Control Cloud Access to Microsoft 365
This procedure describes how to add a new Tenant Controls setting to Umbrella and allow access to the cloud-based application Microsoft 365. Once added, this setting can be selected when adding a ruleset to the Web policy. Settings created here can be reused in multiple rulesets. For more information rulesets, see Add a Ruleset to the Web Policy.
Note: Tenant Controls is only available for the Web policy.
Prerequisites
- HTTPS Inspection must be enabled. For more information, see HTTPS Inspection.
- Full admin access to the Umbrella dashboard. See Manage User Roles.
- The following Microsoft specific data is required to configure Tenant Controls settings and allow access to the cloud-based application Microsoft 365:
- Tenant Domain
- Tenant Directory ID
For more information about this data and how to acquire it, see Azure Active Directory documentation.
The Microsoft 365 Compatibility feature exempts Microsoft 365 traffic from inspection and policy enforcement, allowing it to pass through the Umbrella infrastructure unaltered. However, when Tenant Controls are configured for Microsoft 365, we do decrypt four Microsoft login domains (login.microsoftonline.com, login.live.com, login.microsoft.com, and login.windows.net) for the purpose of tenant enforcement. For more information, see the official Microsoft documentation and Microsoft 365 Compatibility.
Procedure
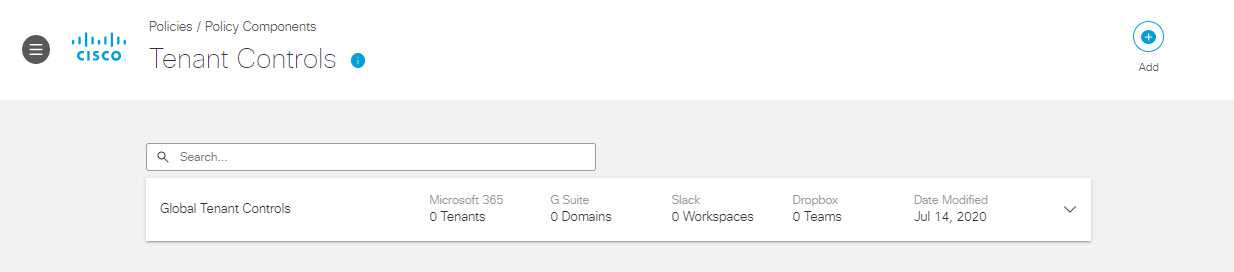
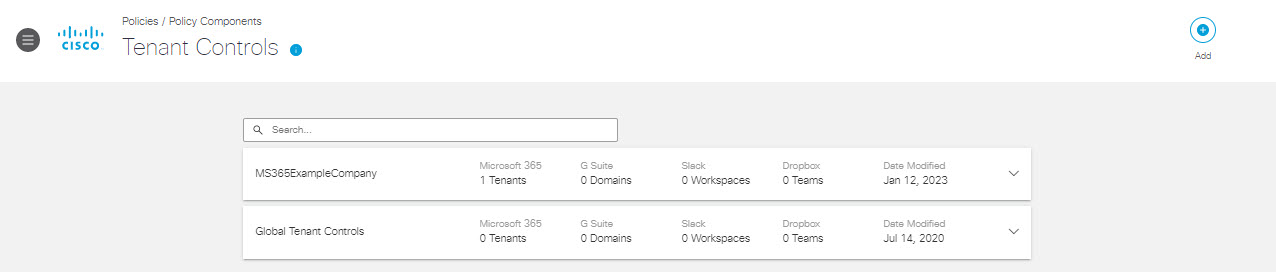
- Navigate to Policies > Policy Components > Tenant Controls and click Add or expand the default Global Tenant Controls setting.
Note: Tenant Controls is enabled by default for a ruleset. The ruleset uses the default Tenant Control setting if no other Tenant Control setting is configured for that ruleset.
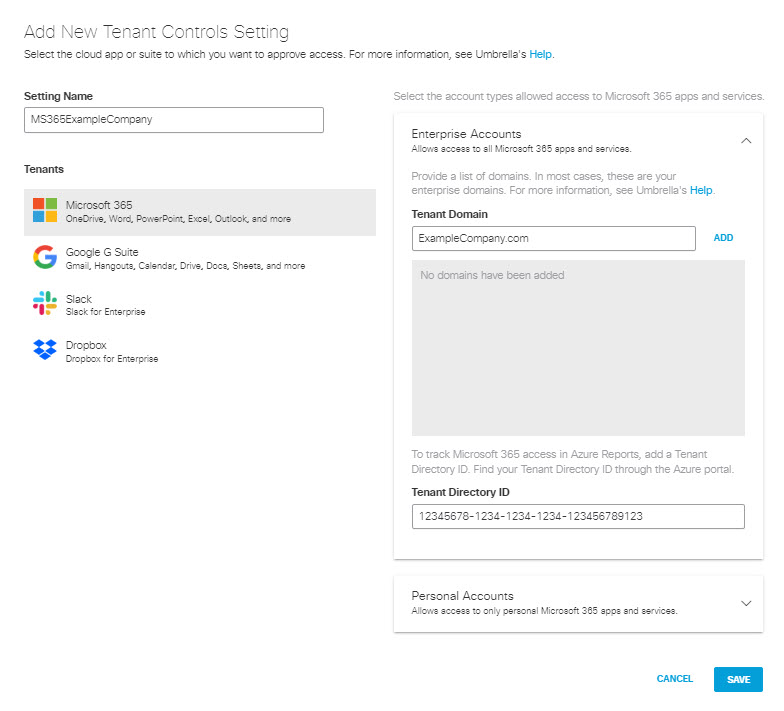
- Give your configuration a good descriptive Setting Name and select Microsoft 365.
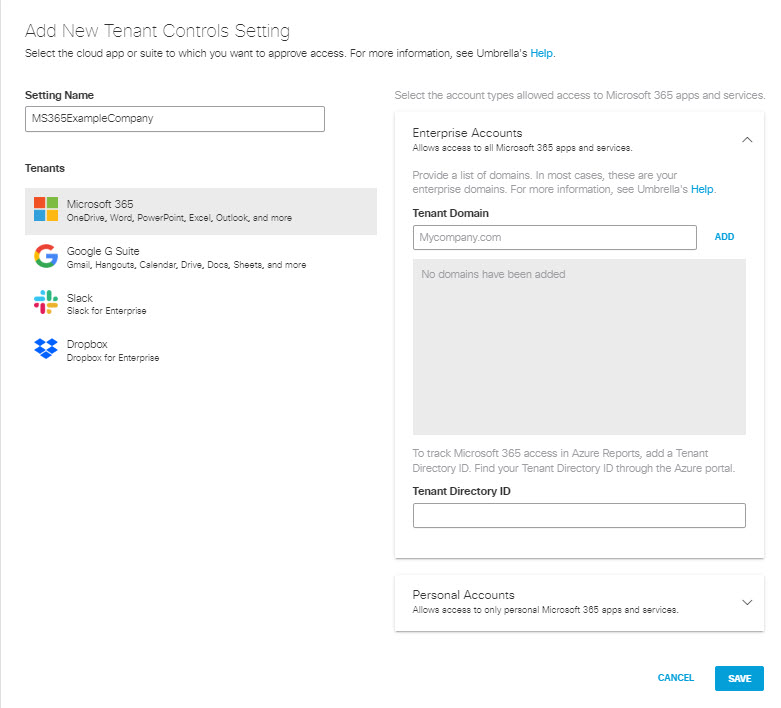
- To grant access to Microsoft 365 from within your organization:
a. Add your organization's Microsoft 365 Tenant Domain and click Add.
Note: You can add multiple Tenant Domains.
b. Optionally, add your organization's Tenant Directory ID for Microsoft 365.
This ID is used to track Office 365 access in Azure Reports.
Note: For more information about how to acquire the Tenant Directory ID, see Microsoft's documentation or contact Microsoft Support.
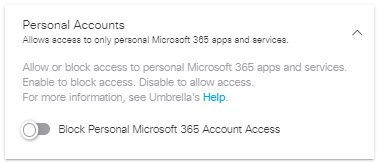
- Optionally, expand Personal Accounts and enable Block Personal Microsoft 365 Account Access.
- Click Save.
This new Tenant Controls setting is now available for selection when you add a ruleset to the Web policy.
Manage Tenant Controls < Control Cloud Access to Microsoft 365 > Control Cloud Access to Google G Suite
Updated about 2 months ago
