last synced with the Umbrella API. |
| Security Information - IPv6 | Description |
|---|---|
| Status | The current state of the Umbrella roaming client. *Green states:** _ Protected—The appropriate policy settings in the Umbrella dashboard are being enforced; the computer can communicate with our DNS servers. _ Protected & Encrypted at the DNS Layer—Same as protected, but the DNS queries are encrypted in transit. _ Protected by VA at the DNS Layer—The Umbrella roaming client has detected a VA on the network and is deferring to it (can include both DNS and IP Layers). _ Protected by Network—The Umbrella roaming client has detected that the current network has an Umbrella network protection policy in place where the local DNS server and the computer are on the same registered dashboard network registration and the Umbrella roaming client is configured to disable itself while on a protected network—this is a configurable option. *_ Yellow – Unprotected**—The policy is not currently being enforced; the computer is unable to communicate with our DNS servers. _ Grey (Offline)—The computer has been powered down, does not have an active internet connection or the Umbrella roaming client has been improperly installed, or uninstalled while disconnected from the internet. _ Grey (Uninstalled)—The Umbrella roaming client was uninstalled on the endpoint and has not been deleted from the dashboard. It can either be reinstalled on the endpoint or deleted from the dashboard. _ Grey (Disabled)—The Umbrella roaming client was manually disabled by the user. This is a feature for OSX only. For more information, see Umbrella Roaming Client for OS X: Adding an Enable/Disable Option to the Menu Bar Icon. * Red (Unregistered)—The Umbrella roaming client cannot perform initial registration with our system over HTTPS. |
| DNS64 | Detected or Not Detected. Displays a caution sign when detected because IPv6 queries for domains with IPv4-only addresses are not resolved by Umbrella at this time. These queries may be answered by your local DNS resolver and thus not protected by Umbrella. |
| Last Active Policy | The policy assigned to this computer when it last synced with the Umbrella API. |
Tray Icon Status
As displayed through the tray icon on the device where the Umbrella roaming client is deployed, status is indicated through a colored dot that is added to the tray icon. Status is determined based on a series of DNS queries, which are used as tests to determine the correct state.
Note: The Tray icon can be set to "hidden" during installation.
Status Indicators
The roaming client icon without a dot indicates a healthy roaming client.
![]()
A colored dot on the roaming client icon indicates a possible issue with the roaming client.
![]()
For more information about which ports and protocols the Umbrella roaming client utilizes, see the Network Access section of Prerequisites.
| State | Icon (Dot Color) | Description |
|---|---|---|
| Waiting | Grey | No active network connections. The Umbrella roaming client waits for an active network connection. On a trusted network. For more information, see macOS Mobile Device Management. |
| Reserved | Grey | No active network connections. The Umbrella roaming client waits for an active network connection. On a trusted network. |
| Open | Yellow | There is at least one active network connection; however, the Umbrella roaming client can’t connect to 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35 over port 53/UDP on any active connection. The user is not protected by Umbrella or reporting to Umbrella. The system's DNS settings are now back to their original settings (DHCP or Static). |
| Protected | Yellow | DNS64 detected. The roaming client does not provide protection for DNS64 queries, though normal IPv4 and IPv6 queries are protected. |
| Transparent | No dot | A network connection is active, and the Umbrella roaming client is able to connect to port 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35 over port 53/UDP, but not 443/UDP. The user is protected and reporting to Umbrella, but the connection is not encrypted. |
| Encrypted | No dot | The Umbrella roaming client has established a connection to 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35 over port 443/UDP. The user is protected and reporting to Umbrella and the DNS queries are encrypted. Internal domains are forwarded to DHCP-delegated or statically-set DNS servers, and are therefore not encrypted. |
| Protected Network | No dot | The computer is behind a protected network, and the organization has “Disable Behind Protected Networks” enabled in their dashboard. The Umbrella roaming client has reverted the DNS settings back to what was set through DHCP or statically set. The connection is not encrypted. |
| Behind Virtual Appliance | No dot | The computer is connected to a network which has VAs configured for DNS servers. The Umbrella roaming client disables itself and reverts the DNS settings back to what was set through DHCP or statically set. The connection is not encrypted. |
| Unprotected | Red | Protection failure. The roaming client is not providing protection. |
| Trusted | No dot | The computer is on a customer defined trusted network, this state is leveraged in special situations to addresses specific needs. Please contact your support team to learn more. |
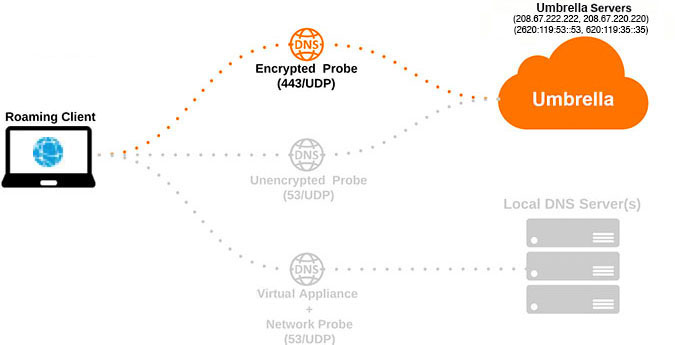
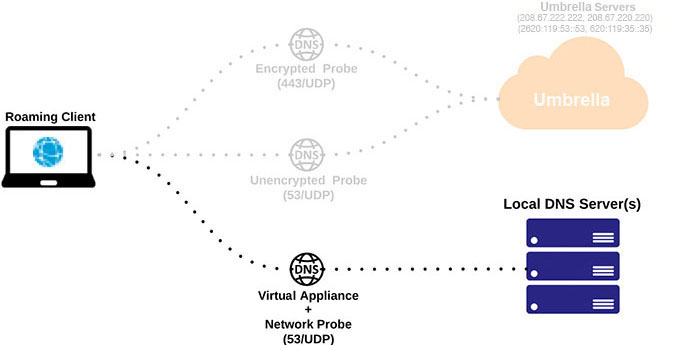
Probes
Probes are frequent DNS requests performed by the Umbrella roaming client that acts as a health check and analysis of the networking environment. How the Cisco Umbrella roaming client operates depends on these probes, which determine the state of the Umbrella roaming client.
The probe types are:
- Encrypted
- Unencrypted
- Virtual Appliance + Protected Network
The probes are DNS queries sent to 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35, and they specifically send TXT-type query for the domain debug.opendns.com. It's common to see many of these in your network or DNS logs. Probes run approximately every 10 seconds in order to sense changes in the network environment. In a typical networking environment, where two local DNS servers are present, the Umbrella roaming client sends:
- 1x Encrypted Probe
- 1x Unencrypted Probe
- 2x Virtual Appliance + Protected Network probes (one per local DNS server).
Encrypted Probe
Sends a DNS request to 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35 over 443/UDP.
- Success—Response. We operate in the Encrypted state, unless the Virtual Appliance + Protected Network Probe also succeeds, in which case we switch to one of those states.
- Failure—No response. We attempt to operate in the Unencrypted state and send the Unencrypted Probe to verify.
Unencrypted Probe
Send a DNS request to 208.67.222.222 / 208.67.220.220 / 2620:119:53::53 / 2620:119:35::35 over 53/UDP.
- Success—Response. We operate in the Unencrypted state unless the Virtual Appliance + Protected Network Probe also succeeds, in which case we switch to one of those states.
- Failure—No response. We transition to the Open state.
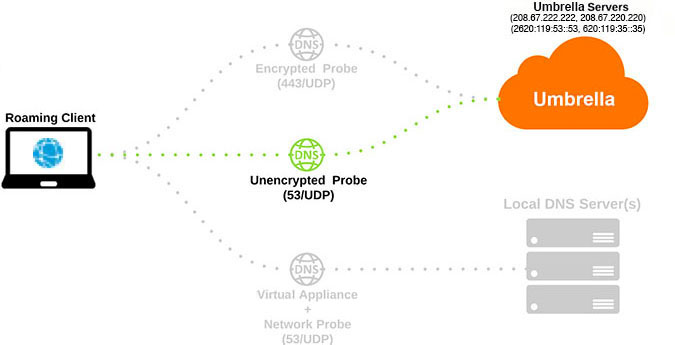
Virtual Appliance + Protected Network Probe
Send a DNS request to the local DNS servers over 53/UDP.
- Success—Three local DNS servers are either a Virtual Appliance or Protected Network, and either the Encrypted or Unencrypted probe also succeeded. Operate in either Behind_VA or Protected Network states, respectively.
- Failure—The local DNS servers are neither a VA or a protected network. Do not operate in either Behind_VA or Protected Network states.
If using protection measures (Endpoint Client Firewall / Antivirus) that require you to allow list network access on a per-executable (binary) basis, these are the processes to allow access:
Windows
- ERCService.exe
- ERCInterface.exe (if the GUI was installed)
- dnscryptproxy.exe (This is new as of version 3.0 of the Umbrella Roaming Client for Windows, and replaces dnscrypt-proxy)
macOS
- dns-updater
These executables perform the same network-based tasks:
- DNS lookups to internal domains
- Perform health checks as explained in our status and functionality article
- Communicate with our API (Updates, Sync status to dashboard)
- Communicate with our logging and diagnostics infrastructure.
| Port | Protocol | Destination |
|---|---|---|
| 53 | UDP | Any |
| 80 | TCP | 67.215.92.201, 67.215.92.210, 146.112.255.152/29 (8 IPs), ocsp.digicert.com, crl3.digicert.com, and crl4.digicert.com IPv6: 2620:0:cc1:115::210 IPv6: 2a04:e4c7:ffff::20/125 (8 IPs) |
| 443 | TCP | 146.112.255.101, 67.215.71.201, 67.215.92.210, 146.112.255.152/29 (8 IPs) IPv6: 2620:0:cc1:115::210 IPv6: 2a04:e4c7:ffff::20/125 (8 IPs) |
Note: The Digicert domains resolve to various IP addresses based on CDN and are subject to change.
The other IP addresses in the table above resolve to disthost.umbrella.com, api.opendns.com, and disthost.opendns.com.
dnscrypt-proxy
Perform encrypted and unencrypted DNS queries directly to Umbrella.
| Port | Protocol | Destination |
|---|---|---|
| 53 | UDP | 208.67.222.222 208.67.220.220 2620:119:53::53 2620:119:35::35 |
| 53 | TCP | 208.67.222.222 208.67.220.220 2620:119:53::53 2620:119:35::35 |
| 443 | UDP | 208.67.222.222 208.67.220.220 2620:119:53::53 2620:119:35::35 |
When the computer is powered on, woken from hibernation, or if there is a new network connection established, the roaming client performs a series of tests to determine which state it should be in. Each test has a success result and a failure result. It performs the following actions, in order of execution.
Initial Resting Stage
If the roaming client does not detect any active network connections, it operates in the Waiting or Reserved state and waits for an active network connection before starting Stage 1.
Stage 1
The roaming client sends a normal EDNS request through each DHCP-delegated or static DNS server on every interface. If it detects that one of the DNS requests went through a VA, it's considered success and will operate in the Behind VA state. It does not detect any VAs, it's considered a failure and moves to Stage 2.
Stage 2
The roaming client sends a special encrypted EDNS request over 443/UDP to 208.67.222.222/208.67.220.220/2620:119:53::53/2620:119:35::35. If the requests receive a valid response, it's considered a success and the Umbrella roaming client will operate in the Encrypted state. If the requests time out or are rejected, it's considered a failure and moves on to Stage 3.
Stage 3
The roaming client sends a normal EDNS request over port 53/UDP to 208.67.222.222/208.67.220.220/2620:119:53::53/2620:119:35::35. If the requests receive a valid response, it's considered a success and the roaming client will operate in the Transparent state and send an additional test to determine if it should operate in the Protected Network state. If the requests time out or are rejected, it's considered a failure and moves on to Stage 4.
Stage 4
The roaming client has failed all tests, and reverts all the DNS settings to the original DHCP or static values and operates in the Open state. The transition to the Open state can take up to six seconds, so if a network has third-party DNS blocked, DNS resolution will not occur until the Umbrella roaming client can transition all the way to this state.
Unprotected Status (Yellow)
When the status (not state) of the roaming client is Unprotected, the roaming client tests all stages aggressively, so it may transition to a Protected state as soon as possible. This is designed to avoid the need to restart the Umbrella roaming client in situations wherein an administrator suddenly opens a firewall port or a user joins a public WiFi network and must authenticate or accept the WiFi network's Terms of Service. Within seconds of successful WiFi authentication or a change in the firewall, the roaming client will return to the Protected status and choose the appropriate state.
Identity Support for the Roaming Client < Status and Functionality > Virtual Appliances
Updated 5 months ago
