Configure Policies
Before proceeding, if you're unfamiliar with how to configure policies, see Manage Policies.
Note: The information listed here discusses creating on-network versus off-network policies for roaming computers. If you require a single unified policy for Umbrella roaming clients, networks, and other identities for content filtering and security, and you do not require separate permissions for off-network and on-network identities, follow Umbrella's standard procedures for creating policies.
Depending on your organization's IT policies, you may wish to configure separate off-network and on-network content filtering policies. You may also disable "Content Logging", and only record security-related events in your reporting. In so doing, the end user's privacy is maintained while connected at remote locations.
The trick is to create a policy in Umbrella for the network usage and have it take priority over a similar policy for roaming.
Table of Contents
Step 1: Create an On-Network Policy
Step 2: Create an Off-Network Policy
Step 3: Order your Policies Correctly
Step 1: Create an On-Network Policy
Begin by creating the policy you would like to apply to all users—with or without the Umbrella roaming client installed—when they are on one of your local networks.
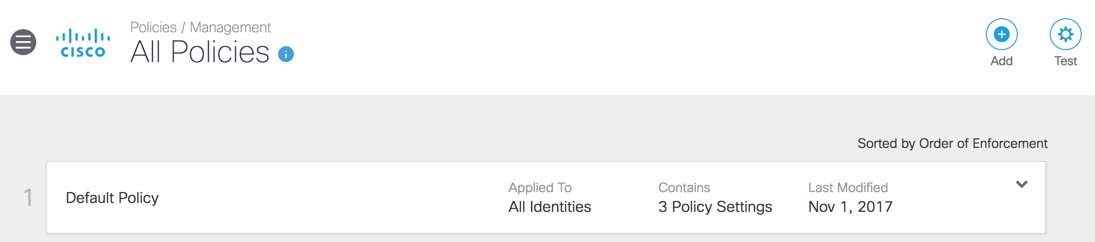
- Navigate to Policies > Management > All Policies and click Add.

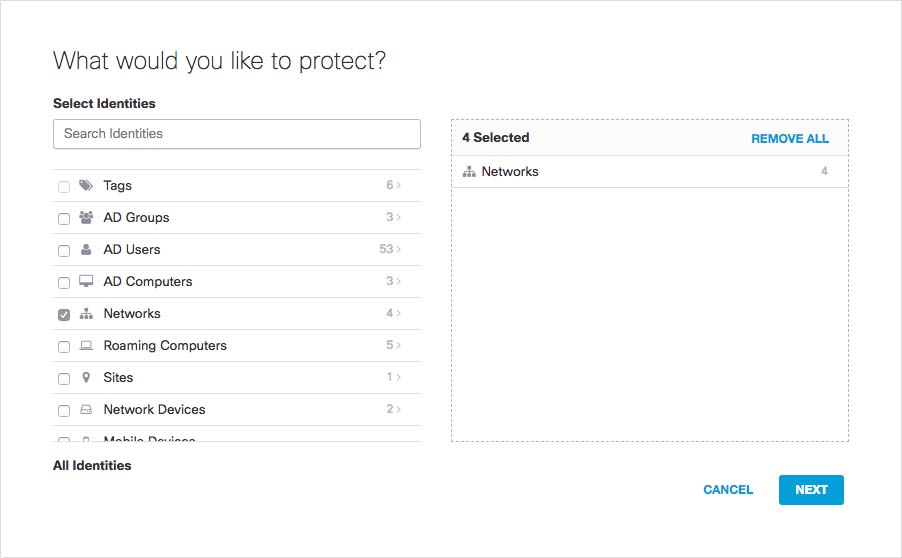
- Select Networks identities and then click Next.
Do not select Roaming Computers.
Note: You can expand an identity type to select individual identities.
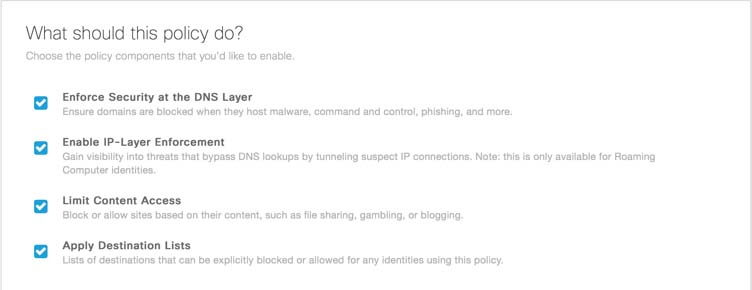
- In Step 2 of the policy wizard, select the policy features you would like to have apply on-network and then click Next.
Ensure that you select Enforce Security at the DNS Layer.
- Follow the steps of the wizard accepting default settings or make changes as required.
- In the final step of the policy wizard, give your policy a name, review your settings and click Save.
Note: It will take up to 90 seconds for the policy to be applied to your roaming computers.
Step 2: Create an Off-Network Policy
Next, create the policy you would like to apply to all users on their roaming computers when connected outside of your networks.
- Navigate to Policies > Management > All Policies and click Add.
Note: Users will be subjected to the on-network policy if connecting back to one of the networks through a VPN, which will make the computer part of the network again.
- In the first step, select all or some roaming computers, but do not select any networks.
- Click Next and in the next sections of the Policy wizard choose the content settings and security settings you would like to apply when out of the office. A common business use case is enabling the default security settings but disabling content filtering to maintain user privacy.
- Finish the wizard by selecting your desired Block Page Settings and any Bypass Codes or Users you wish to add.
- Click Next and in the final step of the policy wizard give your policy a name and click Save.
It will take up to 90 seconds for the policy to be applied to your roaming computers.
Step 3: Order Your Policies Correctly
Finally, and this is critical, make sure that your policy for networks is listed above your policy for roaming computers. Reorder policies by dragging and dropping them.
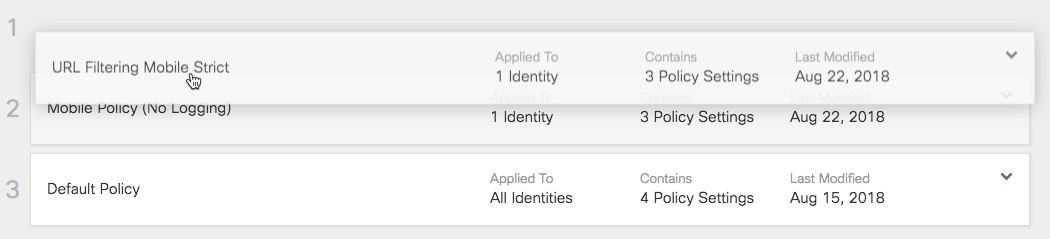
Note: When the user is on your network, the network policy takes precedence. When the roaming computer is off-network, their roaming policy takes effect.
Verify Roaming Client Operation < Configure Policies > Identity Support for the Roaming Client
Updated almost 2 years ago
