Communication Flow and Troubleshooting
The Umbrella integration spans several areas of your Cisco Active Directory (AD) Connector configuration. We recommend that you understand the flow of communication between each of the operational components. This can assist in troubleshooting and in ensuring that your environment is properly configured before you deploy.
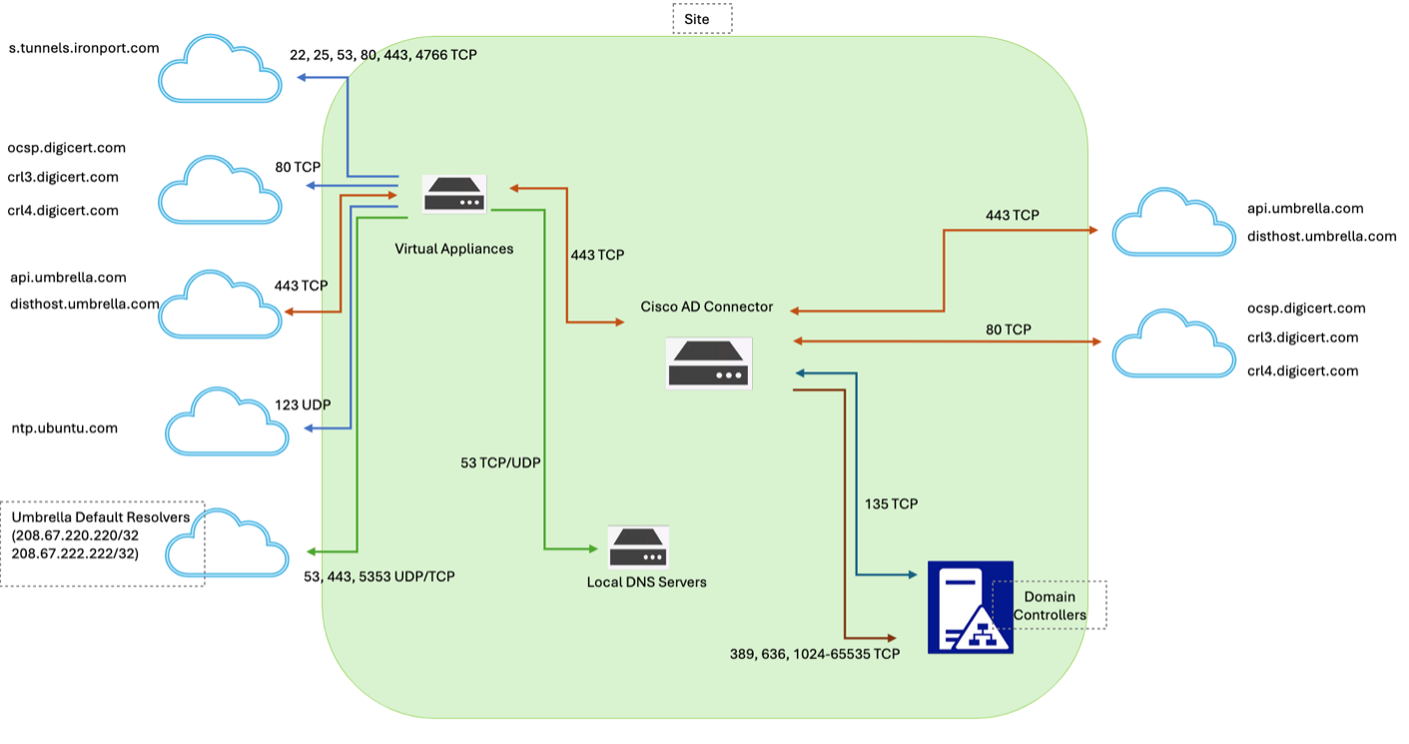
Table of Contents
Communication Flow
The connector first attempts to communicate to the domain controller over LDAPS. If unsuccessful, it falls back to communicating over LDAP using Kerberos or NTLM, in that order.
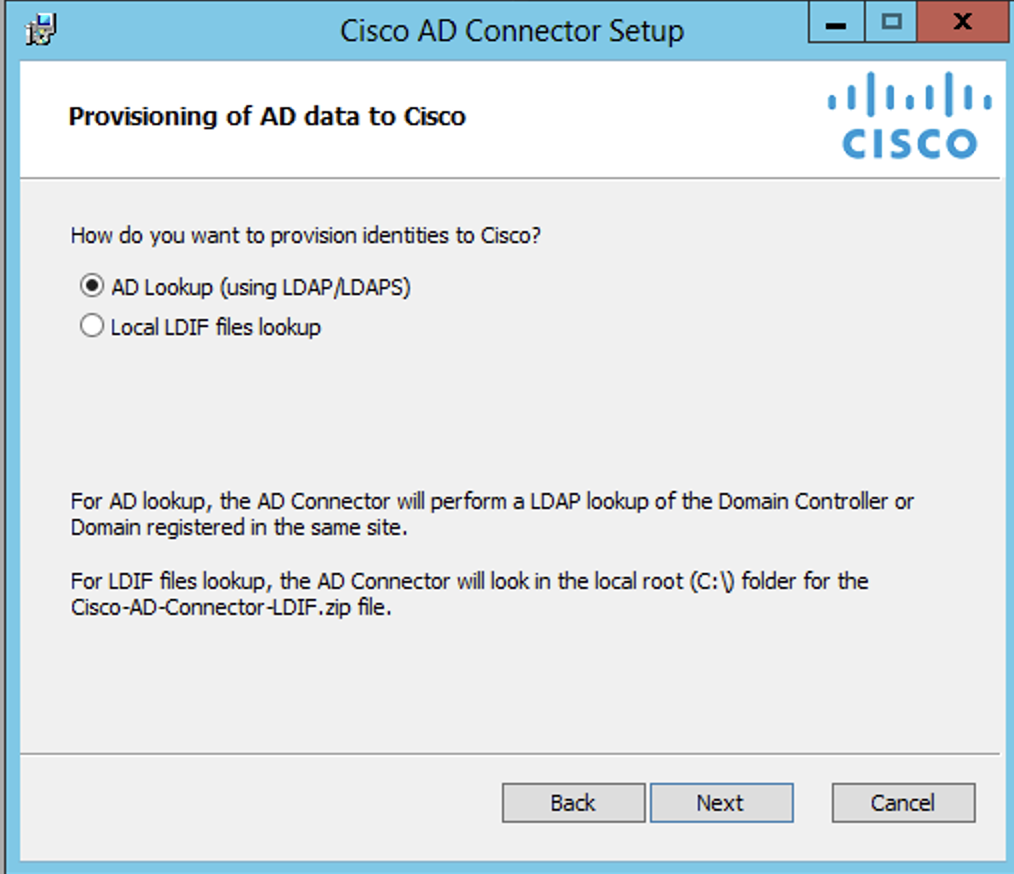
The connector retrieves the AD users, groups, and computer details only. The necessary attributes are stored from each object, including the sAMAccountName, dn, userPrincipalName, memberOf, objectGUID, primaryGroupId (for users, groups and computers), and primaryGroupToken (for groups). Passwords or password hashes are not retrieved. This data is then uploaded to Umbrella for use in policy configuration and reporting. This data is also required for per-user or per-computer filtering. Note that the objectGUID is sent in hashed form.
The connector sends the AD data every five minutes, using an HTTPS connection on port 443 TCP. It can take an hour or longer for changes to reflect in Umbrella.
The connector stores this data locally as well in .ldif files contained within C:\Program Files\Cisco\CiscoADConnector\ADSync. To find out exactly what is being synchronized to Umbrella, you can look at these files. At install time, you have the option to turn off the local storage of .ldif files.
The connector constantly sends AD events to the virtual appliances (VAs) using TCP port 443. This is a one-way communication. The appliances do not communicate with the AD Connectors. By default, the connector sends information, including IP to username mappings, to the VA in unencrypted form. For AD integration with the Umbrella VA, the AD Connector and VA should communicate over a trusted network. If encryption of communication between the Connector and VA is required for compliance or other reasons, see Umbrella Virtual Appliance: Receiving user-IP mappings over a secure channel.
The connector communicates with the domain controllers/event log collector using RPC. In general, port 135 TCP is the standard port for RPC communication with domain controllers. The RPC communication also uses a randomly assigned ephemeral port between 49152 TCP and 65535 TCP.
Troubleshooting
The following firewall/ACL requirements ensure that AD Connectors can communicate with the Umbrella cloud services and on-premise components:
Port and Protocol | Source | Destination | Note |
|---|---|---|---|
443/TCP | AD Connector | api.umbrella.com.com (for syncing) |
|
| 80/TCP | AD Connector | ocsp.digicert.com crl3.digicert.com crl4.digicert.com | Check for certificate revocations through the Online Certificate Status Protocol (OCSP) and certificate revocation lists (CRLs). |
| 389/TCP 636/TCP | AD Connector | Domain controller/ domain | LDAP syncing |
| 443/TCP | AD Connector | Virtual Appliances | Send information relating to login events and IP addressing. It's very important to note that this traffic occurs over 443/TCP but is not an SSL connection by default. Many IDS and IPS systems will flag this traffic as suspicious. If you're running an IDS or IPS that is listening on the local network, check the enforcement logs to ensure this traffic is not getting flagged. |
| 135/TCP 49152-65535/TCP | AD Connector | Domain Controllers/ Event Log Collector | RPC communication to fetch login events |
| 135/TCP | Domain controllers/ Event Log Collector | AD Connector | RPC response |
Note: The Digicert domains resolve to various IP addresses based on a CDN and are subject to change.
If you encounter any issues in communicating to Umbrella, we recommend that you check for any Layer-7 application proxies which might be blocking or dropping data. A common case is the inspect feature on Cisco devices that act on protocols such as DNS, HTTP, and HTTPS:
http://www.cisco.com/c/en/us/td/docs/security/asa/asa72/configuration/guide/conf_gd/inspect.html
You can restart the connector by restarting the Cisco Active Directory Service service on the connector system. Restarting the connector triggers a full synchronization of AD objects (and not just the changes from the previous sync) to Umbrella.
If your connector is not in the Okay state and you need to raise a support ticket with Umbrella, see Providing Support with AD Connector Logs.
Change the Connector Account Password < Communication Flow and Troubleshooting
Updated 2 months ago
