Local DNS Forwarding
Umbrella Virtual Appliances (VAs) are conditional DNS forwarders in your network, forwarding public DNS queries to Umbrella, and local DNS queries to your existing local DNS servers/forwarders, respectively.
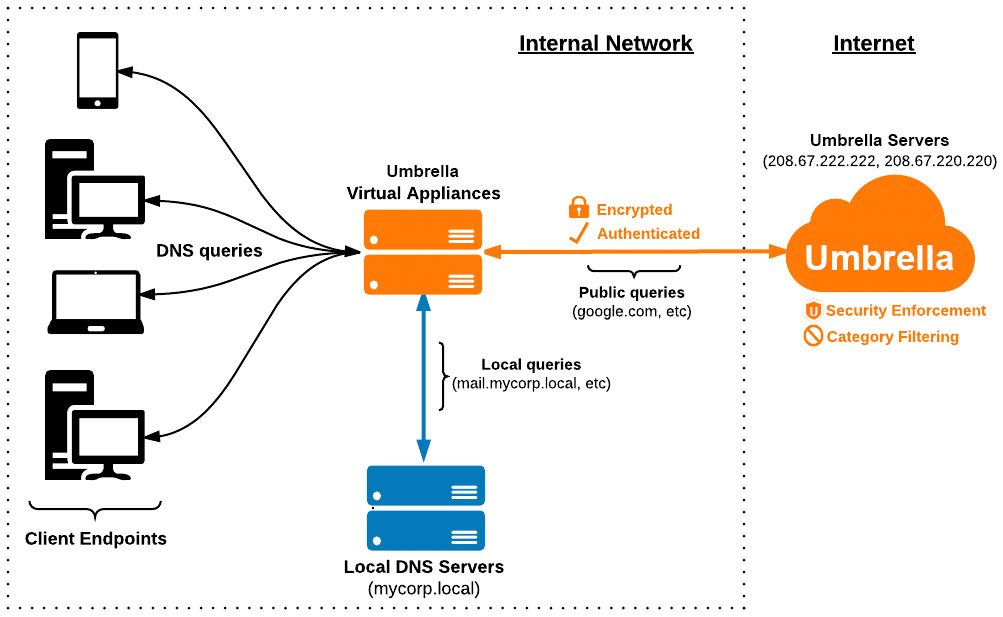
When the VAs receive queries which match domains or subdomains of a local DNS zone (local domain), the VA forwards those queries to your local DNS server for resolution instead of Umbrella's public DNS resolvers. This is accomplished by defining your local domain names in the Umbrella dashboard.
Important
Do not set your local DNS forwarders to point to the VAs. It's possible to create loops in DNS in this configuration and it's not recommended or supported. The diagram above is meant to represent the typical flow of DNS traffic from a client and not how a local DNS forwarder should be pointed.
Table of Contents
Manage Domains in the VA
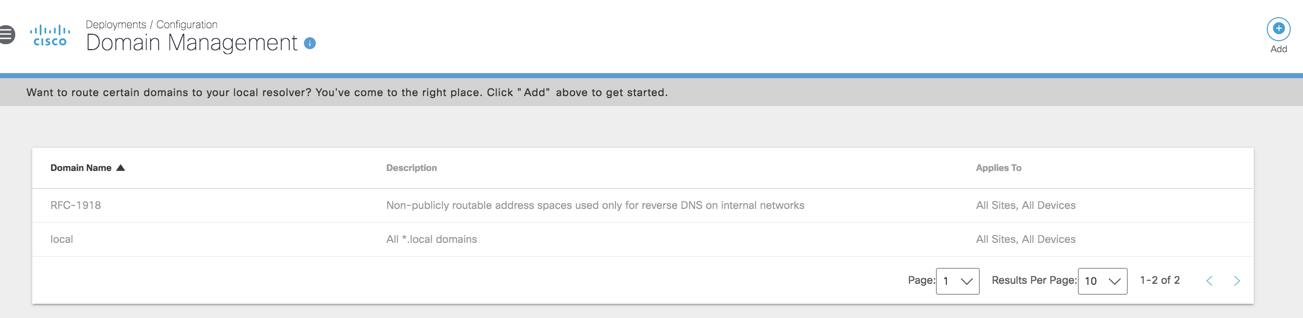
- Navigate to Deployments > Configuration > Domain Management.
Any DNS queries received by the VAs which match a domain on the Internal Domains list, or a subdomain thereof, will be forwarded to the local DNS server as described in Configure Virtual Appliances.
The following domains/zones are pre-populated and do not need to be added:
- RFC1918—non-publicly routable address spaces used only for reverse DNS on internal networks. All local IP address space for reverse lookups (PTR records) is covered with this entry. Adding in-addr.arpa reverse lookup zones are not needed.
- .local—Any domain name with a TLD of .local.
2. Click Add.
You have a choice of what type of identities are set to respect these internal domains:
- All Sites—Covers all requests that are made through a VA.
- Sites listed under All Sites—Covers requests only made through VAs deployed in the selected sites.
- All Devices—Covers all requests that are made through a roaming device.
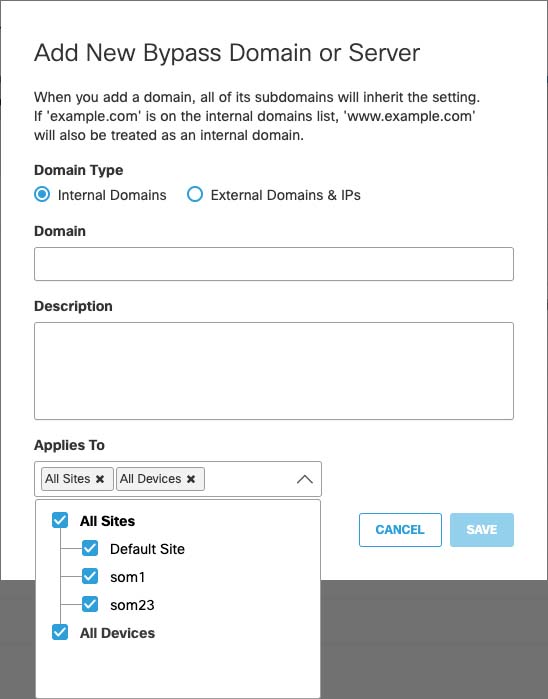
If you do not plan on using Umbrella roaming clients, you may leave this option at the default setting—All Sites and All Devices.
What format does the internal domains list accept?
See Manage Destination Lists. Note that only domains may be entered into the Internal Domains list.
Which domains should be added?
Any domain name which has a forward lookup zone on your local DNS servers must be added, along with any domains that are configured with conditional forwarders. If you already know which domains to add, skip the Add A & PTR Records for the VAs section.
On Windows Server, this information is located in the DNS Manager tool.
- Open the DNS Manager (Start > Run > and type "dnsmgmt.msc").
- Expand the Server name and Forward Lookup Zones sections. Any domains listed here are treated as local by your local DNS forwarders and must be added to the Internal Domains section of the Umbrella dashboard. This is a critical part of the setup process.
- If any public IPs are in use as local IPs, also add the Reverse Lookup Zone of any public IPs which have local DNS records attached. RFC-1918 reverse lookup zones are included by default. These are entered in the in-addr.arpa format.
Note: Be aware that it can take up to 10 minutes for the virtual appliance to synchronize with changes you make to the the Internal Domains list.
(Optional) Add A & PTR Records for the VAs
Adding A and PTR records for the VAs makes them easy to identify within your network topology, including firewall and security appliance logs.
If you’re unfamiliar with adding A and PTR records, see the Microsoft articles:
After adding A and/or PTR records, verify the records:
Verify PTR record
Enter: "nslookup (VA IP ADDRESS)" in a command prompt. You should see the record in the last line of the result.
nslookup 192.168.1.10
Server:192.168.1.1
Address:192.168.1.1#53
Non-authoritative answer:
9.168.192.in-addr.arpaname = [va01.corp.domain.com]
Verify A record
Enter: "nslookup (VA HOSTNAME)" in a command prompt. You should see the record in the last line of the result.
nslookup va01.corp.domain.com
Server: 192.168.1.1
Address: 192.168.1.1#53
Non-authoritative answer:
Name: va01.corp.domain.com
Address: 192.168.1.9
Configure Local DNS Servers on the VA
You can configure the VA to send queries for local domains to any local DNS server. Alternately, you can also selectively forward DNS queries for specific local domains to specific local DNS servers.
Use the following commands to configure the VA to send queries for local domains to local DNS servers:
| Task | Command | Note |
|---|---|---|
| Configure up to 6 local DNS servers | config localdns add <ip> | The command must be entered individually for each local DNS server. The command does not take multiple IP inputs. |
| Remove a configured local DNS server | config localdns remove <ip> | |
| Add a local DNS server and assign specific internal domains to this server | config localdns add <ip of local DNS server><domain1><domain2...domainN> | Internal domains provided here needed to be added first to the Domain Management page of the Umbrella dashboard. Requests for other internal domains will not be forwarded to these local DNS servers. |
| Show the list of internal DNS servers and any domain mappings against these servers | config localdns show |
Note: If you are assigning specific domains to specific local DNS servers, be sure to add at least one local DNS server with no domain assignment so that it can support queries for all other internal domains.
Examples
You can also combine the above features to have some local domains redirected to specific local DNS servers and other domains redirected to the remaining local DNS servers.
| Command | Outcome |
|---|---|
config localdns add 209.165.200.229 internaldomain1.com | DNS queries for internaldomain1.com will now be forwarded to 209.165.200.229. |
config localdns add 209.165.200.229 internaldomain1.com internaldomain2.com | DNS queries for both internal domains will be forwarded to the DNS server with IP 209.165.200.229. |
config localdns add 209.165.200.229 | DNS queries for all other internal domains will be forwarded to 209.165.200.229. |
Configure Virtual Appliances < Local DNS Forwarding > Reroute DNS
Updated over 1 year ago
