Test the Web Policy
The Web Policy Tester lets you test the Web policy's rules and rulesets by testing an identity's access to a destination and displaying the result—allow, block, warn, or isolate.
The Web Policy Tester is "powered" by the same engine that drives the Web policy, thus the Web Policy Tester evaluates rulesets and rules in the same way that the Web policy does. This means that the Web Policy Tester evaluates the Web Policy starting at the ruleset with the highest priority and attempts to match the Primary and optional Secondary identities to the ruleset’s identities. If no match is found, the Web Policy Tester moves down to the ruleset with the next highest priority, and so on. If no ruleset above the default ruleset matches, the default ruleset is selected. Note that once a ruleset is matched, the Web Policy Tester then performs a similar process against the rules within the matched ruleset and begins at the rule with the highest priority—once a rule match is detected the tester stops evaluating against any other rules. The tester finds the first settings match against the added primary and secondary identities and stops evaluating further.
Before You Start
Before running a test, determine what your expected results are so that you can compare expectations against actual results. For example, was the identity blocked from reaching the specified website as expected, or was the website unexpectedly reached?
Although not required, it is recommended that you add both a "primary" and "secondary" identity when configuring your test. Because the identity configured in a ruleset is not always the same identity configured in a rule within that ruleset, adding a secondary identity helps improve the efficacy of ruleset and rule matching.
Procedure
When first testing newly added rulesets, rules, or identities, note that it may take several minutes for your new settings and identities to fully integrate with Umbrella. This means that when first added, they may not be available for testing. Wait a few minutes and try again.
- Navigate to Policies > Management > Web Policy and click Policy Tester.

- Add a Primary Identity, optionally a Secondary Identity, and a Destination:
- Primary Identity — The identity from which the request originates. Can be one of Networks, Network Tunnels, or Roaming Computers identities.
- Secondary Identity — The identity that identifies the user or system from which the request originates. Can be one of AD User or Internal Network identities. Adding a second identity helps improve the efficacy of ruleset and rule matching. Only available if your organization includes AD User or Internal Network identities. While optional, we recommend including this secondary identity to better determine which ruleset and rule are triggered.
- Destination — The destination that added identities will attempt to access. Can be one of domain, URL, or public IP address. You cannot use a destination list or any rule setting, such as a content category or application.
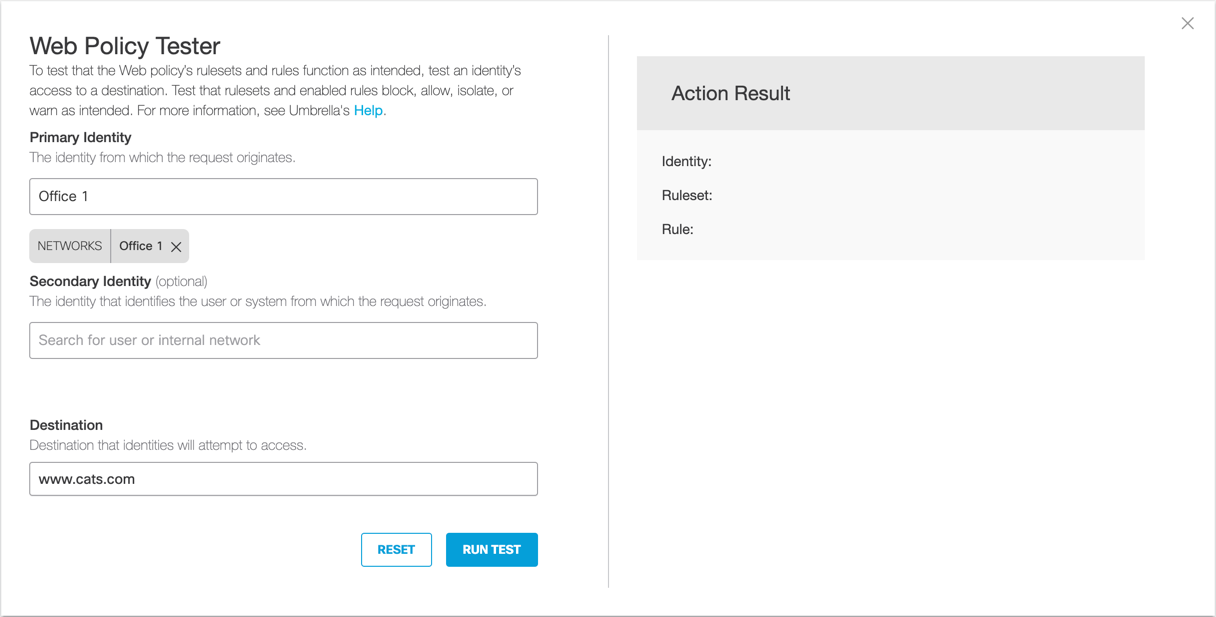
- Click Run Test.
Note: The Run Test button is unavailable until you add both an identity and a destination.
Results
When you click Run Test, the Web Policy Tester tests the configured identities' access to the added destination and then displays the results of that test.
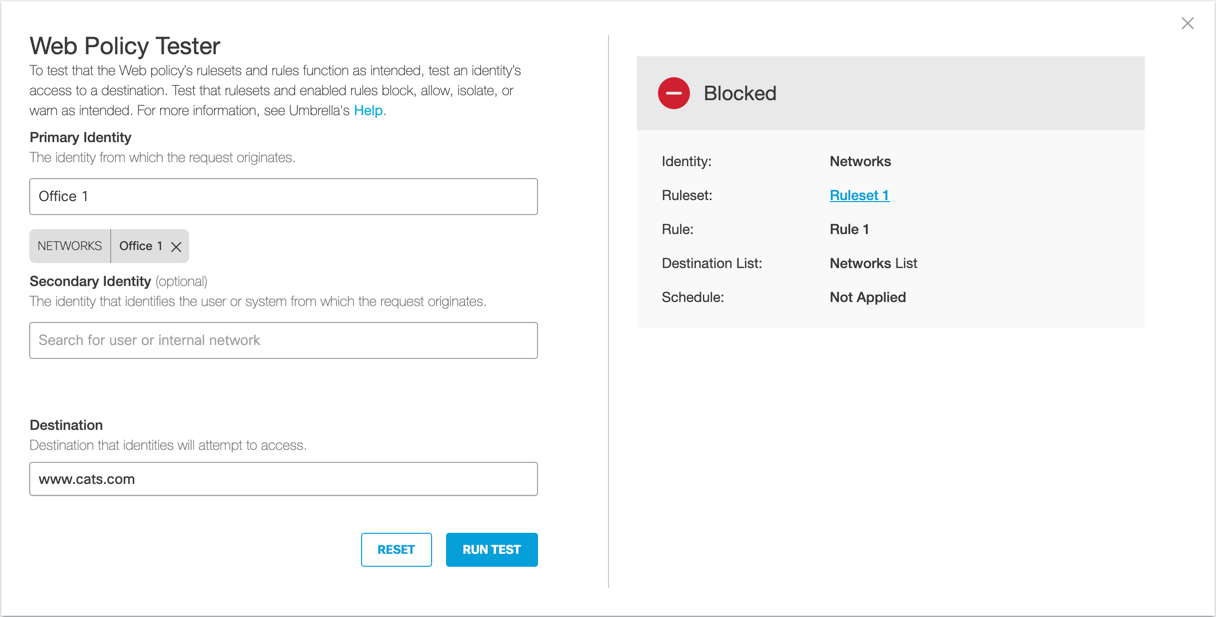
Test results include:
- Result — The action taken by the Web policy based on the "triggering" ruleset or rule: blocked, allowed, warn, or isolate.
- Identity — The identity (rule or ruleset) that triggered the result. This is important if there is more than one identity specified.
- Ruleset — The ruleset against which the identity was evaluated. This is the ruleset that includes the rule against which the identity was evaluated.
- Rule — The rule against which the identity was evaluated. When no rule matches, the tester applies the default allow and only returns the ruleset name as the match.
- Destination List, Security Settings, and Content Category Settings — For blocked, isolate, or warn results only. The name of the setting or list that caused the block, warn, or isolate.
- Schedule — The time frame within which the rule is applied to the identity triggered.
Add Rules to a Ruleset < Test the Web Policy > Web Policy Precedence
Updated almost 2 years ago
