Add a Custom User Role
Create a custom user role that is configured with unique Umbrella dashboard access permissions, so that when you add a user to the Umbrella dashboard you can give that user very specific Umbrella dashboard access.
Prerequisites
- Full admin access to the Umbrella dashboard. See Manage User Roles.
Procedure
- Navigate to Admin > User Roles and click Add.
- Give the role a descriptive name, optionally add a description for this role, and then select the access Permissions you want to grant the new role.
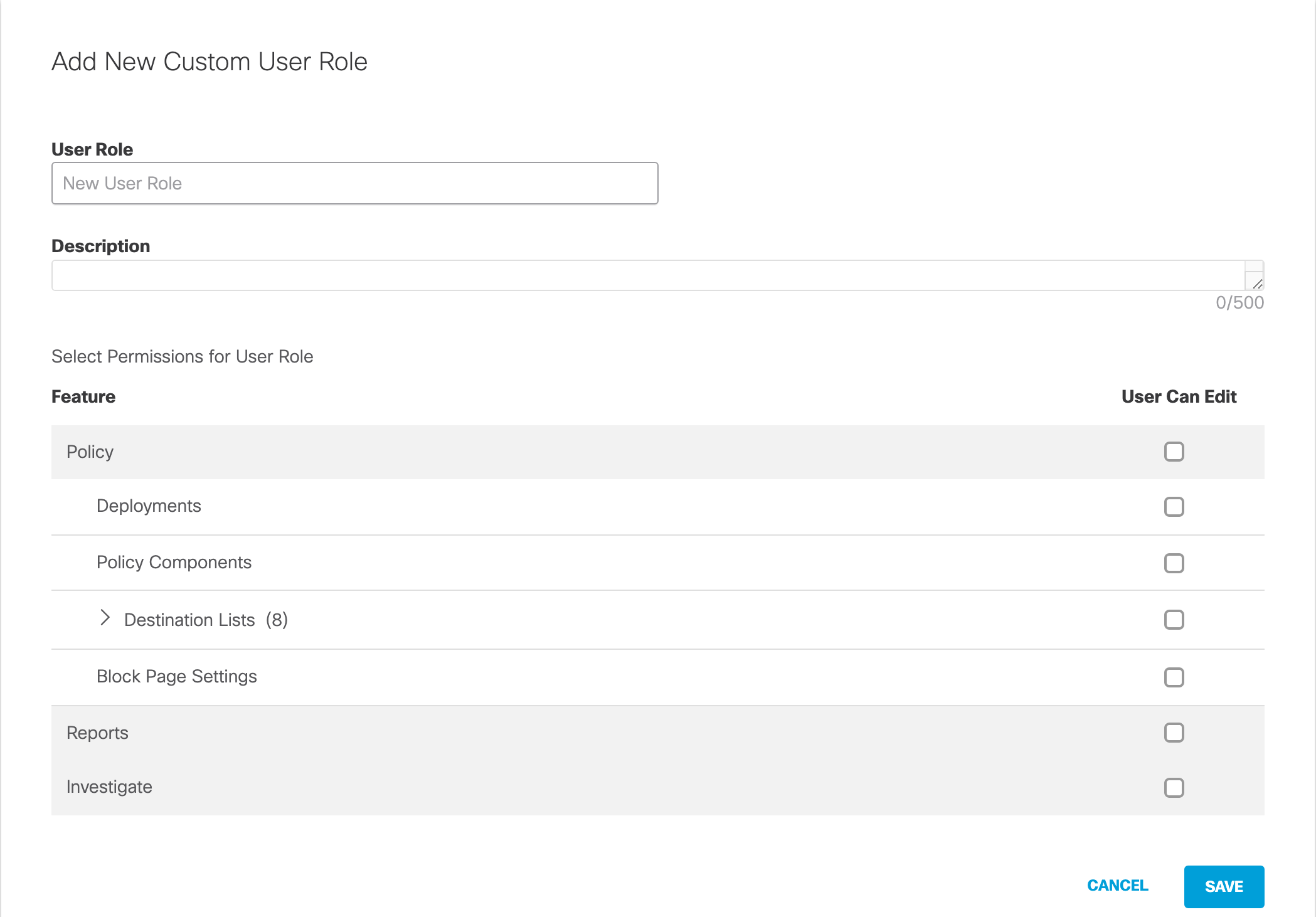
Permissions for custom user role:
- Policy—Allows for the management of deployed identities, policy settings including destination lists, and block page settings. The Policy permission is not allowed to:
- Manage other users within the dashboard
- Add or modify roles, or any of the other Admin features
- Deployments—Allows for the management—create, modify, rename, and delete—of deployed Umbrella identities and configurations except for Network Devices. The role cannot download Mobile Devices configuration, download Chromebook configuration, add or remove tags from Roaming Computer, nor assign a policy to a newly created identity. This role is ideal for provisioning new devices under Umbrella as part of initially bringing computers online to your network.
- Destination Lists—Allows for the management of destination lists, which gives the role the ability to add or delete destinations in destination lists.
Including either the Global Allow List or the Global Block List enables this role to allow or block a destination for the entire organization. - Block Page Settings —Allows for the management of all Block Page Settings (but not the full policy), which gives the role the ability to change a block page's appearance, add, modify or delete a block page user or add, modify or delete a block page bypass code. However, if selected on its own, it cannot add a user account to be assigned to the block page user. For more information, see How to configure the Block Page Bypass (BPB) user role.
- Reports—Allows for the management of Reports, which gives the role the ability to create reports, run reports, and export reports. In addition, the Reports role includes the Investigate role. If you select only the Reports role, you can only access the Reports and Investigate sections of the dashboard.
- Investigate—Allows for the management of Investigate, which includes the Investigate Smart Search and Pattern Search. If your subscription includes the Umbrella Investigate API, you can list the Investigate API access tokens. The Investigate permission can not create or delete an Investigate API access token.
Note: If you enable a role that can provision identities but not manage policies, ensure that your policies are ordered correctly according to the policy execution arrow (which points downward in the policy section). For example, if a user with the Deployments role only provisions a new roaming computer, Umbrella applies the Default policy to the roaming computer unless you select All Roaming Clients in a policy that has higher priority.
- Click Save.
Once created, you can assign this role to a user. For more information about creating user accounts, see Add a New Account.
Once you've configured the user with a role, their dashboard is automatically limited to only the elements they've been assigned. This can mean their dashboard is different than what you may be used to, as elements may be missing—areas of the dashboard that a user role is not granted access to are not greyed out; instead, they are not displayed.
Add a New User < Add a Custom User Role > Manage Your Logs
Updated almost 2 years ago
