Enable SSO with PingID
To enable single sign-on (SSO) with SAML for Umbrella, you must first add the Ping Identity application for Umbrella to your organization, then follow the step-by-step wizard to complete the process in Umbrella.
Prerequisites
- Full admin access to the Umbrella dashboard. See Manage User Roles.
- Follow the procedure to download the PingID XML metadata file.
Procedure
Download the PingID XML metadata file:
a. To configure Ping Identity for Umbrella to gather the metadata, log in to your Ping Identity dashboard, and then go to the Admin tab. You must log in to Ping Identity dashboard with the same account that you are using in the Umbrella dashboard.
b. Click Add Application and then Search Application Catalog.
c. Search for "OpenDNS" and add the application named OpenDNS with SAML 2.0 next to it. Save the app and keep the defaults for General Settings.
d. Select the defaults for setup steps 1 through 4 (change opendns.com to umbrella.com. For example, https://login.umbrella.com/sso) verifying the attribute mapping and then click Save & Publish.
e. At Step 5 - Review, click Download next to SAML Metadata and save the pingone-metadata-idp.xml file.
e. Ensure all users that will need to log in to your Umbrella dashboard now or in the future have the OpenDNS application assigned to their Ping account. All users must have access to the OpenDNS application or they will not be able to log in. Save the configuration.
- Navigate to Admin > Authentication.

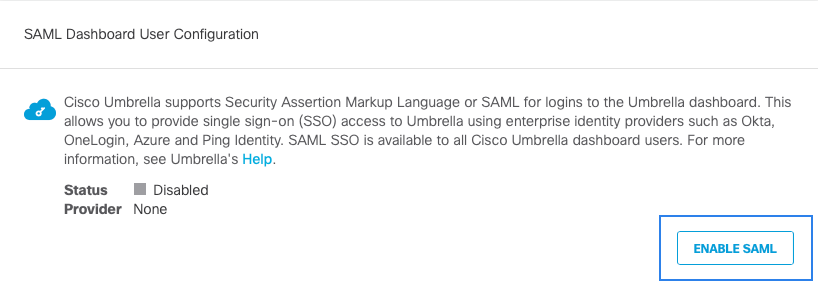
- In the SAML Dashboard User Configuration section, click Enable SAML.
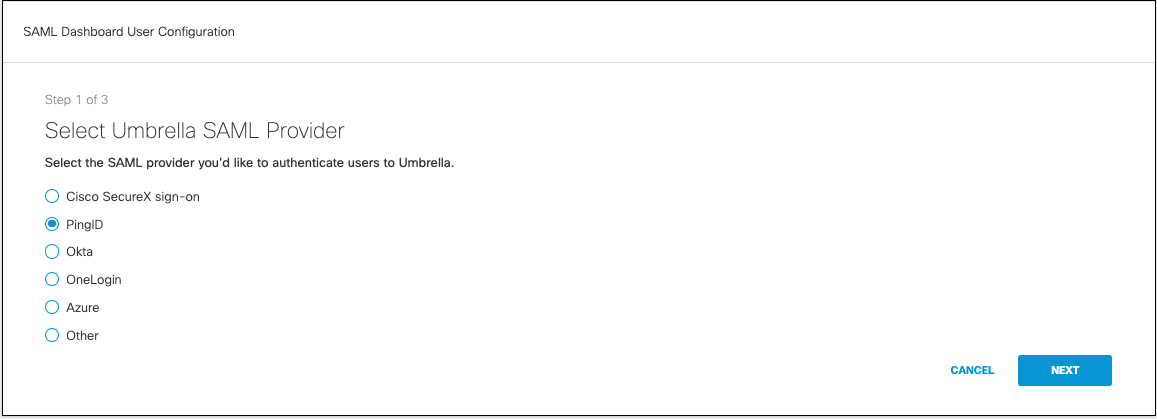
- Click the PingID radio button, and then click Next.
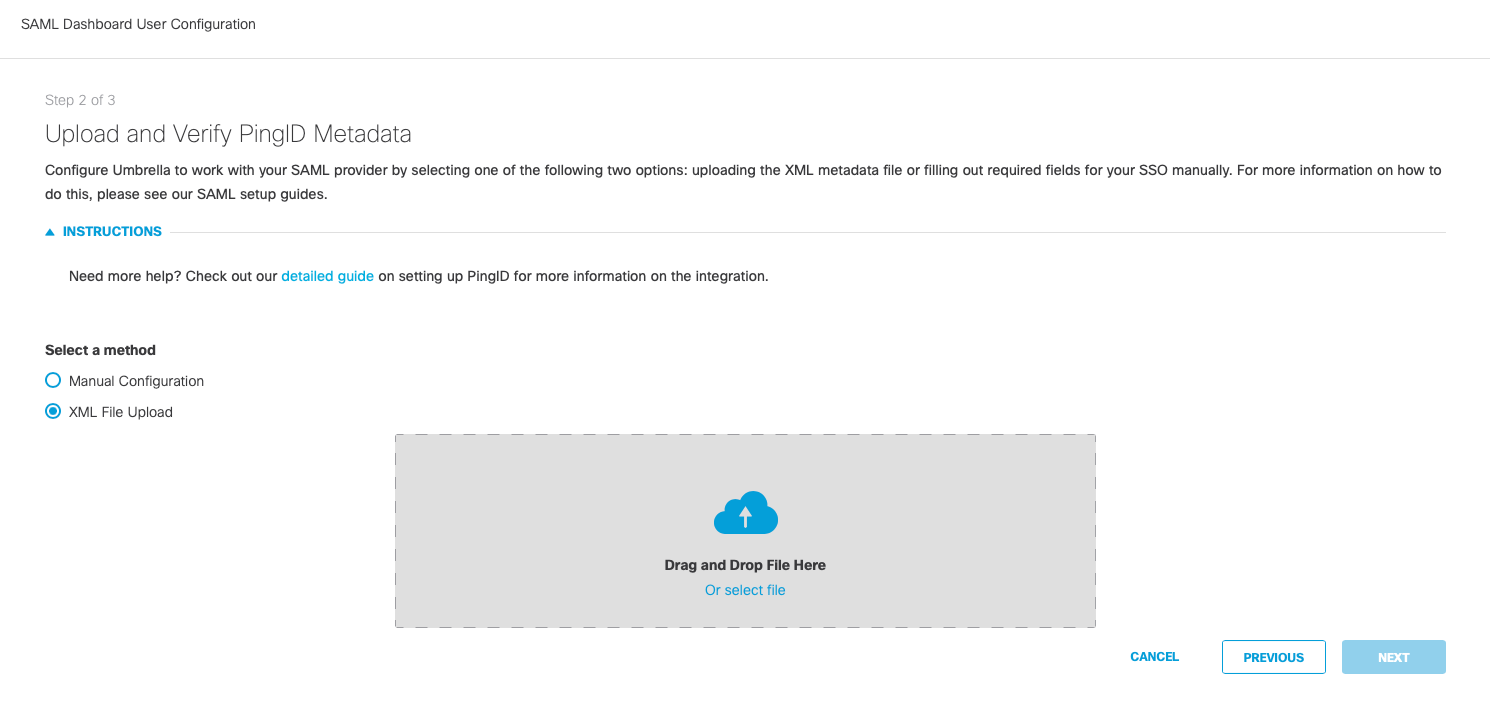
- Click the XML File Upload radio button. Upload the metadata file that you downloaded from Ping Identity, and then click Next.
- Click Test Configuration and enter the Umbrella email for your current logged in user that was added to the Ping Identity application. After the test completes, a success message should be displayed. All authentication to the Umbrella dashboard for all users in your organization is now handled by Ping Identity.
Enable SSO with Duo < Enable SSO with PingID > Enable SSO with Okta
Updated almost 2 years ago
