Connect Active Directory to Umbrella
The Cisco Active Directory (AD) Connector integrates Cisco Umbrella with your instance of Microsoft AD. Before you can provision users and groups from Active Directory, connect your instance of AD to Umbrella by deploying an AD Connector.
This guide describes the steps to install the Cisco AD Connector for LDAP or LDAPS, and provision users and groups from your instance of Microsoft AD to Umbrella.
How to Configure the Setup of the AD Connector
The deployment of the AD Connector has various components. You can configure the Cisco AD Connector to provision users and groups from Microsoft AD using LDAP or LDAPS (domain controller or domain), or LDAP Interchange Format (LDIF) source files.
- (Optional) Configure authentication for the AD Connectors in your environment. For more information, see Configure Authentication for AD Connectors and VAs.
- Add a domain controller or domain in Umbrella for LDAP or LDAPS deployments.
- Download the software package for the AD Connector and install it on your server.
- (Optional) Configure the provisioning of users and groups with LDIF source files. For more information, see Deploy LDIF Files for Cisco AD Connector.
- Verify that the AD Connector begins to provision users and groups in Umbrella.
Table of Contents
- Prerequisites
- Register a Domain Controller or Domain in the Umbrella Dashboard
- Register a Domain Controller
- Register a Domain
- Specify AD Groups of Interest (Optional)
- Install the Connector
- Verify That the Connector Syncs with the Umbrella Dashboard
Prerequisites
- Full Admin user role. For more information, see Manage Accounts.
- For information about the requirements for deploying the AD Connector, see Prerequisites for AD Connectors.
- (Optional) Configure Authentication for AD Connectors and VAs.
Register a Domain Controller or Domain in the Umbrella Dashboard
Active Directory integration requires you to register an AD domain controller or AD domain in the Umbrella dashboard. The Connector will perform an LDAP sync against this domain controller or domain to retrieve the user and group identities. The Connector Server must be able to communicate with the domain controller over port 389/636 TCP for LDAP sync or LDAP over SSL.
The Connector can only retrieve user and group identities from a single domain controller. If you register multiple domain controllers on the Umbrella dashboard, the Connector will only attempt to perform an LDAP sync against the first domain controller in the list. Ensure that the domain controller you are registering is not subject to any AD replication delays. Read-only Domain Controller (RODC) registrations are supported for retrieval of user and group identities.
If you need to periodically bring down your domain controller for maintenance or updates or your domain controllers are behind a load balancer that does not support LDAP queries, it is recommended to register the domain instead.
Note: If you have deployed any virtual appliances, you need to register all of your domain controllers that are handling Active Directory authentication. Otherwise, not all users and groups in the Active Directory will be identified.
Register a Domain Controller
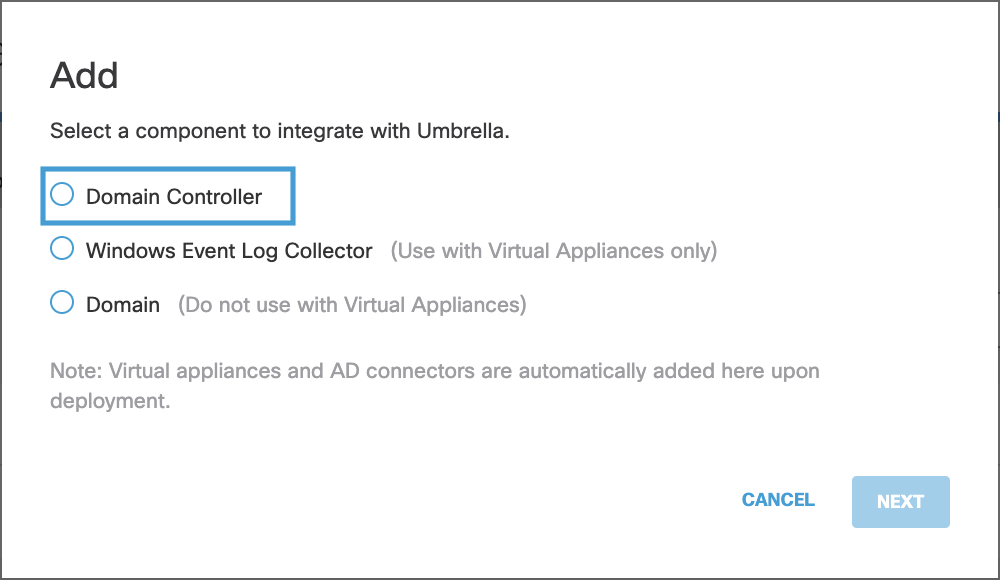
- Navigate to Deployments > Configuration > Sites and Active Directory and then click Add.

- Select Domain Controller and click NEXT.
-
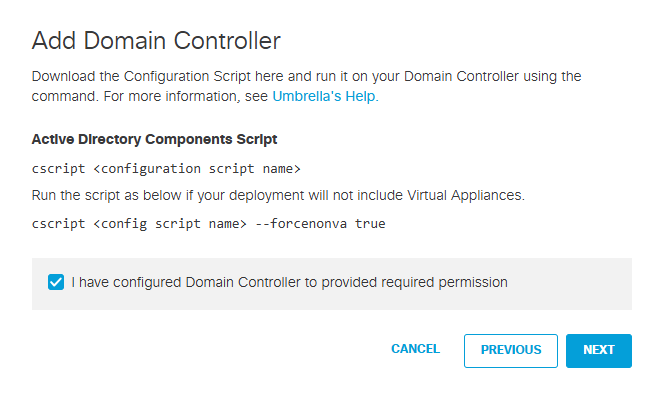
Confirm that you have provided permissions for the Connector account as specified in Prerequisites and click NEXT.
-
Enter the following information:
- Enter the Hostname of the DC.
- Select IPv4 Only and then enter the internal IPv4 address of the DC.
Or
Select IPv6 Only and then enter the internal IPv6 address of the DC.
Or
Select Mixed IPv4 and IPv6 and then enter the internal IPv4 and IPv6 addresses of the DC.
Note: This option is useful for dual-stack networks. - Enter the Domain of the DC.
- Select the appropriate Umbrella site for the domain controller from the Site dropdown list.
-
Click SAVE.
The Active Directory connector within the chosen Umbrella site will attempt to connect to your newly added domain controller. If all the required permissions have been configured, you should not experience any issues. If there are errors, review Prerequisites or contact Support.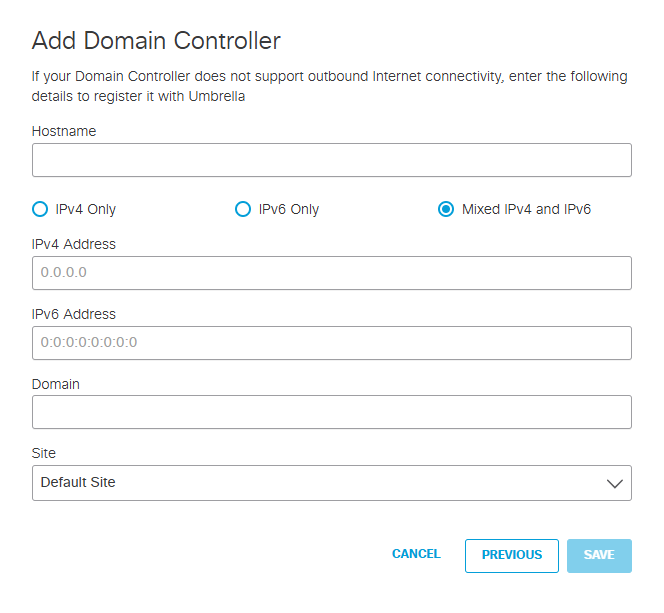
Note: As the ApiGw service is limited to IPv4 networks, the registration and synchronization processes for both the AD Connector and Domain Controller fails on a pure IPv6 network.
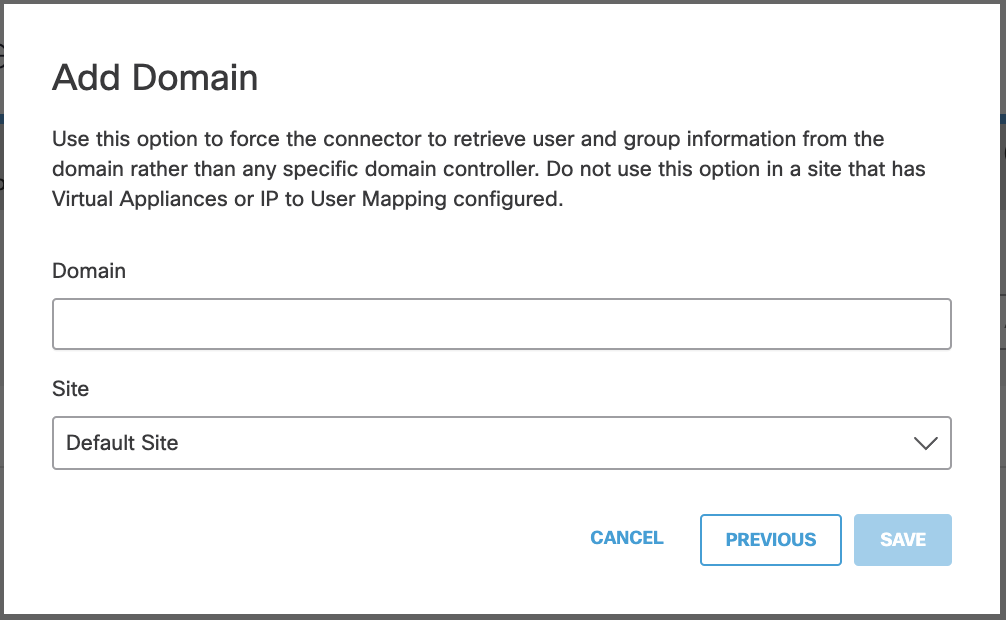
Register a Domain
- Navigate to Deployments > Configuration > Sites and Active Directory and click Add.
- Select Domain and click NEXT.
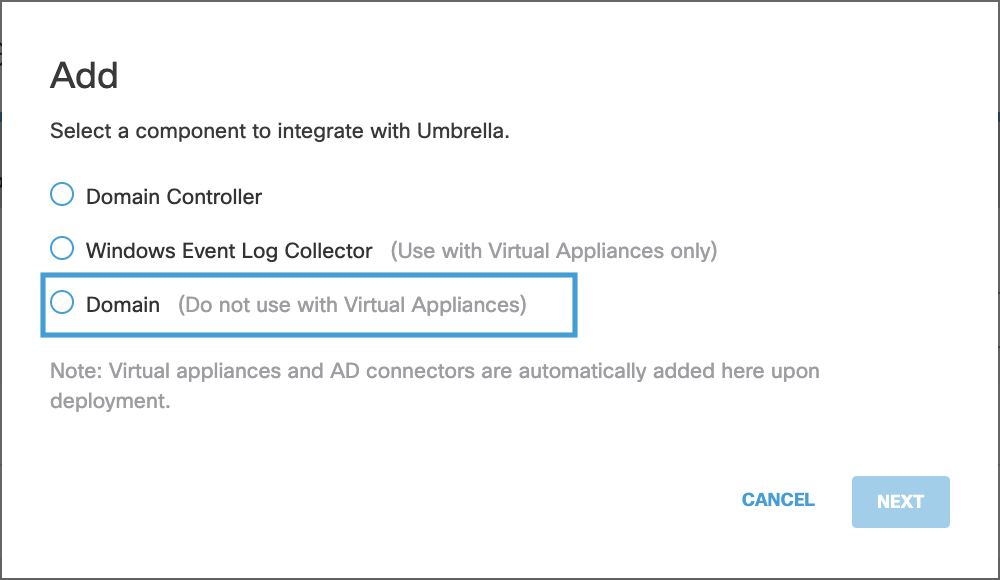
- Enter the Domain, select the appropriate Umbrella Site for the domain and click SAVE.
Specify AD Groups of Interest (Optional)
Optionally, you can specify AD Groups of interest for the purpose of policy creation in Umbrella.
Rename Selective Sync File After Upgrading to AD Connector v1.14.4
If you use selective sync and upgrade the Cisco AD Connectors to v1.14.4 or later, you must rename the current selective sync file C:\CiscoUmbrellaADGroups.dat to C:\CiscoADGroups.dat.
Note: The selective sync file—previously named CiscoUmbrellaADGroups.dat—is not recognized by the Cisco AD Connector v1.1.4.4 or later.
After you rename the selective sync file, Umbrella automatically reads the selective sync file (C:\CiscoADGroups.dat) and syncs the Users in the specific Groups from AD to Umbrella. You are not required to restart the AD Connector service.
Create AD Groups in a Selective Sync File
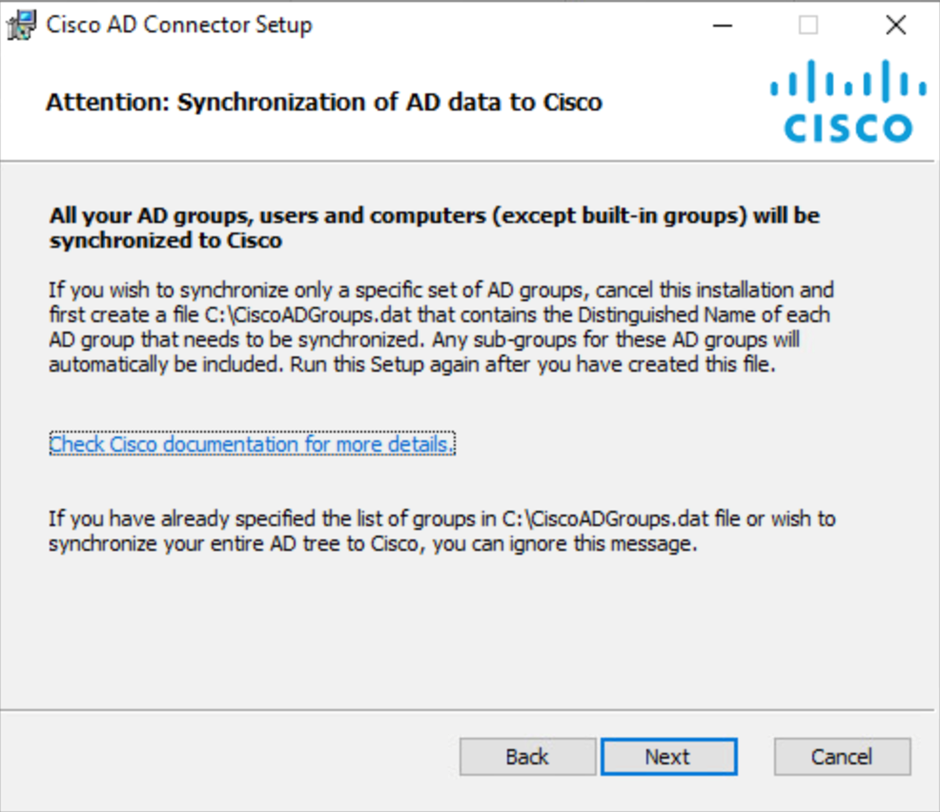
- Identify the AD groups of interest. Users and computers belonging to these groups will be synchronized to Umbrella.
For each sub-tree, only the parent group needs to be specified. All AD groups, users, and computers that are part of this parent group will automatically be included.
Note: If Selective Sync is enabled, AD Users and Computers that are not members of Groups specified in CiscoADGroups.dat or their sub-groups not be synchronized to Umbrella and will be completely exempt from Umbrella Policies and Reporting. - Create a CiscoADGroups.dat file in the C:\ drive of each machine where the connector will be installed.
The connector will only read the C:\CiscoADGroups.dat file. If the file is incorrectly named or is not present in the C:\ drive, all groups will be imported to Umbrella. - List the AD groups that need to be synchronized in distinguished name (DN) format in this file.
Supported OUs
Not Supported: OU=My OU,OU=Organizational Unit,DC=sample,DC=local
Supported: CN=My Group,OU=Organizational Unit,DC=sample,DC=localSample file entries:
- CN=Engineering,CN=Builtin,DC=ciscoumbrella,DC=com
- CN=Sales,CN=Builtin,DC=ciscoumbrella,DC=com
- CN=Marketing,CN=Builtin,DC=ciscoumbrella,DC=com
- Ensure that there are no blank lines anywhere in the file.
Note: If you are running multiple connectors, the file C:\CiscoADGroups.dat should be present on each system running the connector and should be identical on each system.
Total Number of Groups Selected for Synchronization
The total number of groups selected for synchronization—groups specified in the selective sync file and all their sub-groups—should not exceed 15,000. Also, these groups should not be nested within more than five OU levels. Selective synchronization fails in both cases. If either of these requirements cannot be met, the selective sync file should not be used so that a full AD tree synchronization can be done instead.
Install the Connector
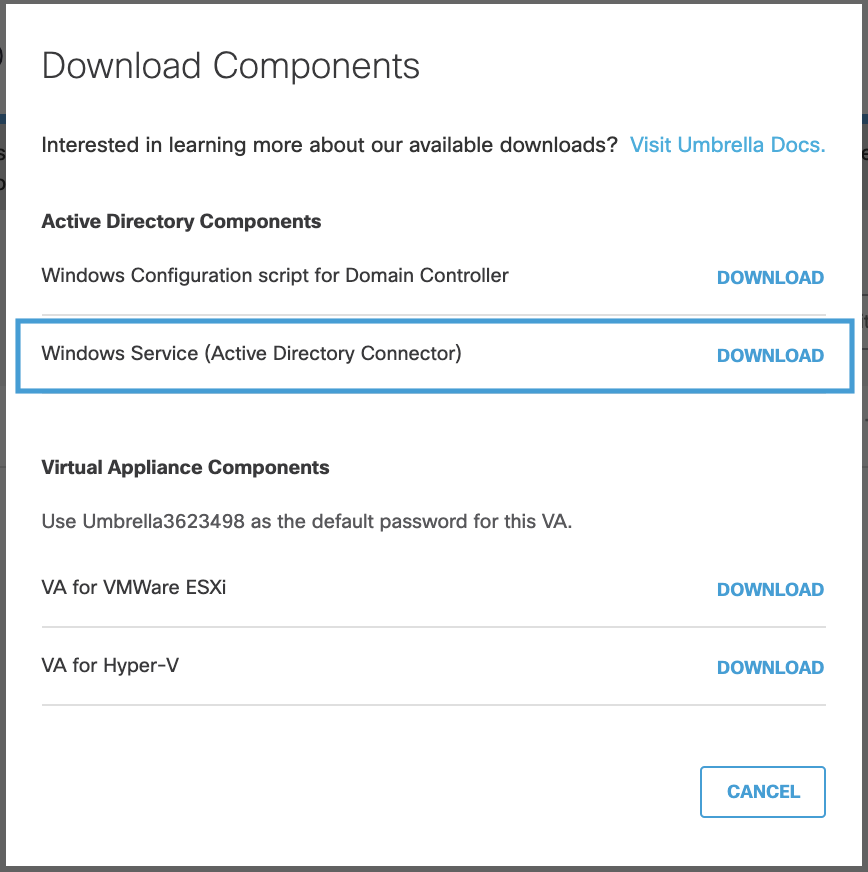
- On the server that you have configured to deploy the connector, login to the Umbrella dashboard, navigate to Deployments > Configuration > Sites and Active Directory and click Download.
- Click DOWNLOAD for Windows Service (Active Directory Connector).
Note: You must download the ZIP file to the local machine where you plan to run it or copy it locally from another machine. Issues have been observed attempting to install the connector from networked drives as well as running the Setup.msi directly from the compressed file.
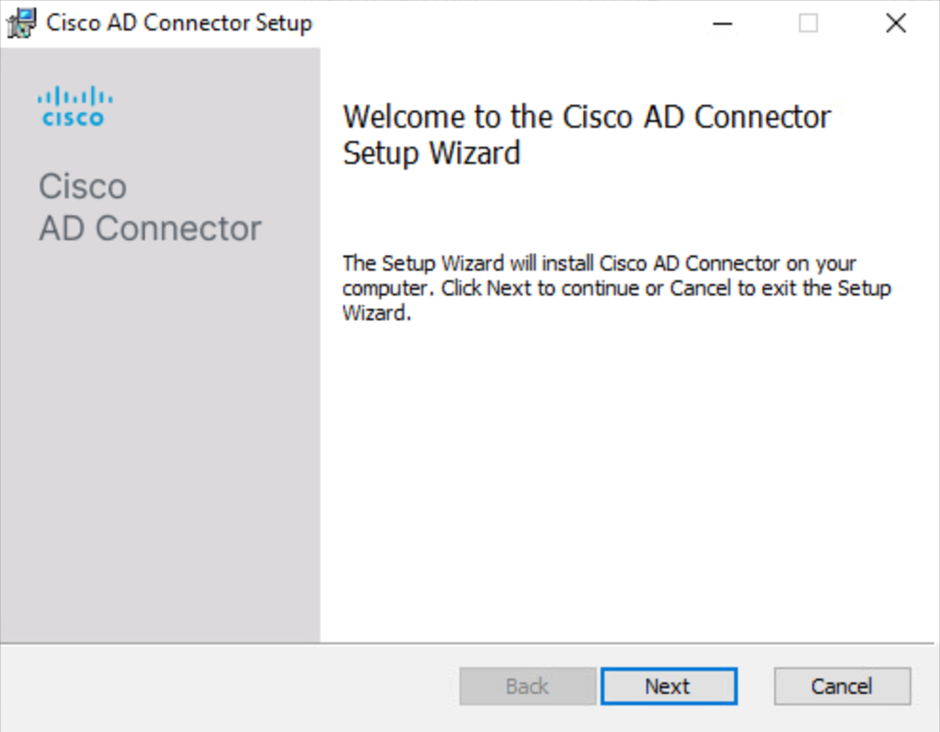
-
As an administrator, extract the contents of the Cisco-Windows-Service ZIP file that you downloaded from Secure Access to a folder on the server, and then navigate to that folder.
Note: If you run the AD Connector installer files from the root directory of your server, you may encounter installation errors. -
Run Setup.msi, and then in the Cisco AD Connector Setup wizard, click Next.
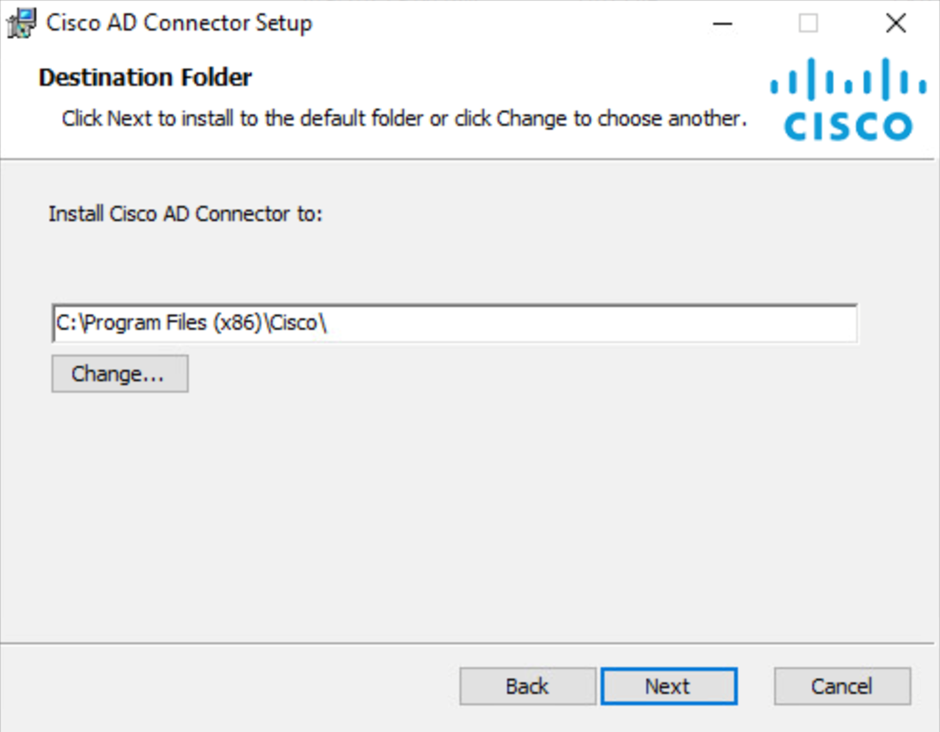
-
Choose the directory on the server to install the Cisco AD Connector and then click Next.
-
Select AD Lookup (using LDAP/LDAPS) and then click Next to provision identities using LDAP lookup of the Domain Controller or Domain registered on the same site.
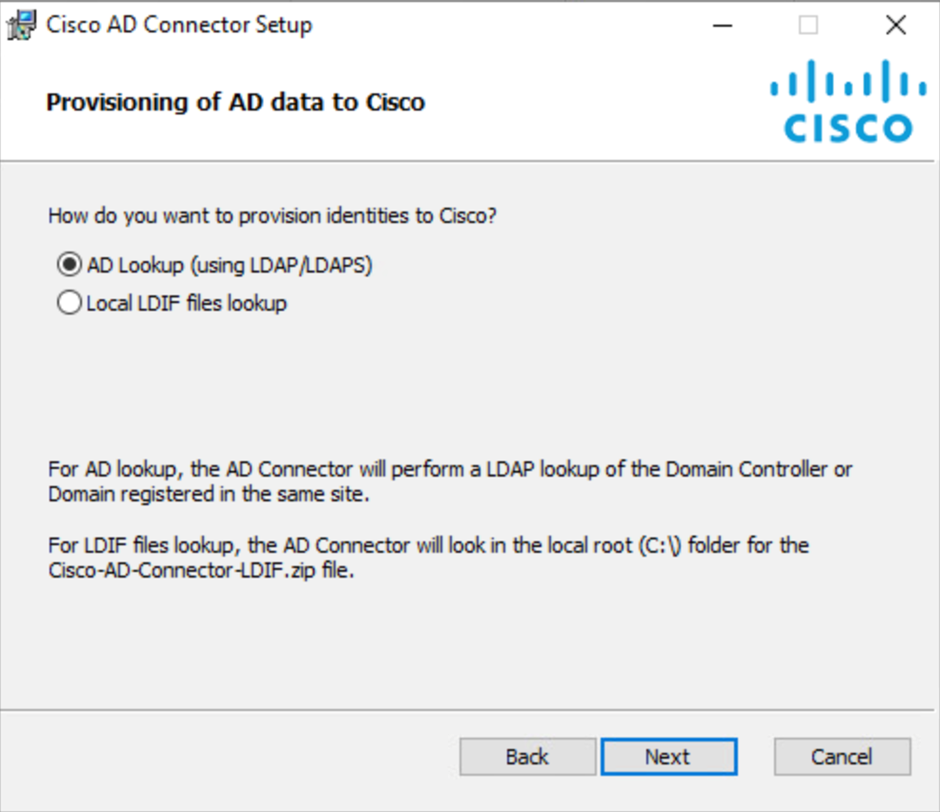
You can also select Local LDIF files lookup to provision identities using Cisco-AD-Connector-LDIF.zip file in the local root folder. To use this option refer to Deploy LDIF Files for AD Connector.
-
Click Next to confirm that you permit your AD Users and Groups to sync to Secure Access from the Cisco AD Connector.
-
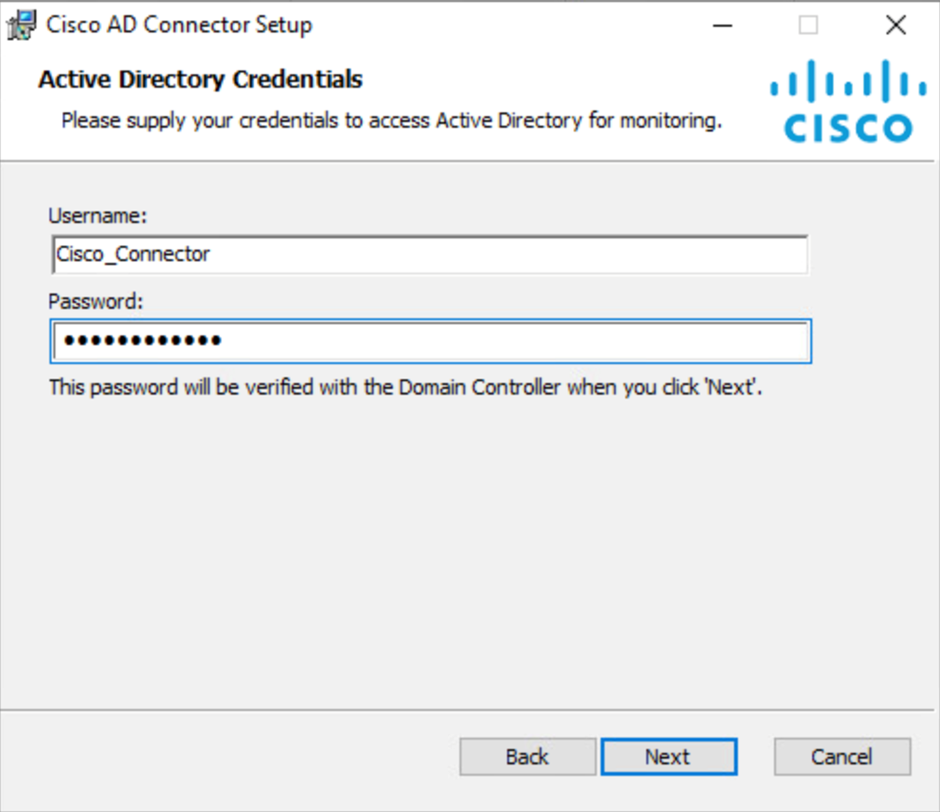
Add your Active Directory credentials. Enter the Username of the Cisco AD Connector user (Cisco_Connector or custom username), the Password, and then click Next. For more information, see Prerequisites.
-
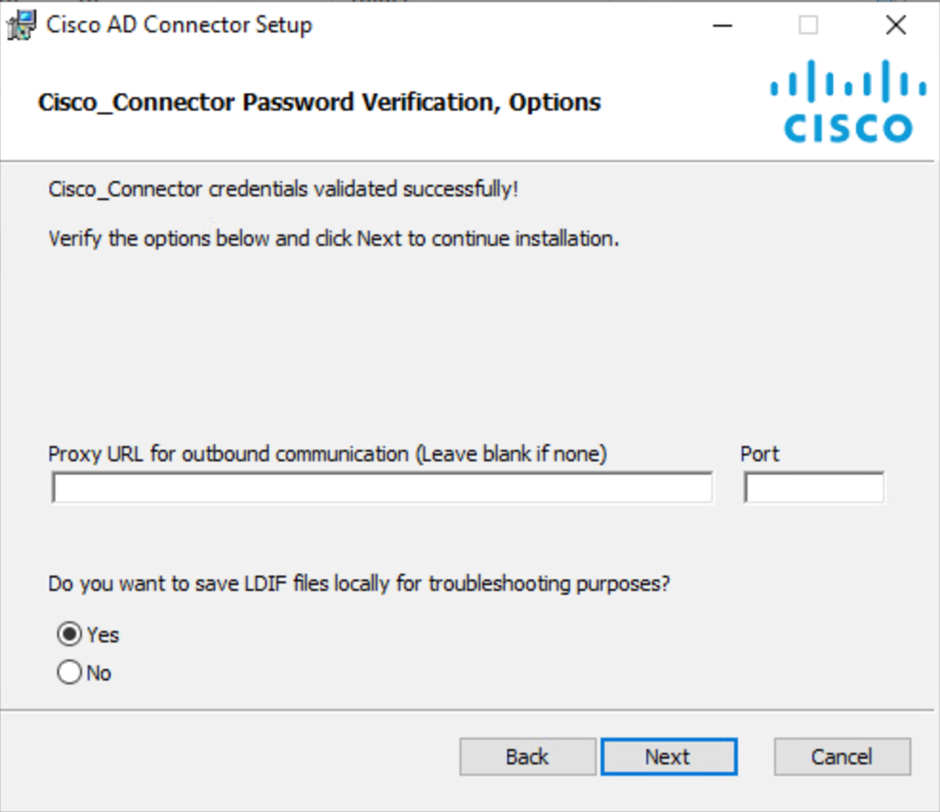
(Optional) Enter the Proxy URL and port for the outbound communication.
-
(Optional) Choose the appropriate option if you want to save LDIF files locally.
-
Click Next and then click Install.
-
Once the setup is complete, click Finish.
Return to the Umbrella dashboard. Verify that the Cisco AD Connector is in the same Umbrella site as the domain controller or domain that it needs to communicate with.
Verify That the Connector Syncs with the Umbrella Dashboard
- For more information, see View AD Components in Umbrella.
Configure Updates on AD Connectors < Connect Active Directory to Umbrella > Deploy LDIF Files for AD Connector
Updated 5 months ago
