Prepare Your Active Directory Environment
To prepare for an Active Directory (AD) integration, we recommend that you deploy at least one virtual appliance before proceeding with the configuration steps. You can configure an AD integration for the Virtual Appliances by:
- Configuring the Cisco AD Connector to read login events from individual domain controllers, or
- Configuring the Cisco AD Connector to read login events from a centralized Windows Event Log Collector.
Table of Contents
- Prerequisites
- AD Integration with Domain Controllers
- AD Integration with a Centralized Windows Event Log Collector
Prerequisites
- Full Admin user role. For more information, see Manage Accounts.
- For information about the requirements for deploying the AD Connector, see Prerequisites for AD Integration with VAs.
AD Integration with Domain Controllers
Verify That Auditing of Logon Events is Enabled on the Domain Controllers
AD integration with Domain Controllers requires each domain controller to audit logon events.
On each domain controller (except read-only domain controllers), you may need to set the "Audit account logon events" to include Success and Failure if it has been set to "No Auditing." By default, this group policy is set to log Success logon events and you should not modify it. This is needed by the Umbrella software so that it knows whether a user has logged in successfully and can then compare that log in to subsequent events generated by that user.
The error you will see when running the Cisco Windows Configuration Script Cisco-WindowsConfigurationScript-20130627.wsf if the Audit Policy is not set is:
"ERROR: "
-----------------------------------------------------------------------------
Your Group Policy for this Domain Controller is set to NOT audit successful logon events!
You MUST edit the following Group Policy for all DCs:
Computer Configuration\Policies\Windows Settings\Security Settings\Local Policies\Audit Policy\Audit logon events
Define that policy to audit Success attempts, gpupdate, and re-run this script!
Run the Configuration Script on the Domain Controllers
Run the Windows configuration script on all of the domain controllers at each site, excluding read-only domain controllers (RODCs) on each domain that needs to be integrated with Umbrella. The configuration script prepares the domain controllers to communicate with the connector.
For information on changes made by the script, see Required Permissions for the Cisco_Connector User.
- Navigate to Deployments > Configuration > Sites and Active Directory and click Download.
- Click DOWNLOAD for Windows Configuration Script for Domain Controller.
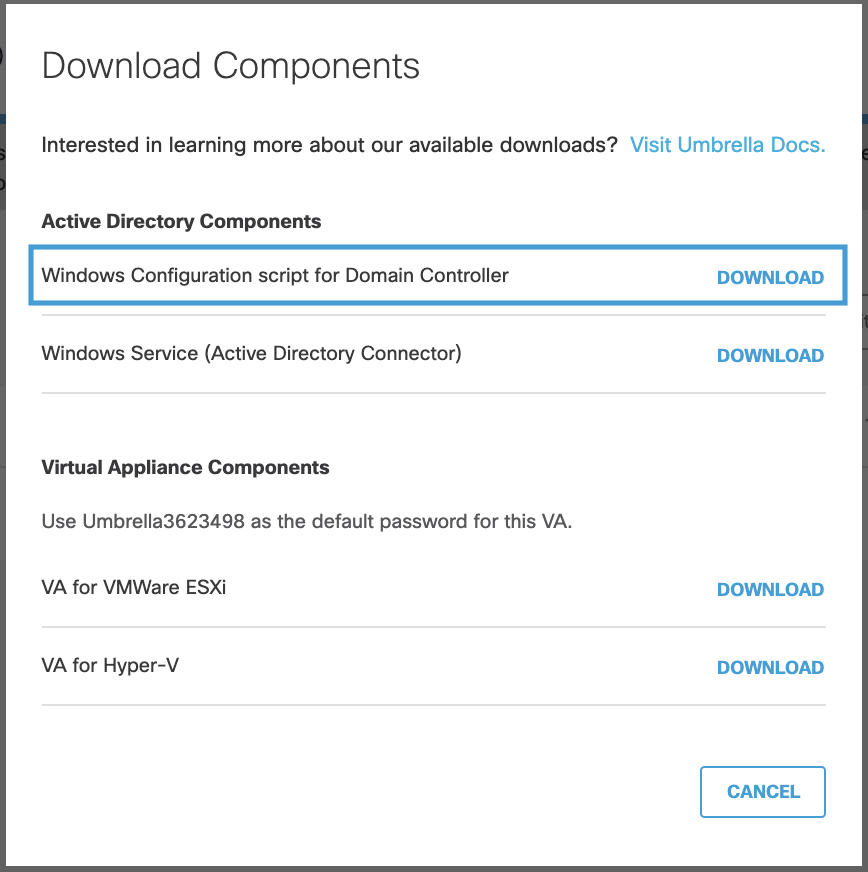
- Download and save the Windows Configuration Script file to a location on the machine where you plan to run it.
Note: The configuration script is written in Visual Basic Script and is human readable. For reference, the configuration script automates the setting of permissions captured in Required Permissions for the Cisco_Connector User. For more information, contact Umbrella Support. - As an administrator, open an elevated command prompt.
Note: The Connector user must be created before running the script, as detailed in the prerequisites. There are also several Group Policies that affect system operation that may need manual configuration. The script displays the status of these settings and, if needed, provides instructions on how to change them. - Locate the Windows Configuration Script file and run the script in the command prompt.
Note: Substitute the Windows configuration script filename (including the wsf file extension) for in the cscript command.
- Use the command:
cscript <*filename*> or cscript <*filename*> --username <sAMAccountName for custom user>
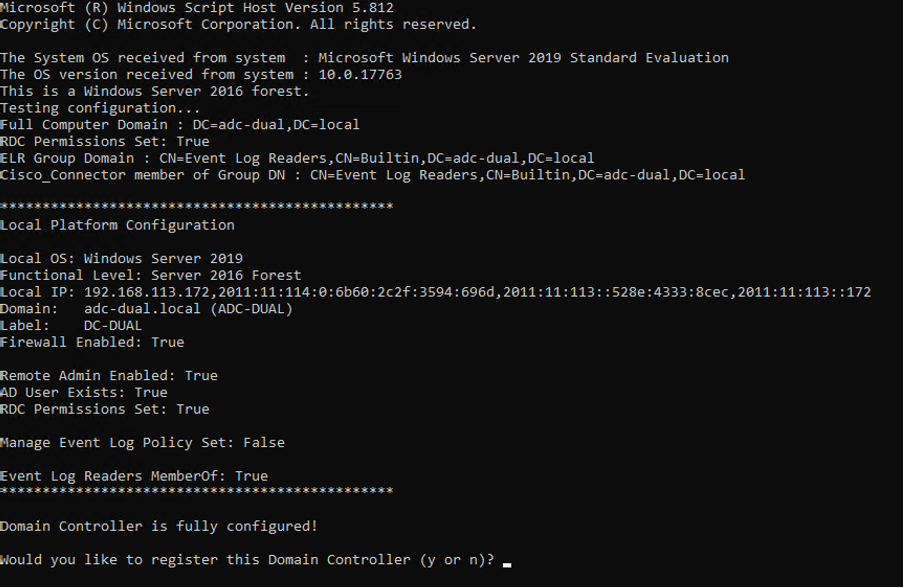
The script displays your current configuration, then offers to auto-configure the domain controller for operation. If the auto-configure steps are successful, the script offers to registers the domain controller with the Umbrella dashboard. Registration only occurs if you accept this offer.
Register a Domain Controller in the Umbrella Dashboard
The configuration script will attempt to automatically register the domain controller with Umbrella. This registration requires the domain controller to support outbound connectivity to Umbrella. If your domain controller can support outbound connectivity to the Internet, ensure that network connectivity requirements specified in Communication Flow and Troubleshooting are met for the domain controller to automatically register with Umbrella.
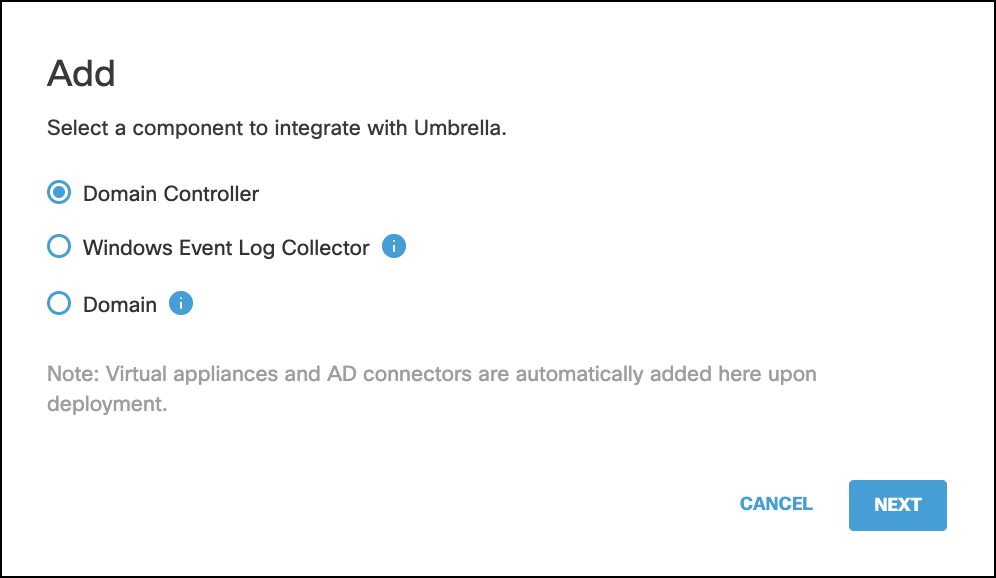
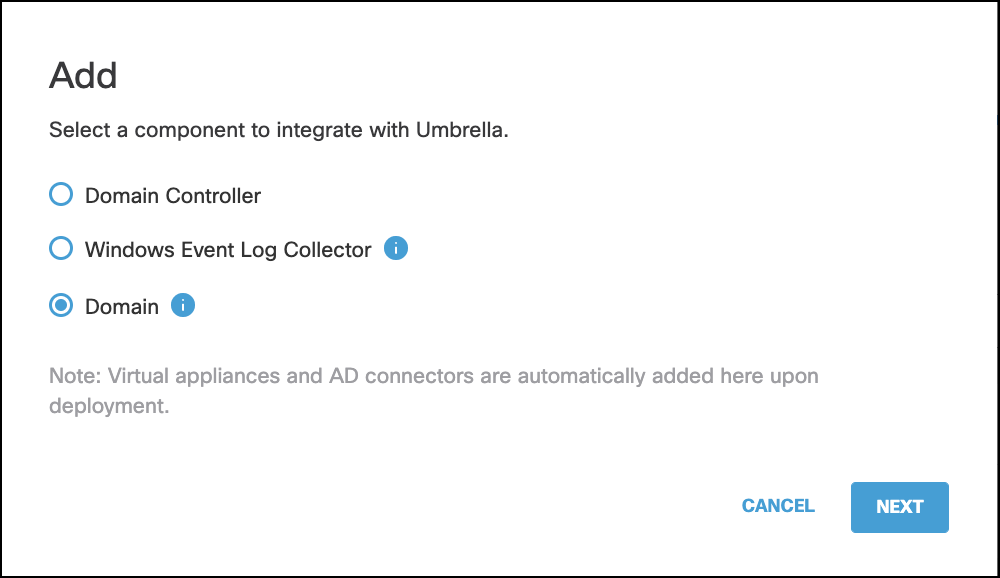
- In Umbrella, navigate to Deployments > Configuration > Sites and Active Directory and click Add.
- Select Domain Controller and click NEXT.
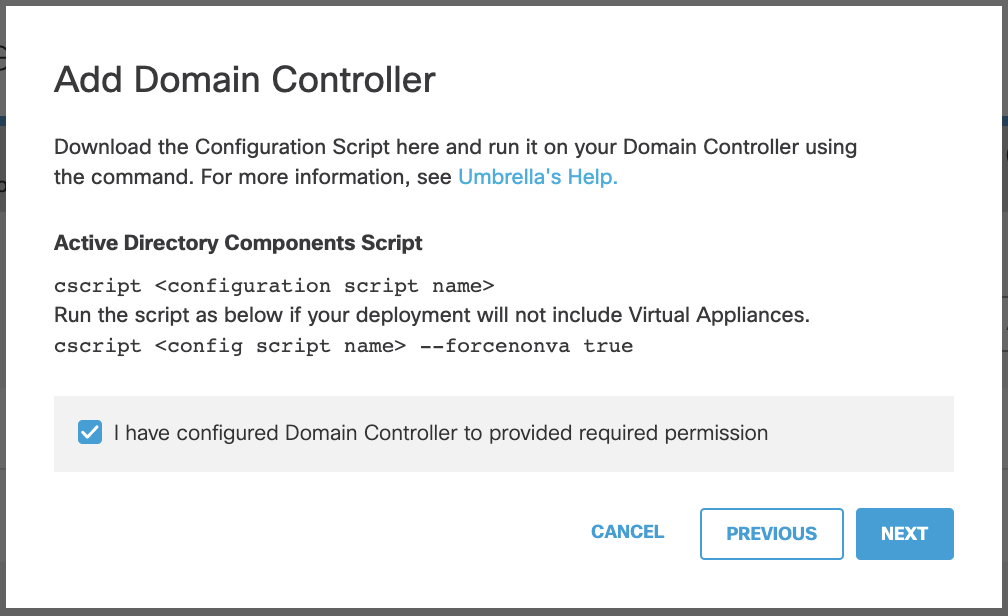
- Check the box to confirm that you have provided permissions for the Connector account and click NEXT.
-
Enter the following information:
- Enter the Hostname of the DC.
- Select IPv4 Only and then enter the internal IPv4 address of the DC.
Or
Select IPv6 Only and then enter the internal IPv6 address of the DC.
Or
Select Mixed IPv4 and IPv6 and then enter the internal IPv4 and IPv6 addresses of the DC.
Note: This option is useful for dual-stack networks. - Enter the Domain of the DC.
- Select the appropriate Umbrella site for the domain controller from the Site dropdown list.
-
Click SAVE.
Verify the Domain Controller Registration in the Umbrella Dashboard
In the Umbrella dashboard Deployments > Configuration > Sites and Active Directory.
The hostname of the domain controller you just ran the script on appears in the Inactive state. If you have configured multiple Umbrella sites and have deployed Virtual Appliances, make sure that the AD server is in the same Umbrella site as the VAs that will receive DNS queries from the users in that AD domain.
Repeat the steps in Register a Domain Controller in the Umbrella Dashboard to prepare additional DCs in each AD domain environment to communicate with the connector successfully. It is essential that each domain controller in each AD domain environment has the configuration script run on it in order for the service to work as expected, both for high availability and overall reliability.
Note: The configuration script only runs once; it is not an application nor a service. If you change the IP address or hostname of the domain controller, remove the previous instance of the domain controller and repeat step 1 through 5 to re-register the domain controller.
Multi-AD domain and Multi-Forest Support
If you wish to integrate multiple AD domains or AD forests with Umbrella through integrations with domain controllers, then a connector deployment (with an additional connector for redundancy) is required for each AD domain that needs to be integrated with Umbrella.
AD Integration with a Centralized Windows Event Log Collector
If you have already deployed a centralized Windows Event Log Collector where domain controllers are forwarding login events, you can use that for AD integration with Umbrella. A single Windows Event Log Collector where login events are being forwarded for multiple AD domains or AD forests can be integrated for these AD domains.
Note: Setting up a centralized Windows Event Log Collector is outside the scope of Umbrella. Refer to Microsoft documentation for the same.
Step 1 – Additional Prerequisites
- The connector account (Cisco_Connector or custom account as configured) should be added to the local Event Log Readers group on the Windows Event Log Collector machine.
- The following firewall rules need to be enabled on the Windows Event Log Collector machine to allow the connector machine to read the logs:
- Remote Event Log Management (NP-In)
- Remote Event Log Management (RPC)
- Remote Event Log Management (RPC-EPMAP)
- All network access requirements specified in Communication Flow and Troubleshooting should be met.
Step 2 – Register the Windows Event Log Collector with Umbrella
You will need to manually add the Event Log Collector on the Umbrella dashboard.
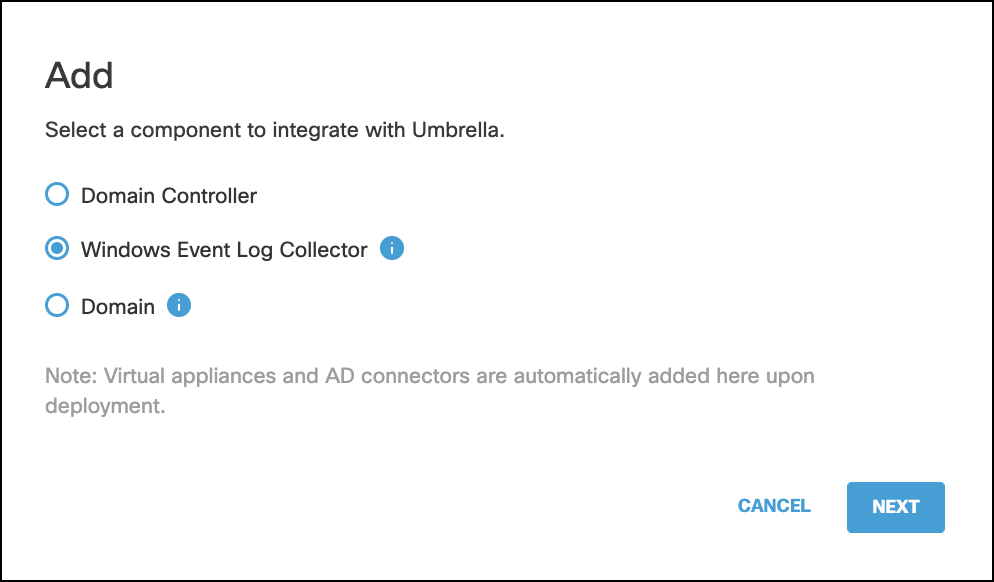
- In the Umbrella dashboard, navigate to Deployments > Configuration > Sites and Active Directory and click Add.
- Select Windows Event Log Collector and click NEXT.
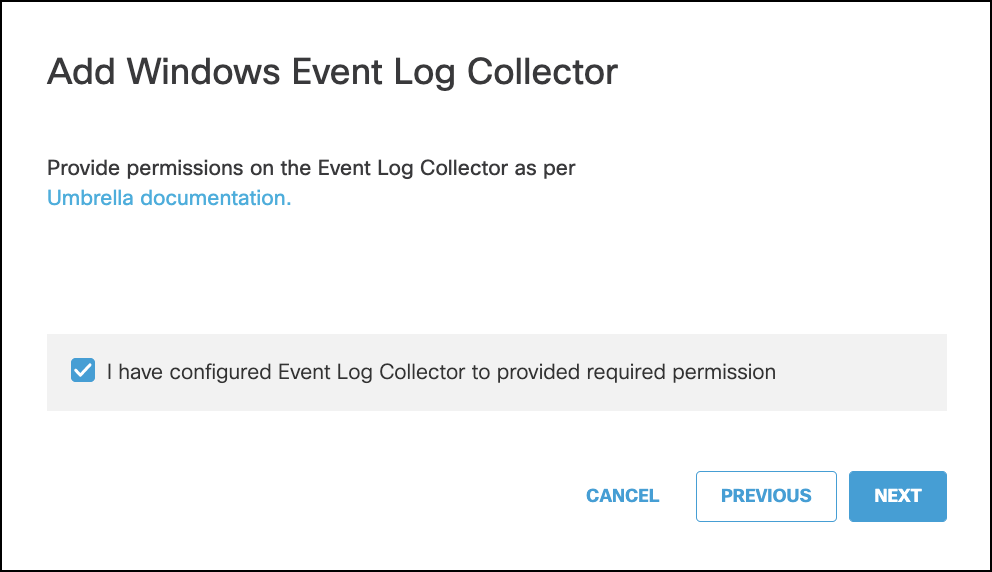
- Check the box to confirm that you have provided the required permissions on the Event Log Collector and click NEXT.
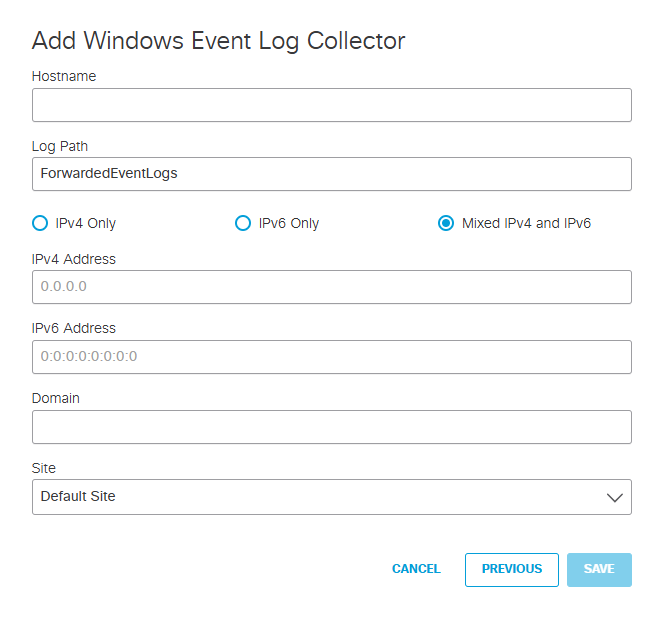
-
Enter the following information:
- Enter the Hostname of the DC.
- Select IPv4 Only and then enter the internal IPv4 address of the DC.
Or
Select IPv6 Only and then enter the internal IPv6 address of the DC.
Or
Select Mixed IPv4 and IPv6 and then enter the internal IPv4 and IPv6 addresses of the DC.
Note: This option is useful for dual-stack networks. - Enter the Domain of the DC.
- Select the appropriate Umbrella site for the domain controller from the Site dropdown list.
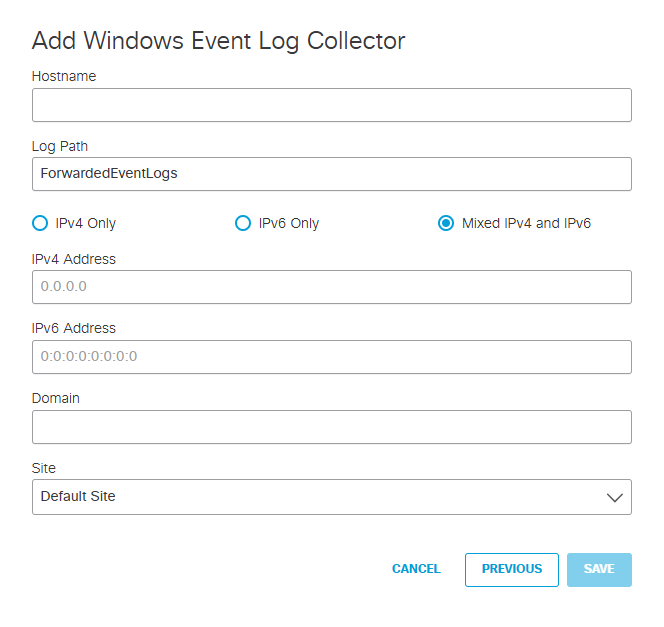
-
Click SAVE.
Step 3 – Register the AD Domains with Umbrella
You will need to register each AD domain for which logon events are being sent to the Windows Event Log Collector. This registration is required for the connector to be able to retrieve the list of AD users, groups, and computers from these individual AD domains.
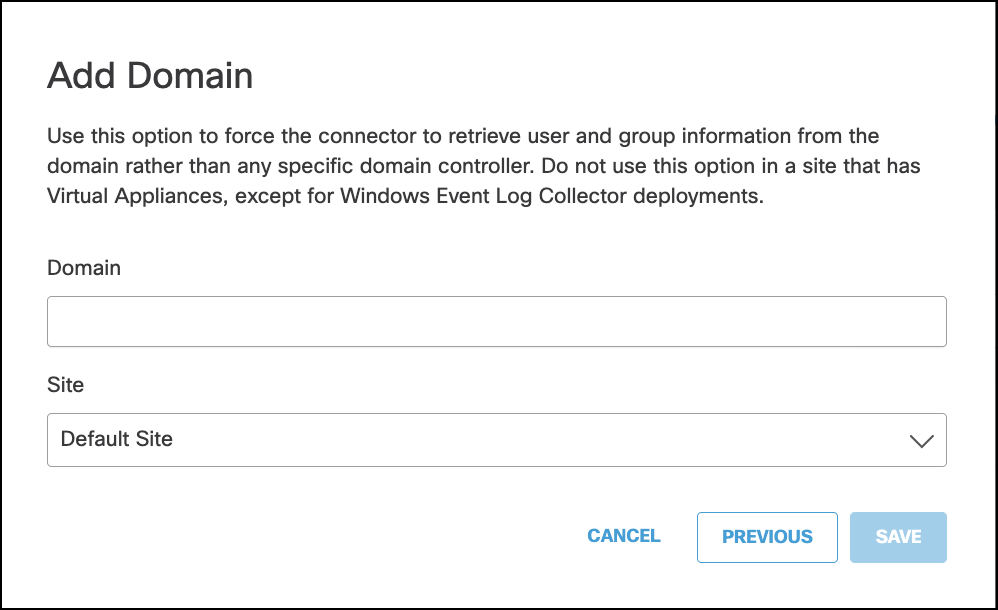
- In the Umbrella dashboard, navigate to Deployments > Configuration > Sites and Active Directory and click Add.
- Select Domain and click NEXT.
- Enter the Domain, select the appropriate Umbrella Site for the domain and click SAVE.
Configure Active Directory User Exceptions < Prepare Your Active Directory Environment > Connect Active Directory to Umbrella VAs
Updated 5 months ago
