Add Network Tunnel Identity
A network tunnel identity enables you to manage and monitor traffic sent from an IPsec (Internet Protocol Security) IKEv2 (Internet Key Exchange, version 2) tunnel in your environment to Umbrella. Before Umbrella can begin to receive traffic from a network tunnel, you must add the tunnel to Umbrella as a network tunnel identity. Then, after you create the tunnel identity, configure and deploy the IPsec tunnel in a compatible network device.
Once Umbrella receives and logs traffic from the network tunnel, the tunnel is considered active. When you apply the network tunnel identity to an Umbrella Web or firewall policy rule, Umbrella can observe the state of the tunnel and report on traffic sent from the tunnel. View the events for the tunnel in the Umbrella Activity Search report.
Table of Contents
- Prerequisites
- Procedure
- Configure Network Tunnel
- Verify Tunnel Traffic in Umbrella
- Add Tunnel to Umbrella Policies
Prerequisites
- Umbrella organization ID. For more information, see Find Your Organization ID.
- Cisco Umbrella SIG Essentials subscription or a free SIG trial.
Procedure
- Navigate to Deployments > Core Identities > Network Tunnels and click Add.
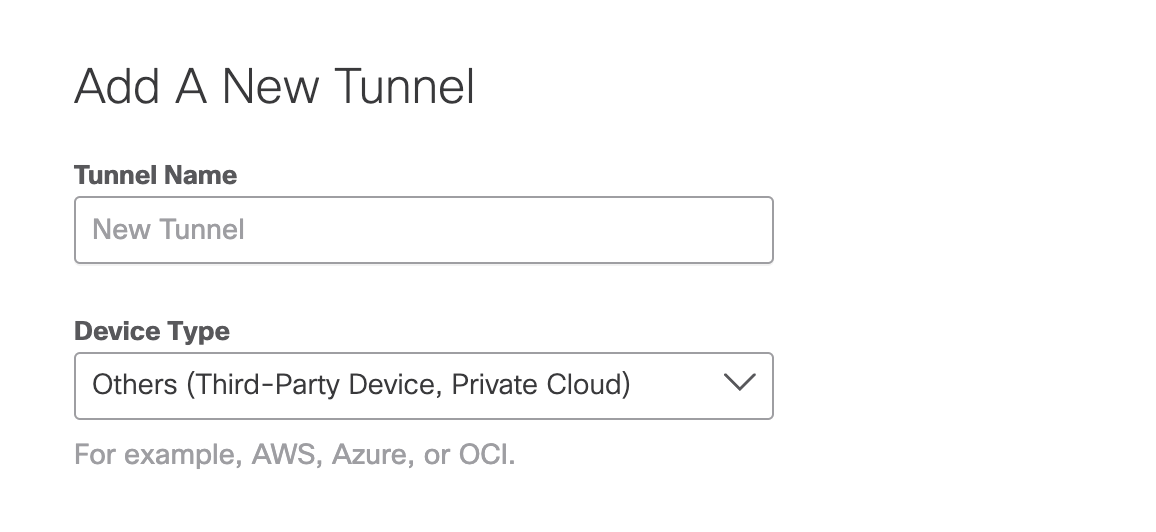
- Give your tunnel a meaningful name and choose Others from the Device Type drop-down menu.
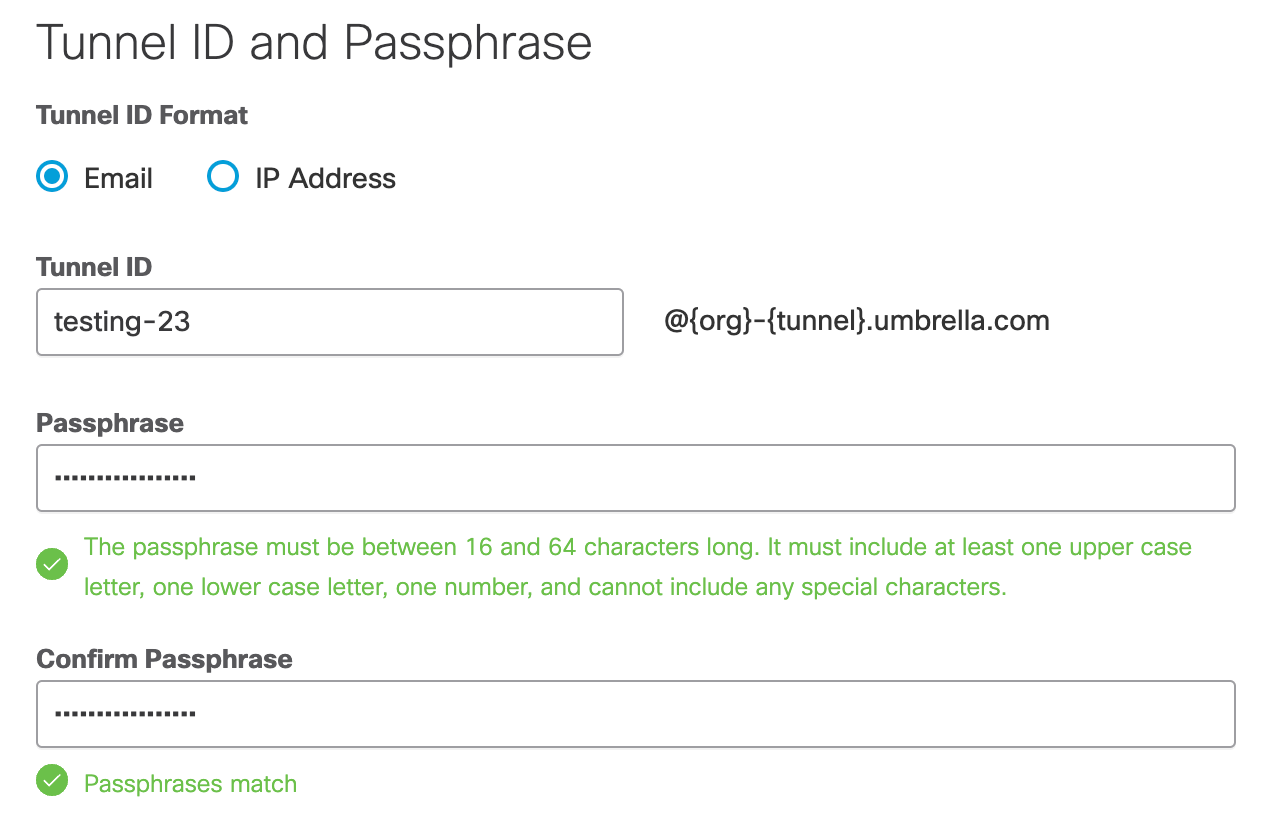
- Select Email or IP Address for the Tunnel ID Format. Add the Tunnel ID and create a passphrase.
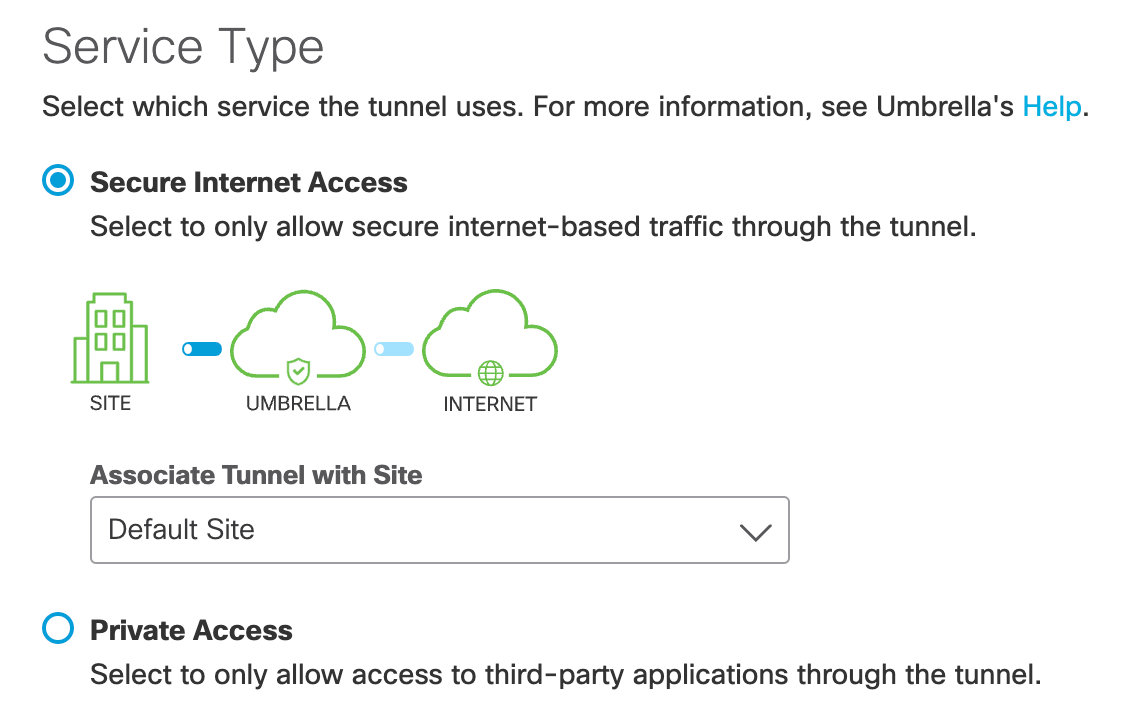
- Select Secure Internet Access for Service Type.
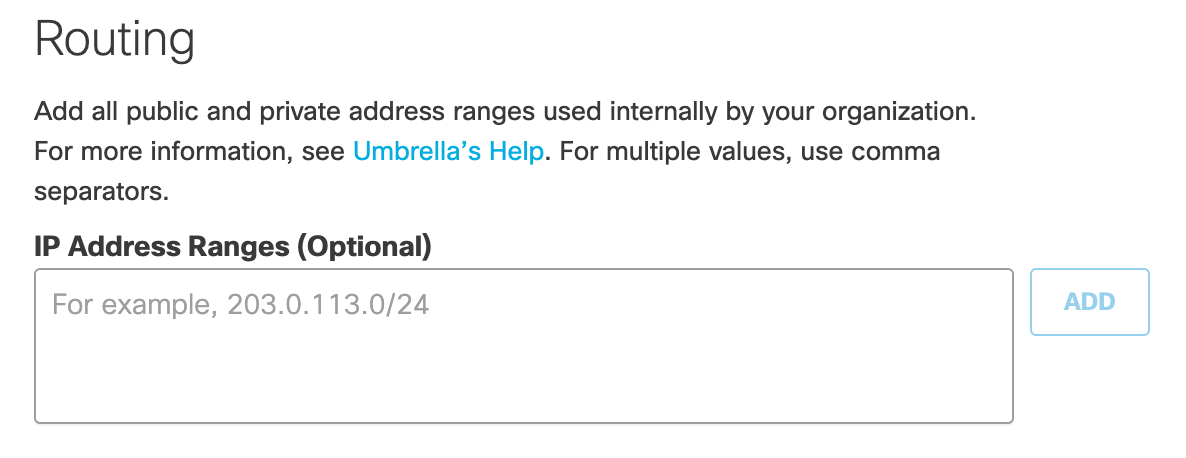
- (Optional) Add public and private IP address ranges.
- Copy the Tunnel ID and passphrase and click Save.
Use the tunnel ID and passphrase to configure and deploy a tunnel in a network device.
Configure Network Tunnel
- Follow the steps in one of the device guides to deploy an IPsec tunnel with Umbrella. For more information see Network Tunnel Configuration.
Verify Tunnel Traffic in Umbrella
After you add a tunnel identity to Umbrella and deploy a network tunnel with a compatible network device, check that Umbrella receives and logs traffic from the tunnel.
- Navigate to Deployments > Core Identities > Network Tunnels and find your configured tunnel. Verify that the Tunnel Status is Active.
- Navigate to Reporting > Core Reports > Activity Search.
Search for the tunnel by identity by name to view the traffic for the tunnel.
Add Tunnel to Umbrella Policies
Manage your IPsec tunnel as a network tunnel identity from the Umbrella firewall and Web policies. For more information, see Manage Firewall Policy and Manage the Web Policy.
Check Device Compatibility < Add Network Tunnel Identity > Supported IPsec Parameters
Updated almost 2 years ago
