Troubleshooting
Check the scenarios below if you have difficulty validating the Cisco Secure Client with Umbrella module after first installing it.
Table of Contents
- Is this a VPN to Umbrella?
- An Internal Site Isn’t Loading
- Configuration Issues
- Check for VPN Connection and Policy
- Check Block Page
- Get the Android ID
- Fail Close/Open Scenario
- Check Device Registration
- Missing CA Certificate
- Org ID on Policy Page is 0
- App Installation is Blocked
- Offboarding Users
- Known Issues
Is this a VPN to Umbrella?
The Cisco Secure Client for Umbrella module uses a VPN-like mechanism but it is not in a traditional VPN. This VPN-like mechanism is used to intercept DNS queries so that the module can process them (add metadata, encrypt and forward to Umbrella). The Android operating system’s user interface does not show this distinction, so it appears as if a VPN were running.
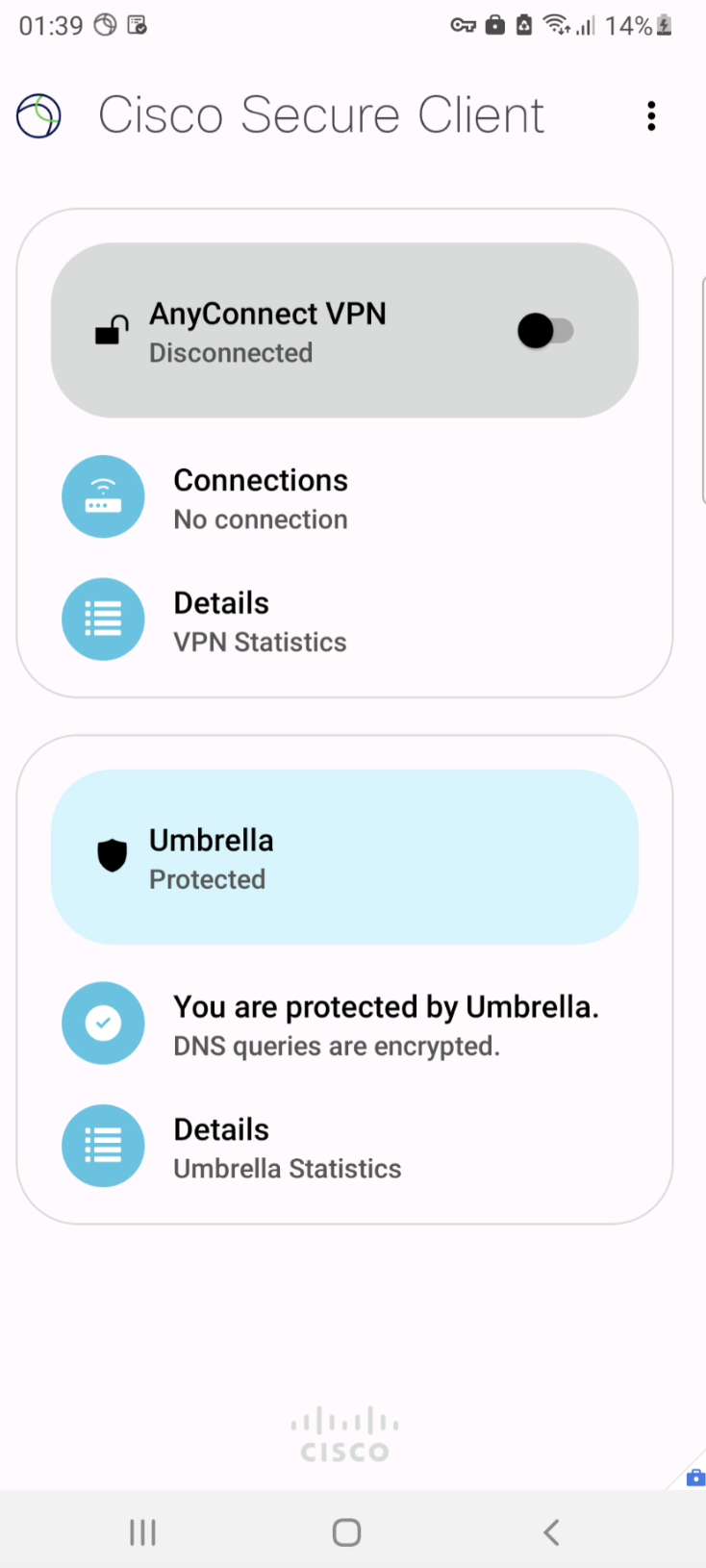
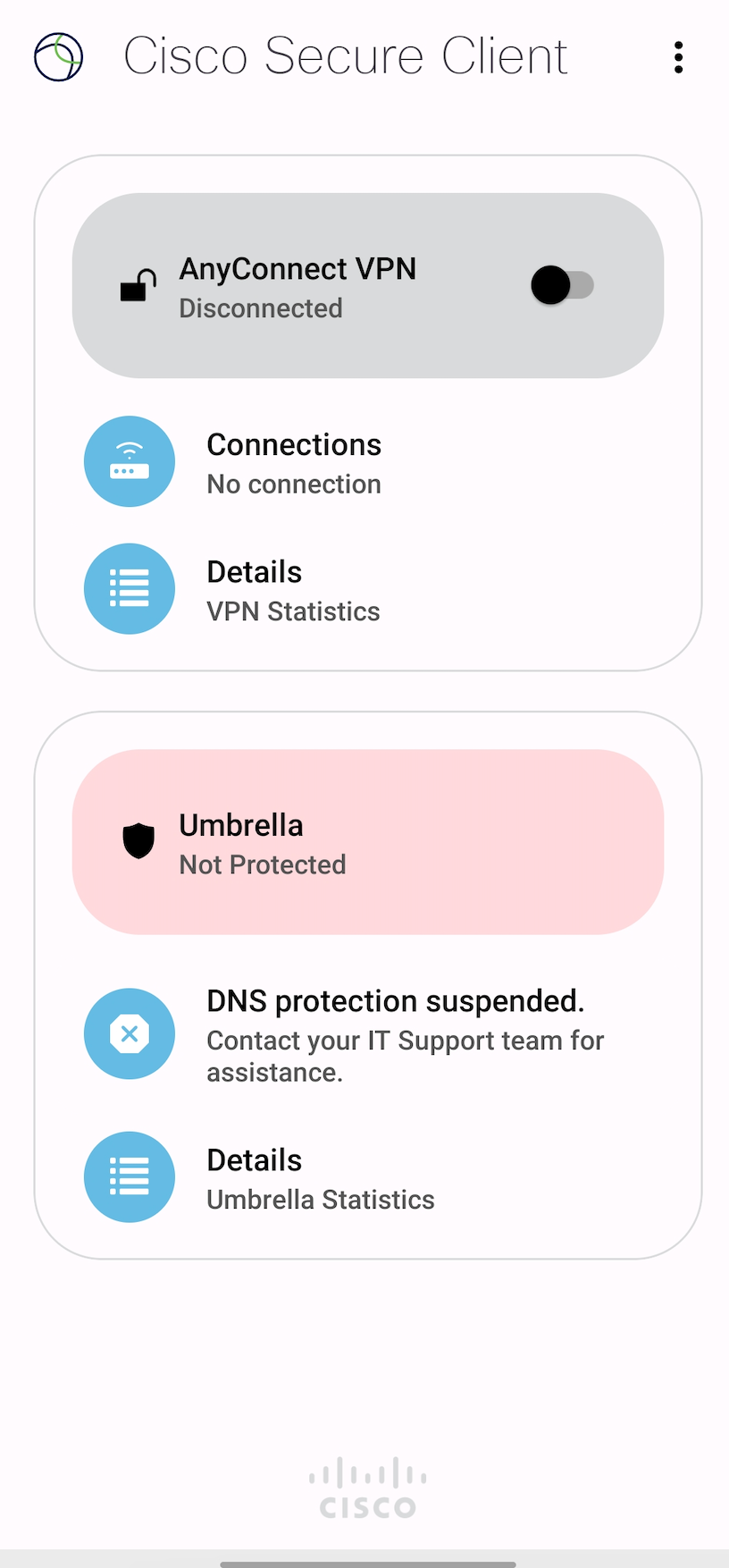
When Umbrella protection starts, a green checkmark appears under the Umbrella UI subheading with the text “You are protected by Umbrella.”
Virtual Appliance in the Network
If an Umbrella Virtual Appliance (VA) supporting HTTPS is configured in the network, the Umbrella module detects this and backs off. If a VA is not present, or is present but does not support HTTPS, then the Umbrella module remains active.
An Internal Site Isn’t Loading
The Umbrella module makes a best effort to automatically detect internal (intranet) sites and route DNS appropriately to the local DNS server. However, these mechanisms may not work in all scenarios. Therefore it’s important to enter your internal / intranet domains in the Domain Management tools in the Umbrella dashboard. For more details, refer to Domain Management.
Configuration Issues
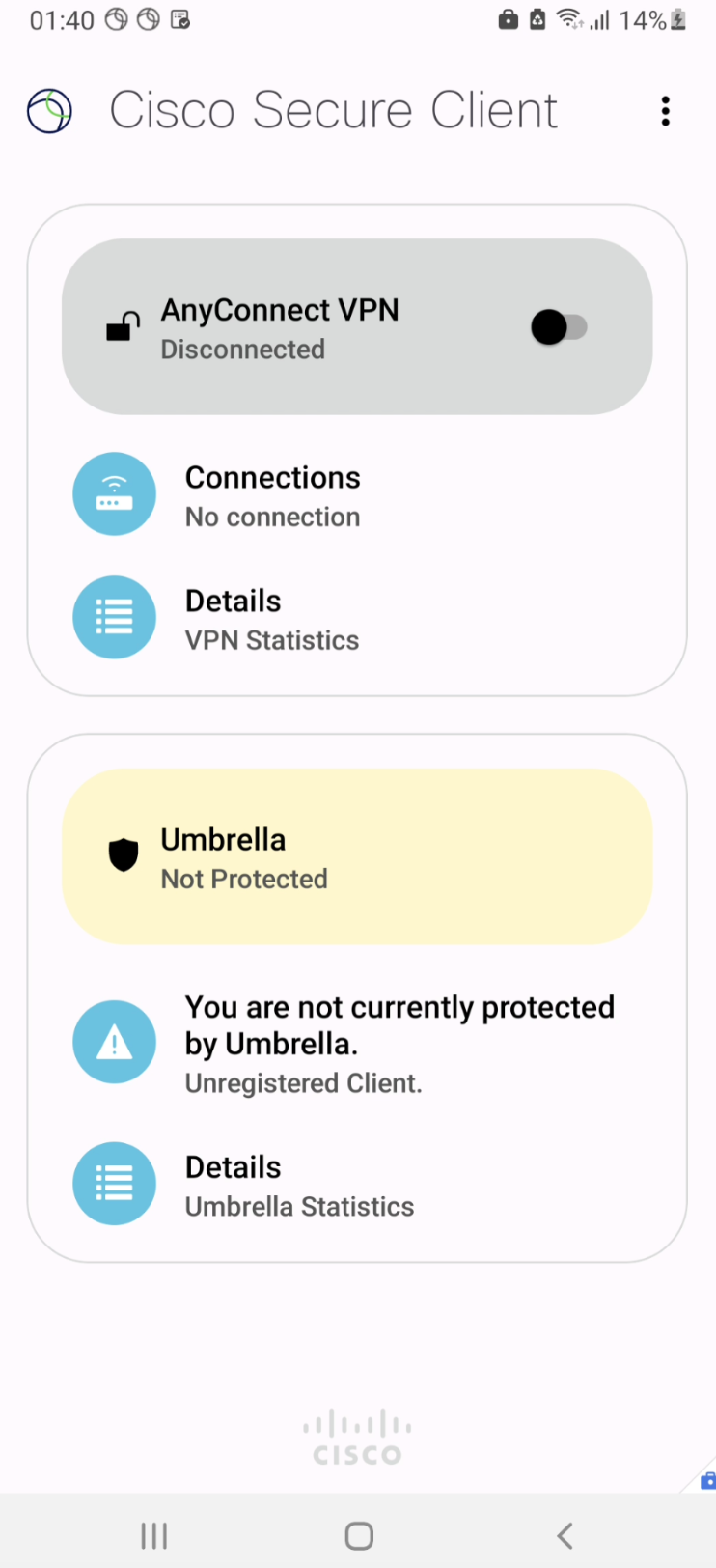
If the Umbrella Section in AnyConnect app does not display a green checkmark, check the configuration details pushed from the MDM. If you don’t have access, contact your administrator.
You can check if the configuration is available by clicking on the menu button at the top right in AnyConnect > Diagnostics > Logging and System Information > System > Managed Configuration.
Verify that the managed configuration pushed by the administrator is available.
Check for VPN Connection and Policy
- Verify that the “key” icon (or something similar) is displayed in the notification panel for the VPN session created by AnyConnect.
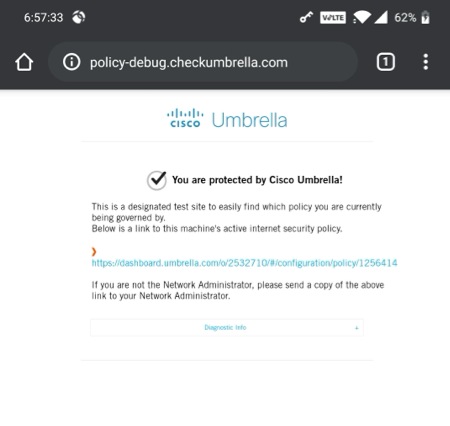
- Open a browser.
- Clear the cache.
- Load
http://policy-debug.checkumbrella.com. The page should load and display a URL to the active policy in the Umbrella dashboard. The format of the URL should be:https://dashboard.umbrella.com/o/<orgid>/#/configuration/policy/<policyid>. - Verify that the organization ID displayed in the URL is the same as your Umbrella organization ID.
Check Block Page
Open http://www.internetbadguys.com/. You should see an Umbrella block page displaying the domain that was blocked along with the IP address of your device and the reasons for blocking. If you do not see the Umbrella block page, follow these steps:
- Select Settings > Apps > AnyConnect > Force Close.
- Restart AnyConnect.
- Reopen
http://www.internetbadguys.com/and check for the Umbrella block page.
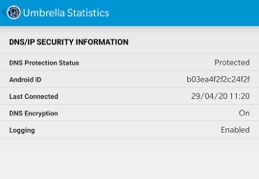
Get the Android ID
- Launch AnyConnect.
- Open Umbrella Security.
- Click Options, then open Umbrella Statistics. The Android ID is listed in that window.
Fail Close/Open Scenario
Under the Mobile Device Settings, select either of the options available for iOS and Android devices:
- Fail-Open
- Fail-Close
To adjust the notifications on the device, select one of the user notifications on the device.
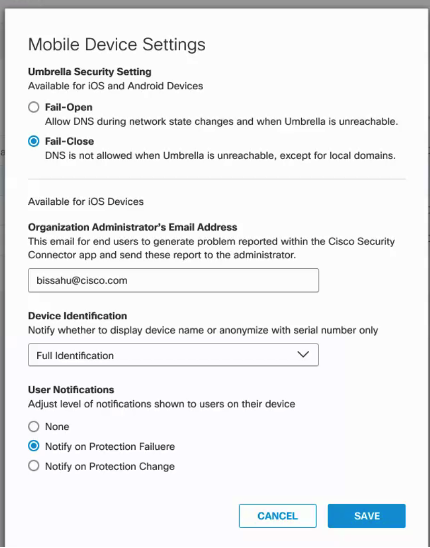
In case of internal errors, such as the Umbrella Resolver is not reachable or the DNSCrypt Certificate is not available, the Umbrella UI displays the following:
Check Device Registration
- Find the
android_idfor your Android device. - Login to
https://dashboard.umbrella.com/, - Choose the
org idassociated with the device. - Navigate to Deployments > Core Identities > Mobile Devices.
- Verify that the
android_idis listed.
Missing CA Certificate
If the Umbrella block page is not displayed but you see, instead, a warning about an insecure page, then there might be an error due to a missing Umbrella root certificate.
- Download the Cisco Umbrella root certificate. For more information about downloading the root certificate, see Install the Cisco Umbrella Root Certificate.
- Secure the device with your PIN, password or pattern lock.
- Install the certificate you downloaded.
- Select the certificate file.
- Reload the block page in your browser.
Org ID on Policy Page is 0
If the http://policy-debug.opendns.com URL shows 0 for the org id and bundle (policy) id, then refresh the page. Alternatively, clear the browser cache, try an incognito window, or try a different browser.
App Installation is Blocked
In order to download apps from the Google Play Store, a Gmail ID should be configured in the MDM. If the ID is configured and the app still cannot be downloaded, the MDM admin may have chosen to disallow installation of apps from the Play Store.
Offboarding Users
In order to fully remove an end user there are two steps:
- Delete the user from the Mobile Devices page in the Umbrella Dashboard.
- Delete the Cisco Umbrella Module for AnyConnect for Android OS from the user's device. This can be done by the MDM. The MDM app itself need not be removed from the user's device.
Known Issues
- App download fails in Google Play Store after enabling Cisco Secure Client with Umbrella module. This is a known limitation from Google on Android OS versions below v10. To avoid this, you must download Apps before enabling the Umbrella App. Google has fixed this behavior in their Android OS 10. Check the issue tracker.
- In Android 10 and later, Google restricts reading serial numbers from the device. As a result, the Serial number field in the Umbrella dashboard displays “unknown” for Android 10 and later devices.
- Avoid using the Wifi Assistant; it may conflict with AnyConnect and DNS interception.
- Private DNS must be turned off for DNS interception to function properly.
- Click for information about unusual DNS queries showing in Umbrella reports.
- Huawei phones, when running in Work Profile mode, do not automatically start AnyConnect, even when the app was previously open. This does not apply to Huawei phones in Fully Managed mode.
Export Device Data to CSV< Troubleshooting > Frequently Asked Questions
Updated 9 months ago
