File Retrospective Events and Cisco Secure Malware Analytics (Threat Grid)
For both DNS and Web policies, when File Inspection is enabled, Cisco Umbrella leverages the power of Cisco's Advanced Malware Protection (AMP) to scan files for malicious content hosted on risky domains before those files are downloaded. This helps prevent infections.
For Web policies, additional intelligence can be provided by enabling Cisco Secure Malware Analytics (Threat Grid). Files not blocked through File Inspection and that are unknown to AMP file reputation or blocked by Umbrella's anti-virus (AV) may be submitted by Umbrella to Cisco Secure Malware Analytics (Threat Grid) for malware analysis. The result in Umbrella is that you are able to review retrospective events—files that were previously considered benign, but have recently been marked as malicious. These events are identified under the File Retrospective section of Umbrella's Overview report.
For more information about File Inspection and Secure Malware Analytics (Threat Grid) Malware Analysis, see Manage File Analysis.
Table of Contents
File Retrospective Details
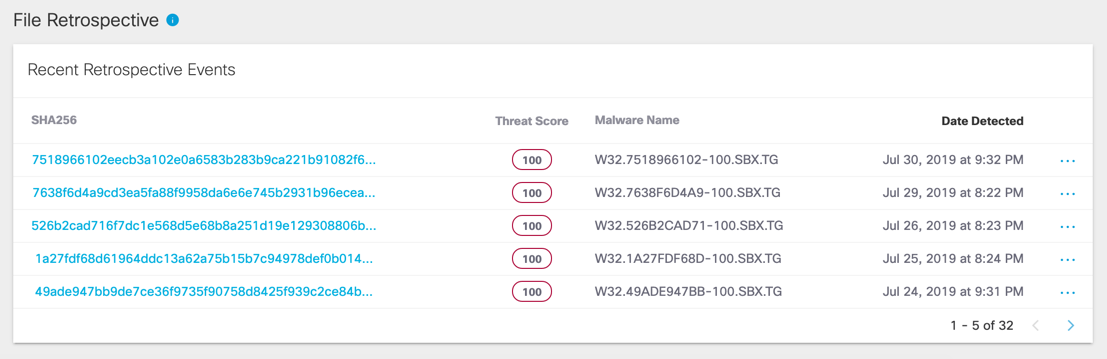
The Overview report's File Retrospective section lists the SHA256 name, the threat score, the malware name, and the date the file was detected. The threat score is a percentage from 0-100 ranking the likelihood that the file is malicious. The score is generated from the data provided in the Secure Malware Analytics (Threat Grid) Report.
Activity Search
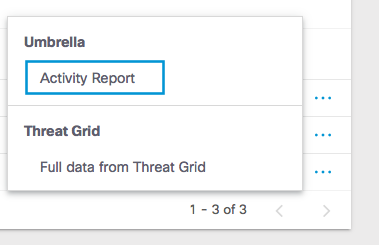
You can review details about a listed file through Umbrella's Actively Search report.
Details provided include what identity performed the download, the destination where it was downloaded from, and the action taken. When the action displays Allowed, the file has been successfully downloaded by the user and was not blocked by an AV engine or AMP Cloud. At this point, the file has been deemed malicious retrospectively through Threat Grid sandboxing and can be remediated by an admin.
- Click the file's SHA256 name or click the three dots to the right of the detection date which will open a drop-down menu with access to Umbrella's Activity Search report.
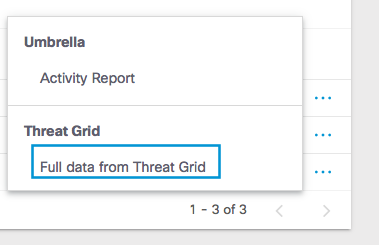
Full Data from Secure Malware Analytics (Threat Grid)
You can also view more details about the file's potential threats.
- Select Full data from Threat Grid when clicking the three dots next to the file's detection date.
Overview Report < File Retrospective Events and Cisco Secure Malware Analytics (Threat Grid) > Security Activity Report
Updated 5 months ago
