Enable SSO with Okta
To enable single sign-on (SSO) with SAML for Umbrella, you must first add the Okta app for Umbrella to your organization, then follow a step-by-step wizard to complete the process in Umbrella.
Prerequisites
- Full admin access to the Umbrella dashboard. See Manage User Roles.
Procedure
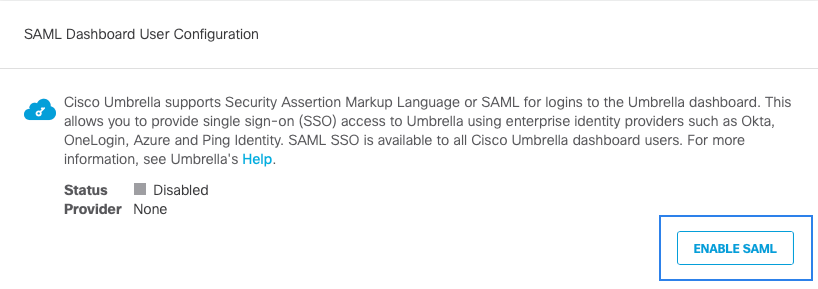
- Navigate to Admin > Authentication.

- In the SAML Dashboard User Configuration section, click Enable SAML.
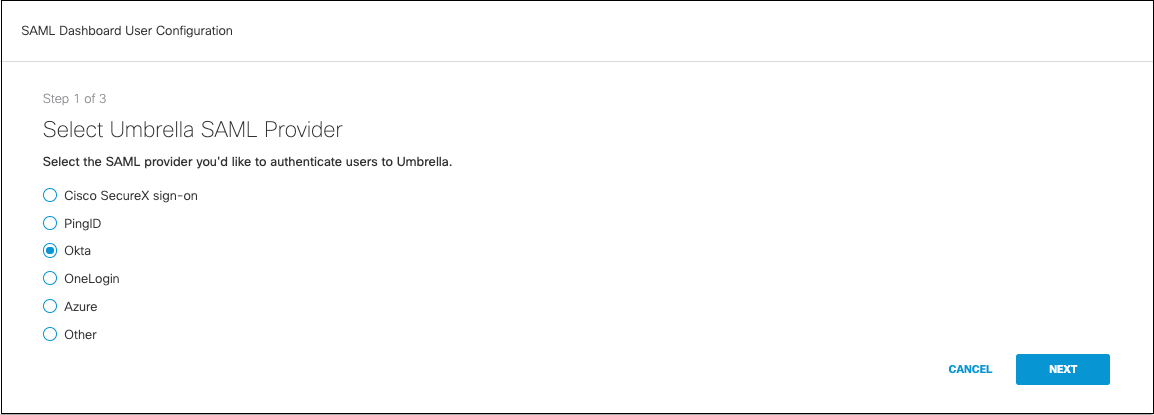
- Choose Okta and click Next.
- Download the Okta XML metadata file:
a. Log into your Okta dashboard as the user you want to configure for Umbrella and go to the Admin tab. It's best if you start by logging into the Okta dashboard with the same account you are using in the Umbrella dashboard.
b. Click Applications and then click Add Application. Search for “Cisco Umbrella” and click Add.
c. Assign an easily identifiable label for the Application, keep defaults as is for General Settings, and then click Next.
d. Under Sign-On Methods, select SAML 2.0. You can disable force authentication here. Click the Identity Provider metadata and save the downloaded metadata file. You will need this in step 3 of the Umbrella setup wizard.
e. Return to the Sign-On Options and from the Application Username Format drop-down list, choose Email and then click Next.
f. Assign the application to one or more users. All accounts that need to access the dashboard now or in the future should be selected here and have the application assigned to them or they will not be able to log in.
Ensure the proper user attributes have been enabled for each account, specifically the username (email). The email must match exactly the email that's used to log into Umbrella.
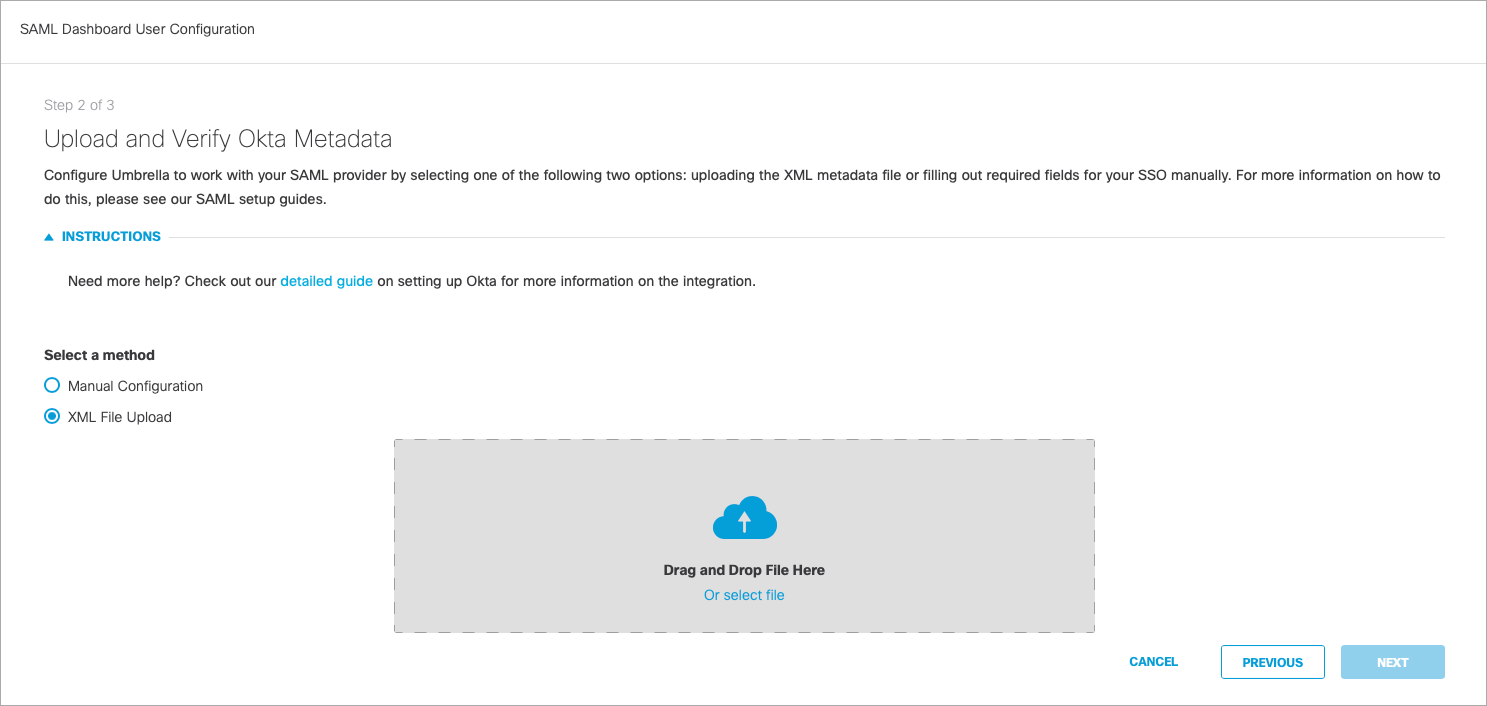
- In Umbrella, navigate to Admin > Authentication and proceed to Upload and Verify Okta Metadata. Select XML File Upload, upload the metadata file you downloaded from Okta, and then click Next.
- Click Test Your SAML Configuration and enter the Umbrella email for your current logged in user that was added to the Okta application. After the test completes, a success message should be displayed. All authentication to the Umbrella dashboard for all users in your organization is now handled by Okta.
Enable SSO with Duo < Enable SSO with Okta > Enable SSO with PingID
Updated almost 2 years ago
