Test File Inspection
After setting up Umbrella, we recommend that you check your configured Umbrella Web policy. You can evaluate a Web policy with File Inspection enabled by pointing your browser to one of our test files.
Note: To only evaluate a Web policy, you must disable all Umbrella DNS security categories for your identities.
Prerequisites
- A device enrolled in an Umbrella policy with File Inspection enabled.
Procedure
- Browse to one of the Umbrella EICAR test files.
| Test File | Description |
|---|---|
| http://proxy.opendnstest.com/download/eicar.com | Cisco Umbrella clear text test file. |
| https://ssl-proxy.opendnstest.com/download/eicar.com | Cisco Umbrella encrypted test file. |
| http://proxy.opendnstest.com/download/AMP_TEST_FILE.txt | Cisco AMP clear text test file. |
| https://ssl-proxy.opendnstest.com/download/AMP_TEST_FILE.txt | Cisco AMP encrypted test file. |
- After loading a File Inspection test file, you should see a block page. Diagnostic information includes details about which server the file went through. If you do not see a block page, see Troubleshoot File Inspection.
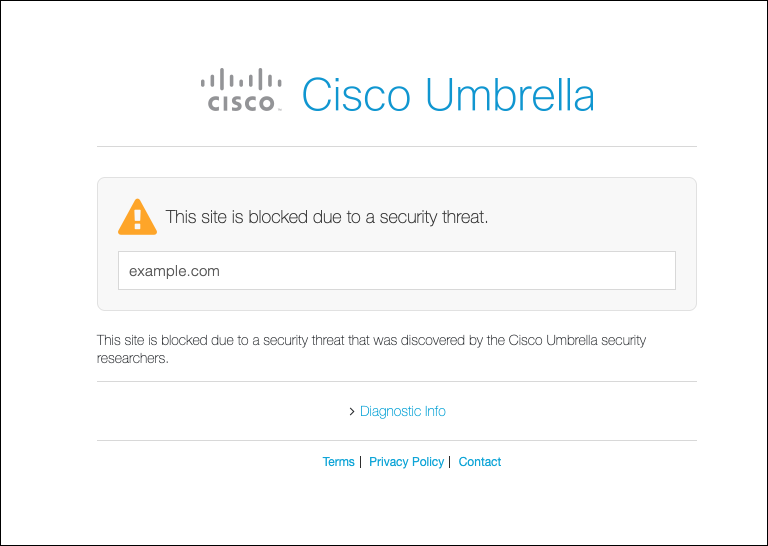
Block Page Diagnostic Information
The Umbrella block page diagnostic information identifies the hostname of the reputation authority. When proxying a domain or URL, Umbrella evaluates the destination in two phases.
- Umbrella receives a request and checks the reputation of the domain or URL. If the destination is known to be malicious, Umbrella blocks the request and displays a block page. The block page diagnostic information lists the
Serverasnginx. - Next, Umbrella checks if a destination matches a security category or is blocked by a rule in the Web policy. If a destination is not blocked, then Umbrella retrieves any requested content from the URL. Umbrella scans the requested files by file inspection (antivirus and AMP). If a file is malware, Umbrella returns a block page. The block page diagnostic information lists the
Serverasmps.
Enable Threat Grid Malware Analysis < Test File Inspection > Troubleshoot File Inspection
Updated about 1 year ago
