Add Customer CA Signed Root Certificate
You can use a certificate signed by your CA to enable secure connections between your identities and Umbrella. Umbrella requires that you configure identities to use a certificate in any circumstance where Umbrella must proxy and decrypt HTTPS traffic intended for a website. You must install a trusted root certificate in all browsers that an identity uses.
A root certificate is required for Block Pages and HTTPS Inspection.
- For Block Pages, if you visit a blocked domain through HTTPS, a certificate must be installed so that Umbrella presents a block page rather than a browser error.
- For HTTPS Inspection, if a domain is proxied, a certificate must be installed so that Umbrella can decrypt HTTPS traffic without the browser presenting an error.
Web Policies
For the Web policy, you can use either the Cisco Umbrella root certificate or your own CA-signed certificate. To use your own certificate, you must set up a certificate signed by your CA in Umbrella and select identities in a Web policy to use your root certificate. For more information about the Web policy, see Manage the Web Policy.
DNS Policies
For DNS policies, you can only use the Cisco Umbrella root certificate.
By default, all identities use the Cisco Umbrella root certificate unless you configure identities to use a certificate signed by your own CA.
Table of Contents
Prerequisites
- A Certificate Signing Request (CSR) file downloaded from Umbrella.
- Microsoft Certificate Services, Active Directory Certificate Services, or OpenSSL to sign the CSR with your CA.
Certificate Requirements
When you issue a certificate signed by your own CA, you must meet the following requirements:
- The encoding must use UTF8String.
- You must use the same character encoding for all certificates in your certificate chain.
- The “Subject Name” in the CSR file downloaded from Umbrella must be honored.
- The certificate must be valid for no more than three years.
- The certificate must be an X509v3 certificate with an RSA public key.
- Use one of the following signature algorithms:
- SHA256withRSA
- SHA384withRSA
- SHA512withRSA
- Include the following X509v3 extensions:
- X509v3 Basic Constraints marked as critical: CA:TRUE, pathLenConstraint: undefined
- X509v3 Key Usage, marked as critical: Certificate Sign, CRL Sign
Note: Umbrella supports a maximum of six certificates.
Install Root Certificate in Browsers
For information about how to install certificates in browsers, see Install the Cisco Umbrella Root Certificate.
Procedure
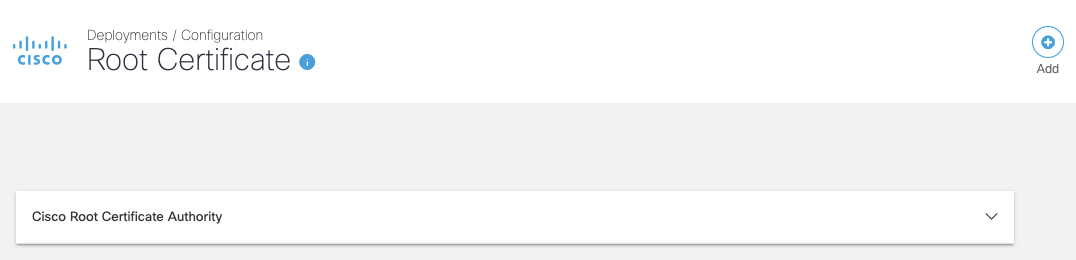
- In Umbrella, navigate to Deployments > Configuration > Root Certificate and click Add.
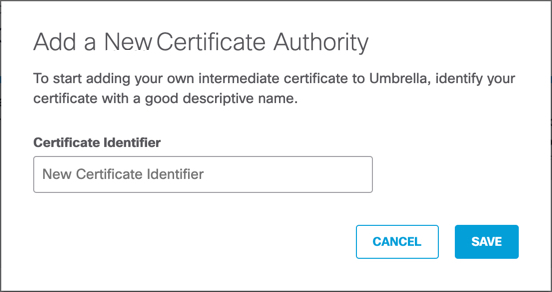
- Enter a descriptive name for your certificate in Certificate Identifier and then click Save.
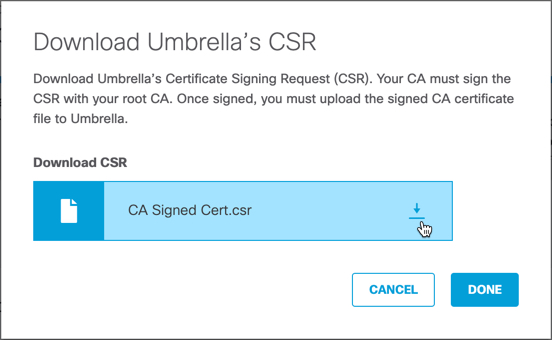
- Download Umbrella's Certificate Signing Request (.csr) file and then click Done.
Use a tool such as Microsoft Certificate Services or OpenSSL to sign the CSR with your CA.
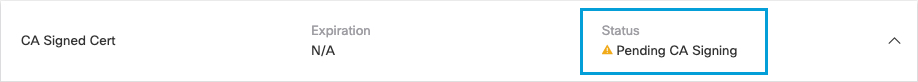
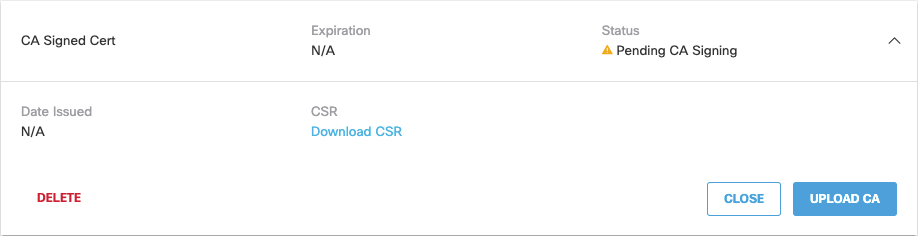
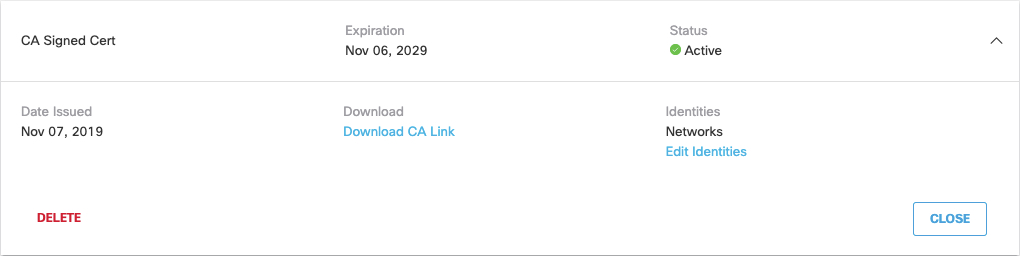
Certificate status is "Pending CA Signing" until you upload your own CA signed root certificate.
Note: If you do not download the CSR file, status is "Pending CSR Download".
- Sign the CSR file with your CA. For more information, see Custom Root Certificate—Active Directory Services.
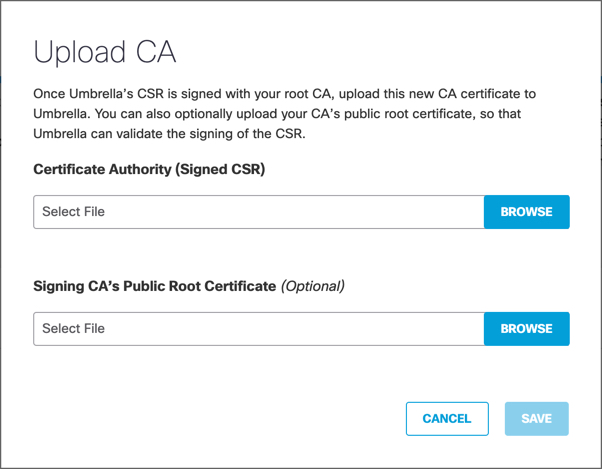
- Once you have signed the downloaded .csr file, click Upload CA.
Note: If you do not download the CSR file, the button is labeled "Download CSR".
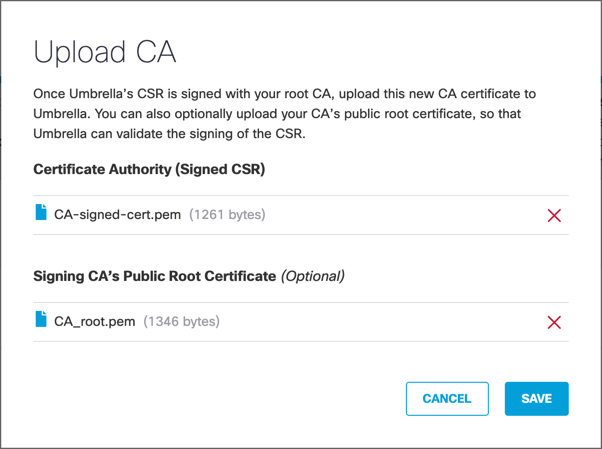
- Browse to the certificate you have generated with Umbrella's CSR, and then click Save.
You can optionally also upload your CA's public root certificate to Umbrella. This allows Umbrella to validate the certificate you are uploading to Umbrella.
- Click Save again. Umbrella adds the certificates.
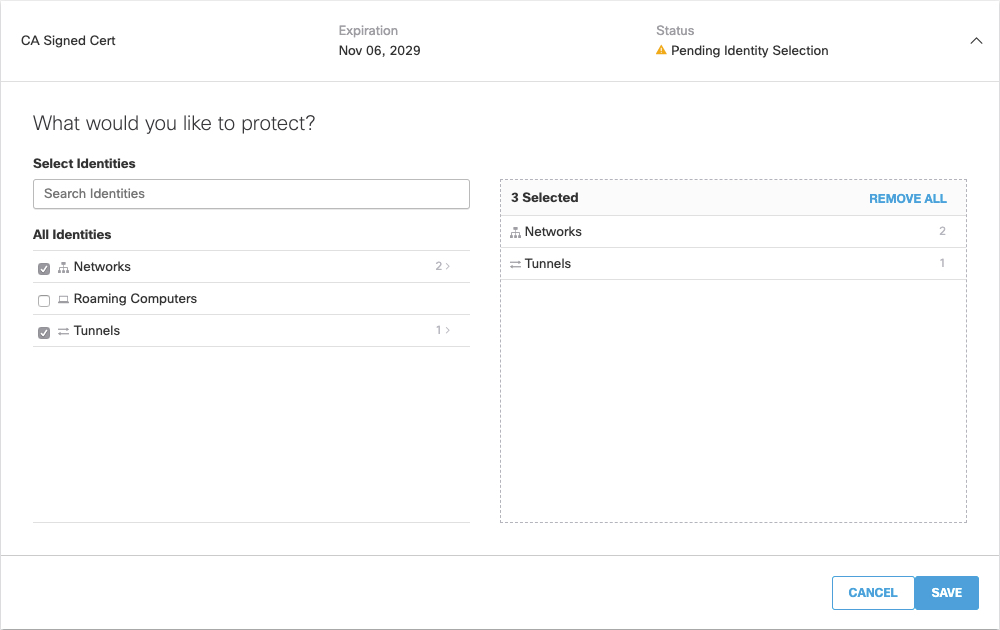
- Click Select Identities.
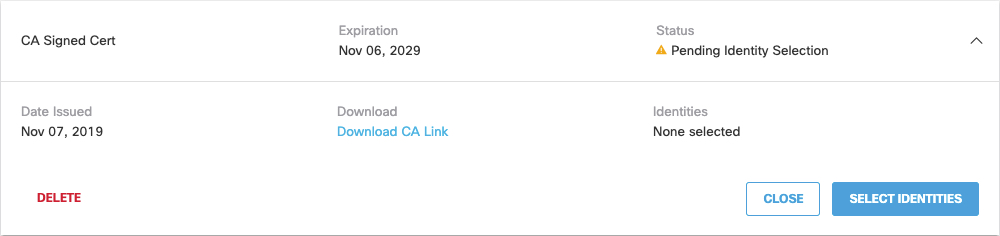
- Choose the identities to use the signed certificate, and click Save. Configuration changes may take several minutes to come into effect.
Expand the identities to select individual identities which can use this certificate.
Note: If an identity not available to select, the identity is already assigned to a certificate. You can only assign an identity to one certificate. You can not select Roaming identities individually. A single certificate applies to all Roaming clients.
- Install your own signed certificate into all browsers found in the selected identities. Umbrella now knows to trust this certificate. For more information about how to install certificates in browsers, see browser specific documentation.
Install the Cisco Umbrella Root Certificate < Add Customer CA Signed Root Certificate > Delete Customer CA Signed Root Certificate
Updated almost 2 years ago
