Manage Identities
To enable identities in Umbrella, configure your Mobile Device Manager to share the identity information.
An identity is any of the following information based on what you choose to share with Umbrella:
- User email address
- Username
- Device serial number
- Any other unique device identifier
After you push the identities to Umbrella, they are listed in the Umbrella dashboard.
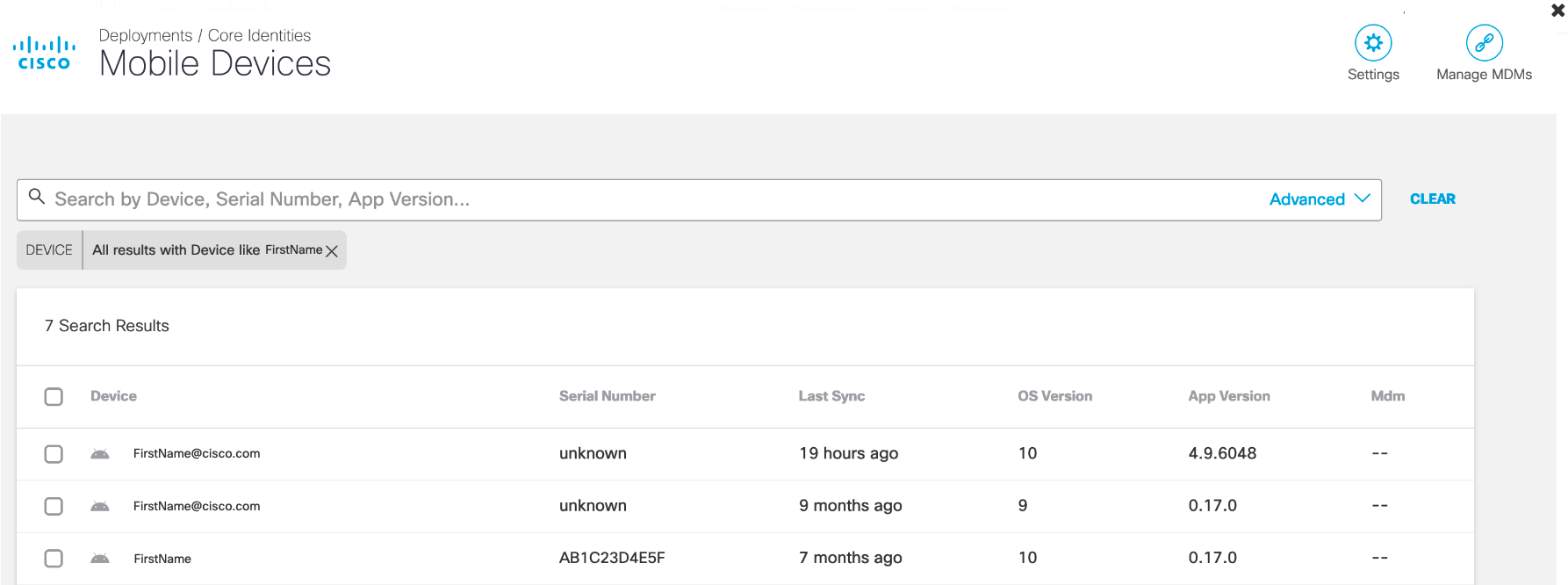
You can select the devices or user ID to search for the mobile devices. To enable user identities for Android clients, follow these steps.
Table of Contents
- Cisco Meraki Systems Manager
- Microsoft Intune
- Samsung Knox
- VMWare WorkspaceOne
- Access User Identities on the Umbrella Dashboard
Cisco Meraki Systems Manager
The key for User Identity in Meraki is umbrella_user_identity.
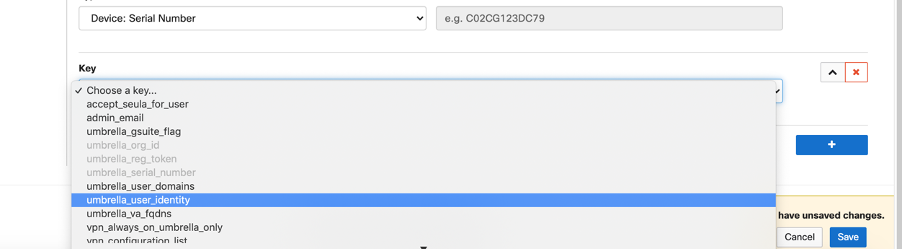
By default, the Type is a text field. Instead of choosing text, you can opt for the variables provided by Meraki SM.
For setting up a user identity value, choose a type.
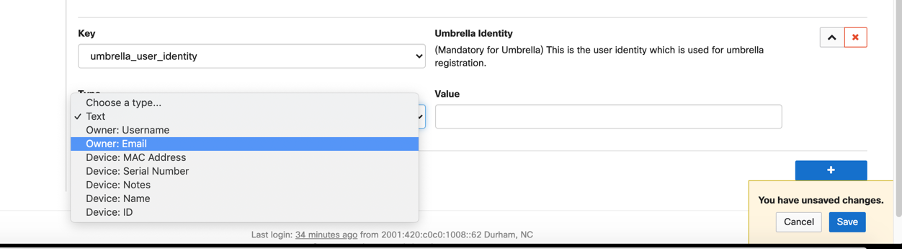
If a user identity is selected, the field looks as shown below:
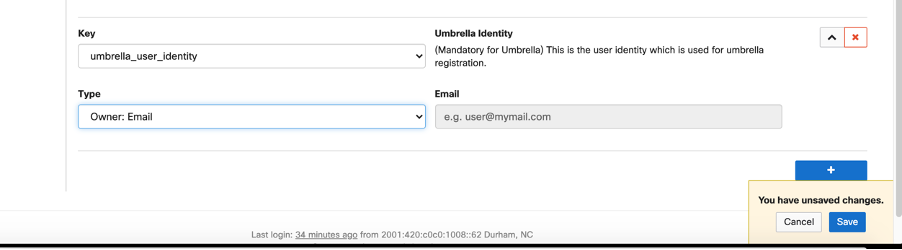
Once the configuration is pushed to the device, Meraki SM replaces the variable with the corresponding value.
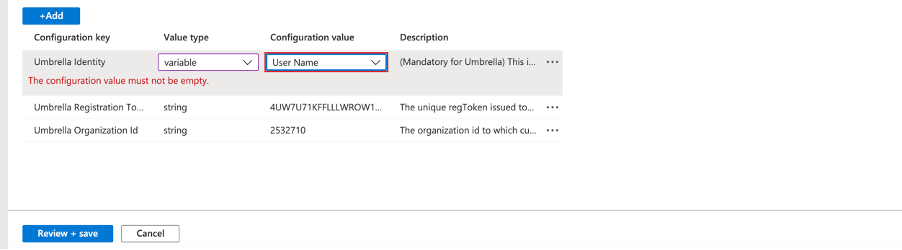
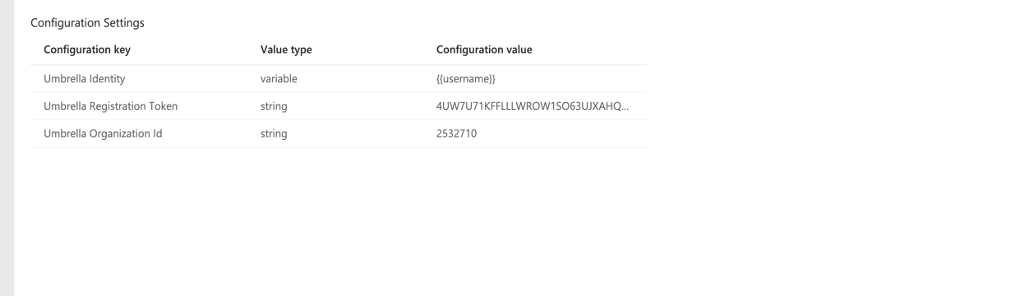
Microsoft Intune
You can choose the key for user identity.
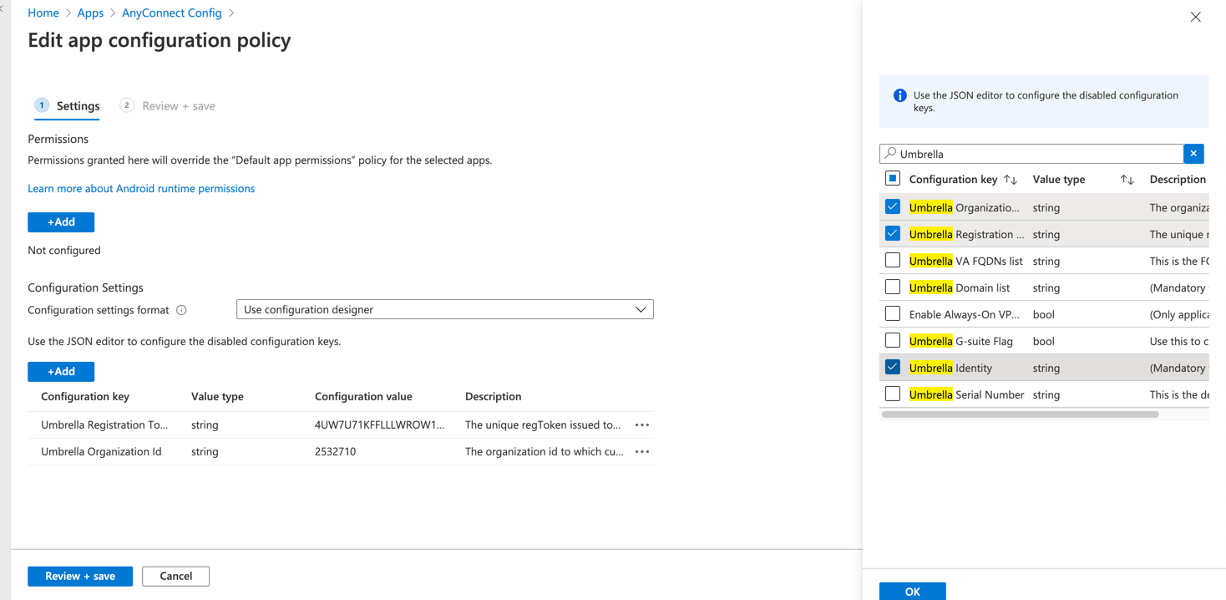
For Value type, choose either string or variable.
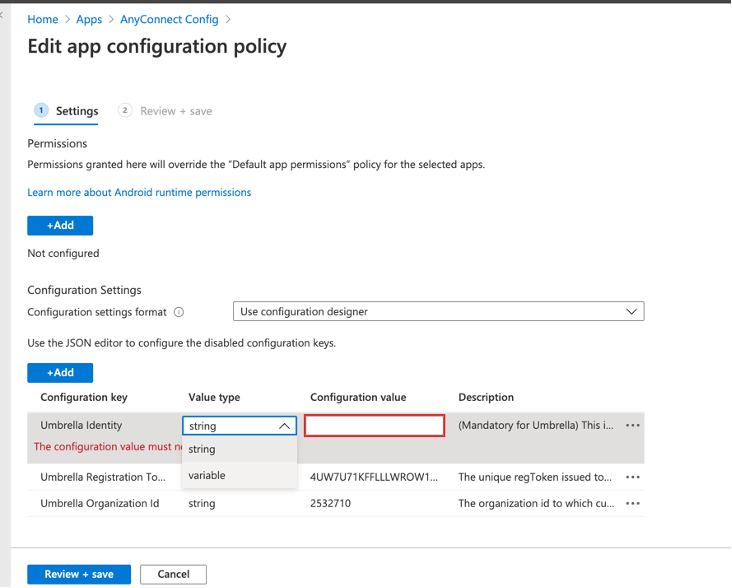
Choose the Value type as a variable so that configuration values can be selected from the options provided.
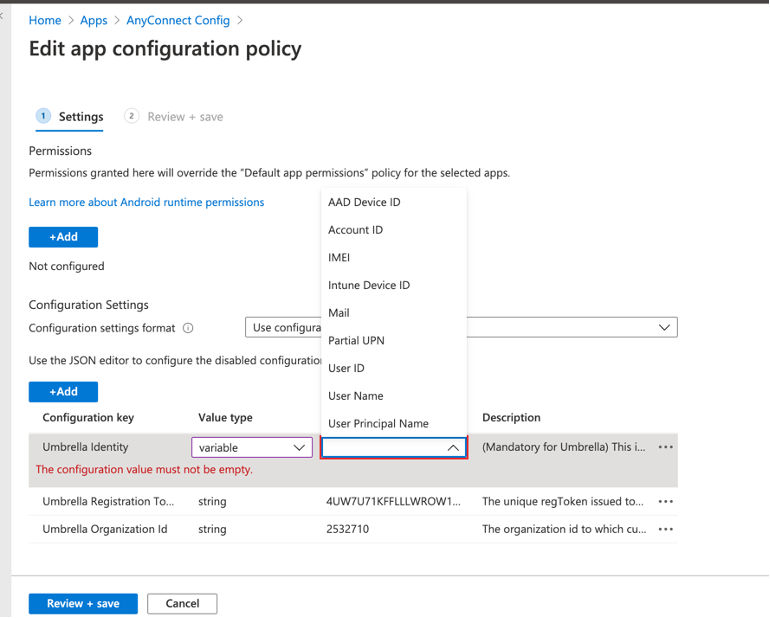
Choose any of the options from the list. Once the configuration is pushed to the device, MS Intune replaces the variable with the corresponding value.
Samsung Knox
The key for user identity in Knox MDM is Umbrella Identity.
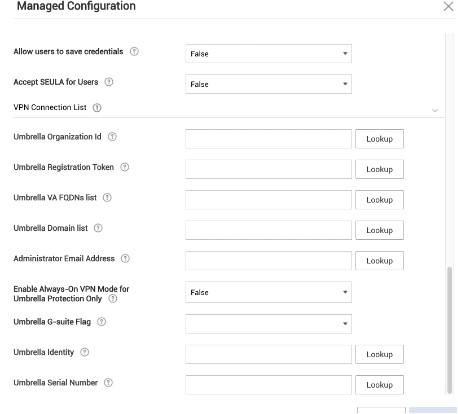
Click LookUp for the Select Lookup Item and choose the appropriate variable for the identity.
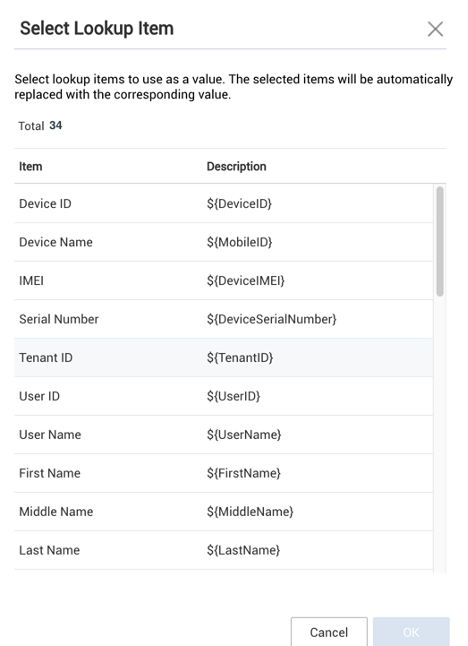
After you select the appropriate variable for the identity, the page appears.
VMWare WorkspaceOne
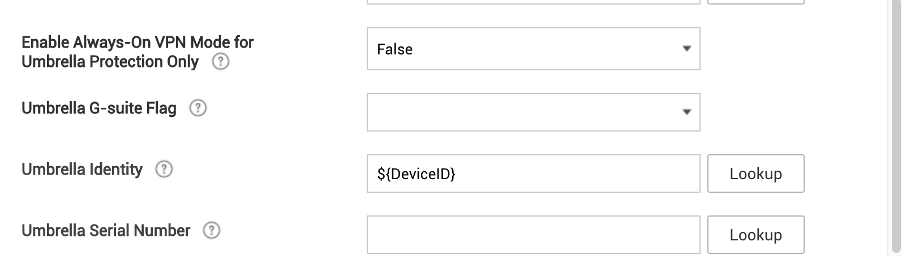
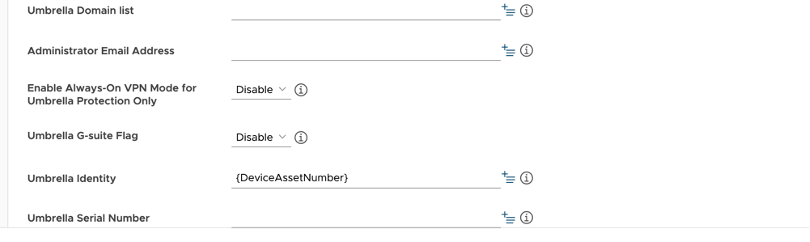
The key for user identity in VMWare WorkspaceOne is Umbrella Identity.
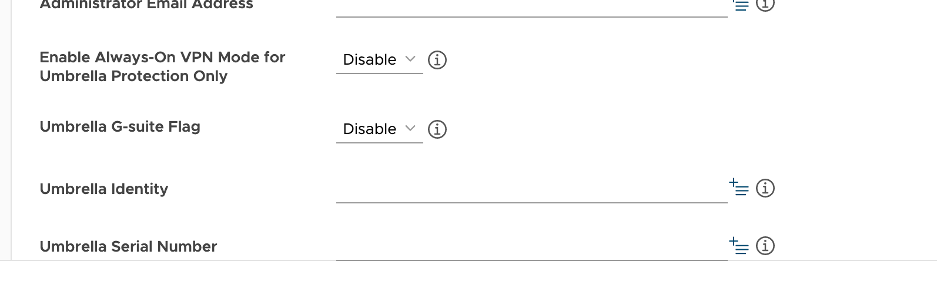
The Value can either be typed into the text box or you can be chosen from the Select Lookup Item tab.
Click LookUp for the Select Lookup Item, and then choose the appropriate variable for the identity.
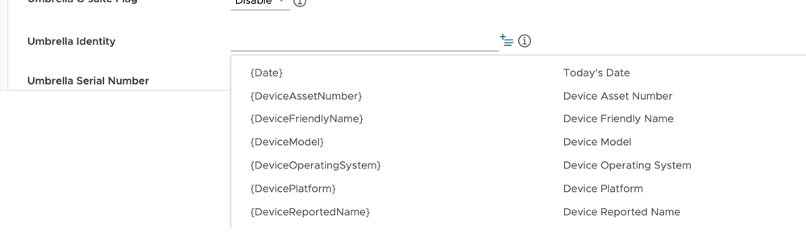
After you select the appropriate variable for the identity, the below screen appears.
Access the User Identities on the Umbrella Dashboard
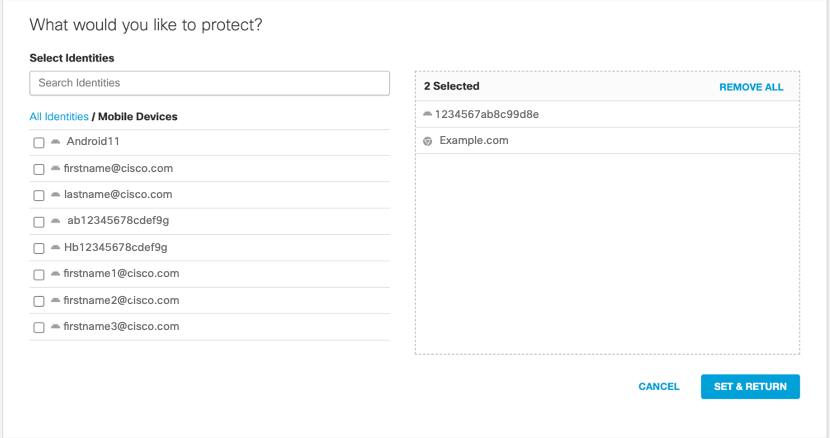
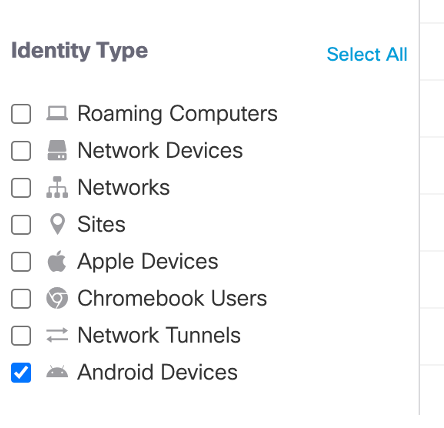
Choose the user identities for the mobile devices or add all mobile devices in your organization to the policy. Once you add the identities and Umbrella receives traffic from the mobile devices, you can view the events for the identities of the mobile devices in the Activity Search report.
Configure Policy Based on User Identity
After the user identities are shared with the Umbrella dashboard, add these identities in the policy. On the identity page, choose the identities or all mobile devices.
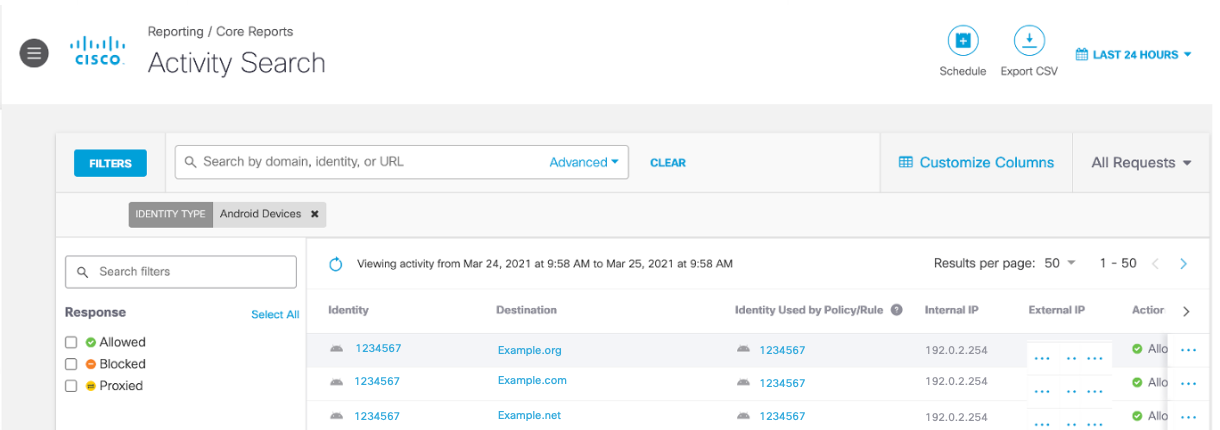
Monitor User Activity
Once the mobile device sends traffic to Umbrella, you can monitor user activity through the Activity Search report. Filter your Umbrella logs for the Android devices by selecting Android Devices.
View the user activity for the allowed and blocked traffic.
Manage Pop-Ups and App Controls < Manage Identities > Export Device Data to CSV
Updated 9 months ago
