(combined with cEdge)Configure Tunnels Manually with Viptela vEdge
Follow these steps to add a tunnel to connect a Cisco vEdge device to Cisco Umbrella’s cloud-delivered firewall and secure web gateway security services.
For more information about Cisco vEdge devices and related topics, see Cisco's SD-WAN product documentation.
Table of Contents
Prerequisites
- You must enable NAT in the vEdge feature template that faces the internet.
- A working configuration must have public DNS configured in the transport vpn to be able to resolve DNS queries used in the tunnel formation. For example,
management.api.umbrella.com. - You can access the vManage console with a web browser. By default, the HTTPS port is 8443, but this may vary based on how your vManage is configured.
Note: If you get a "Not Secure" warning when accessing the link, you can ignore it. When the vManage login screen appears, enter your credentials.
Configure vManage Templates
In vManage, all the features are configured through templates. Once the vEdge devices are registered with vManage, you cannot configure anything through the CLI.
There are two types of Templates: Device and Feature Templates. First define the device template, then the feature template.
Define the Feature Template
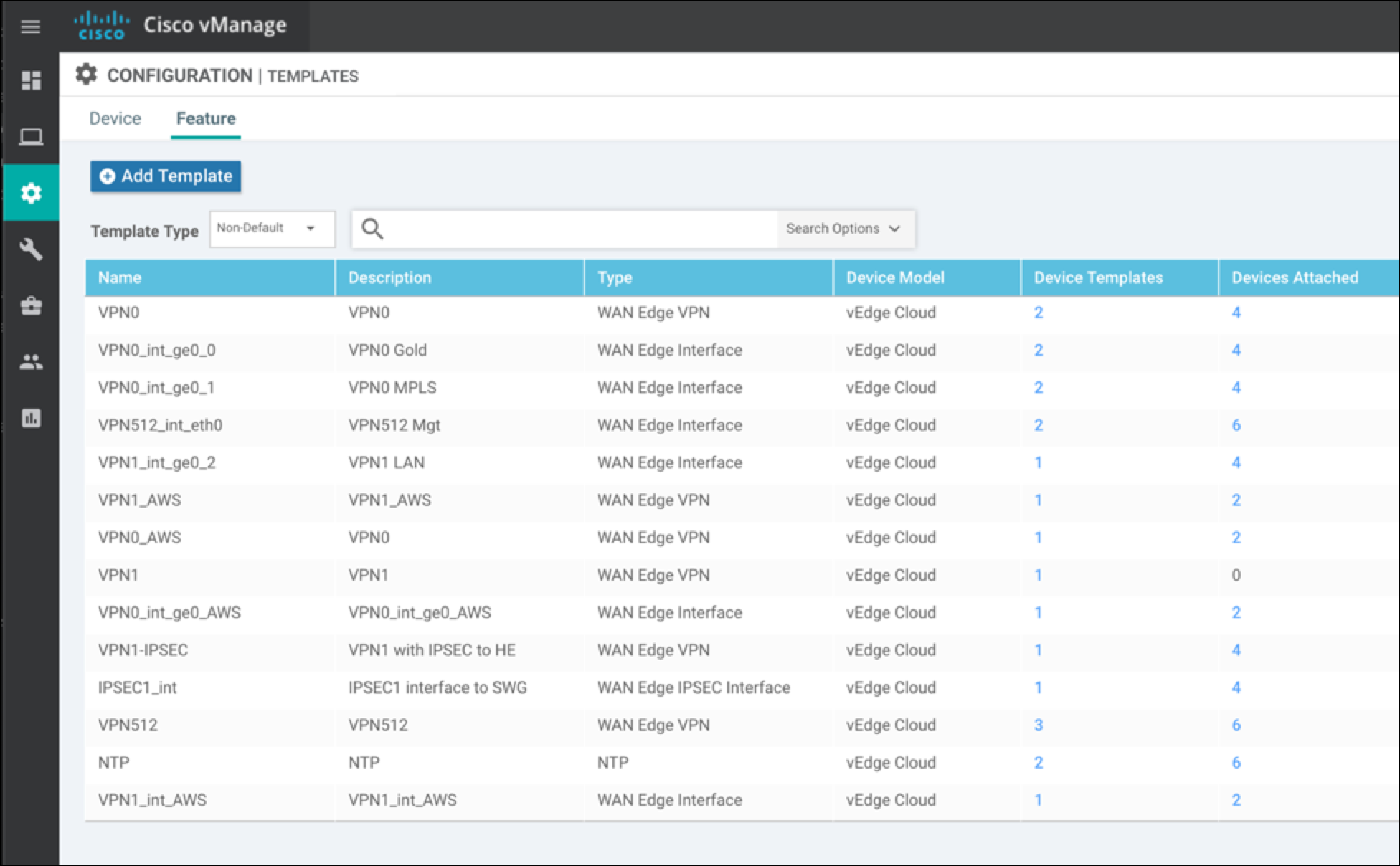
- Log into the vManage console and navigate to Configuration > Templates.
- Confirm that the Feature Templates tab is selected, then click Add Template.
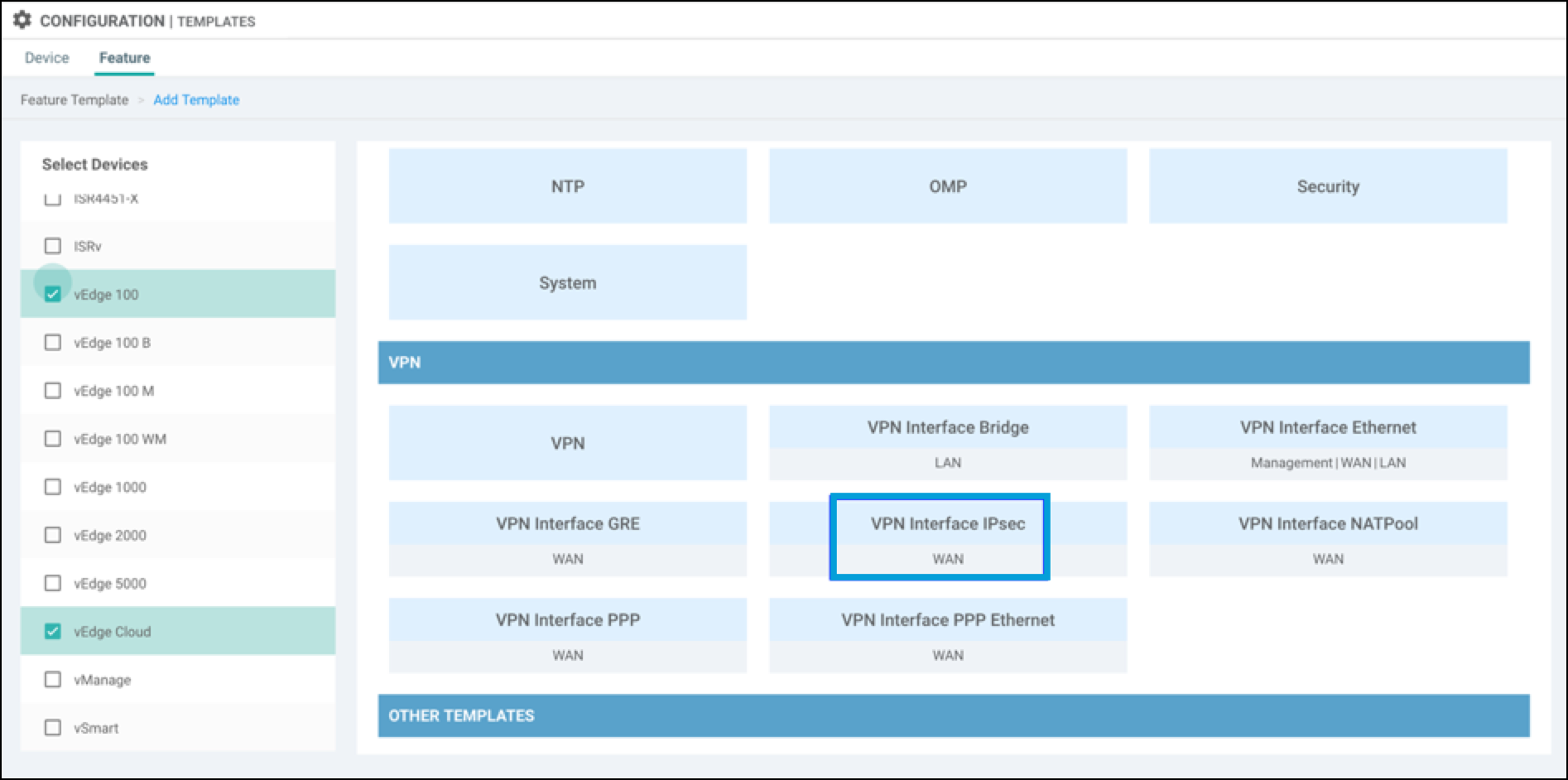
- Under Select Services select device types, then choose VPN Interface IPSec WAN.
- Configure Tunnel Parameters:
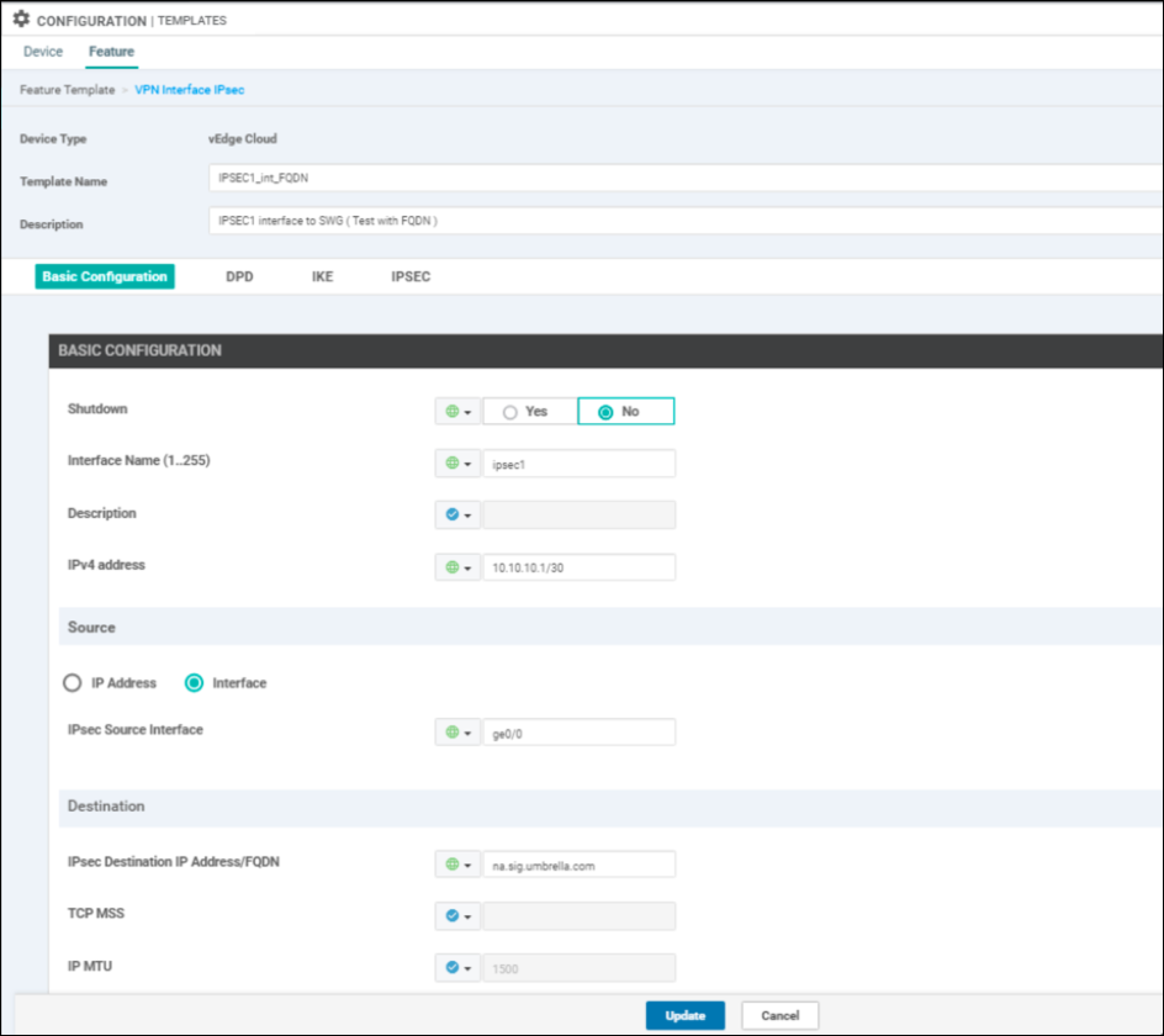
a. Choose a template name and description for the Tunnel interface.
b. Under Basic Configuration, set Shutdown to the global option and choose NO.
c. Choose the Interface Name from 1 to 255. For example,ipsec1.
d. Configure the IPv4 address by selecting the Global attribute and set the IP.
e. Set the IPSec Source Interface toge0/0. This must be the WAN interface in VPN 0, which has the internet connectivity.
f. Set the IPSec Destination to the closest Cisco Umbrella data center.
g. Dead Peer Detection Value: Leave this at the default setting unless you have a specific requirement otherwise.
- Choose the Global Attribute to change any IKE and IPSec defaults:
IKE Settings
- Set the IKE Version to 2.
- Set the IKE Rekey Interval to 28800.
- Leave the default Cipher Suite, which is AES-256-CBC-SHA1.
- Set the IKE DH Group to 14 2048-bit Modulus.
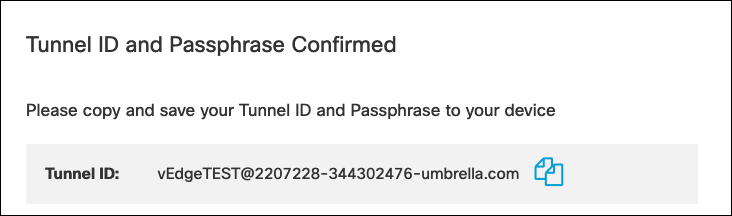
- The Pre-shared key (PSK) is configured on the Umbrella dashboard.
- The Remote endpoint is Umbrella IP CDFW Headend.
- For the Local endpoint enter the named tunnel you generated in the Umbrella dashboard:
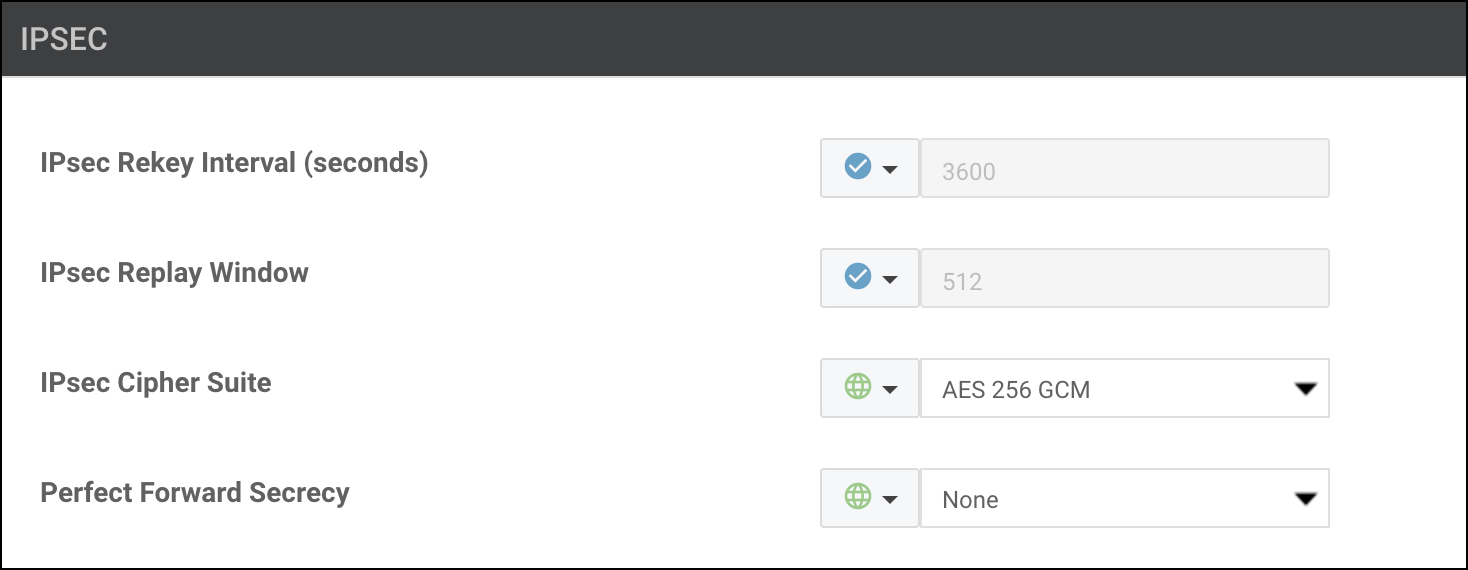
IPSec Settings
- Leave the IPSec Rekey Interval & Replay Window values at their defaults.
- Use the default Cipher Suite
AES 256 GCM. - Set the Perfect Forward Secrecy value to "NONE".
Cipher Suite Encryption
If performance is an issue with the default cipher, both
AES 256 CBC SHA1andNull SHA1are also supported. You can test these to determine whether one offers better performance for a particular platform. Note thatNull SHA1isn't necessarily faster than the defaultAES 256 GCMbecause of the cost of the SHA1 hashing. In addition,Null SHA1is not recommended due to security concerns of unencrypted transport.
- Click Update to save the configuration template.
Add the IPSec Interface Template
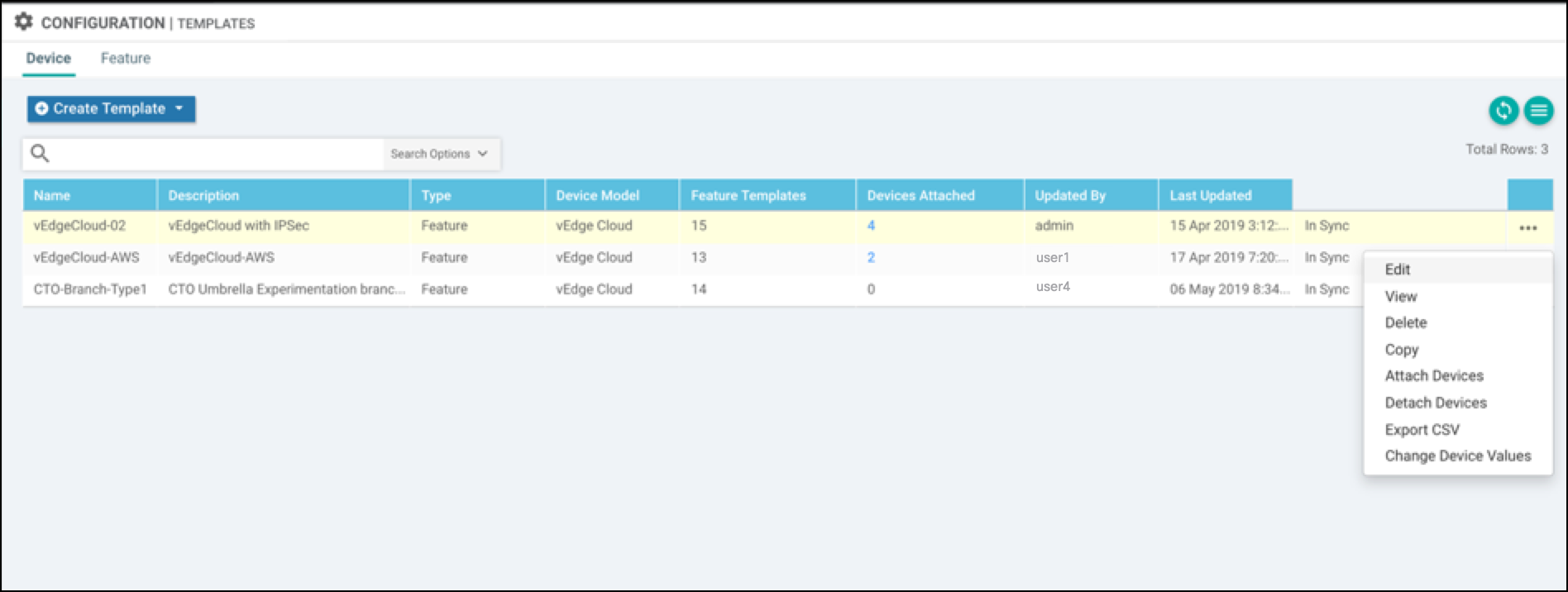
- Select Configuration > Templates > Device and then choose the device template for the CDFW tunnel.
- Select Edit from the pull-down list.
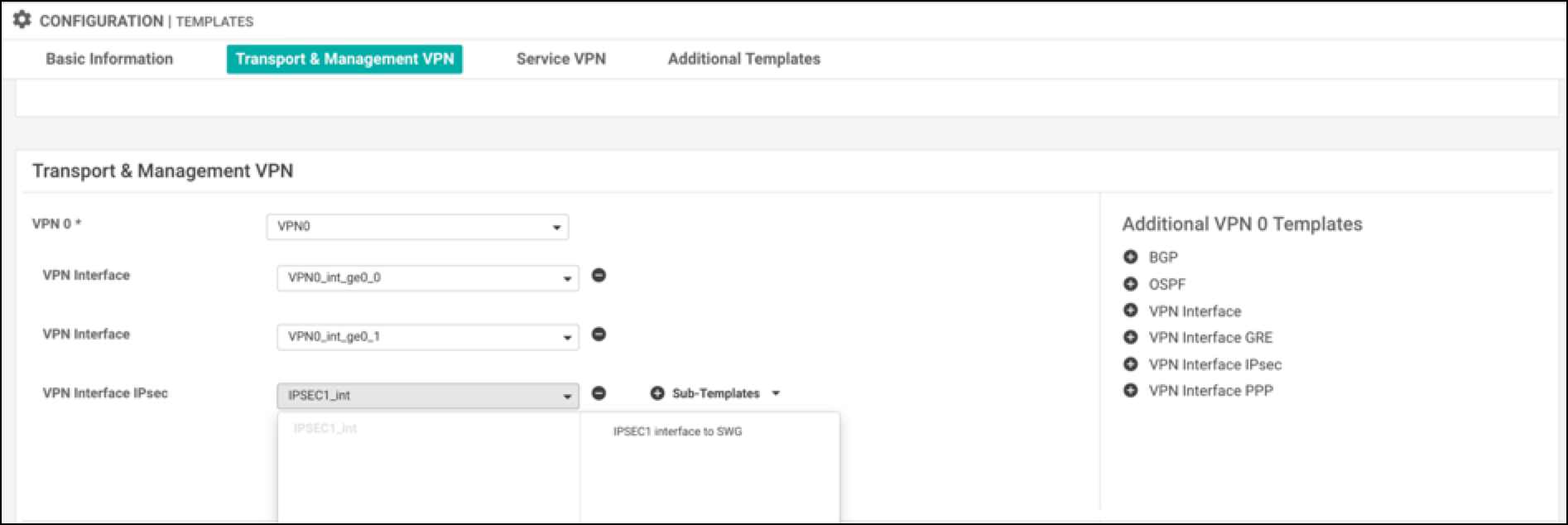
- Add the VPN IPSec tunnel interface in the VPN 0 Transport & Management VPN section.
Choose the VPN Interface IPSec that you added as part of the feature template.
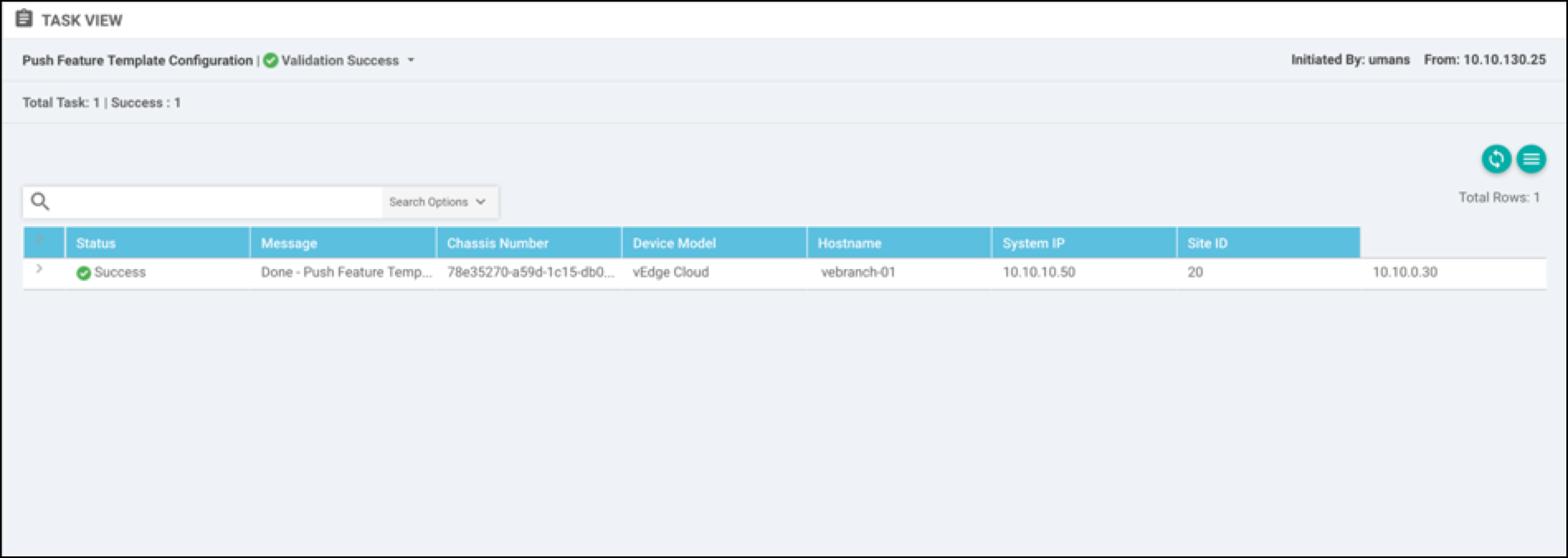
- Click Update. A success message appears.
##Configure Static Routes
After configuring a template, you need to add static routes from the service VPN to redirect the traffic through the IPSec tunnel to CDFW headend.
- Select Configuration > Templates > Feature.
- Click the action menu, then edit the template to add IPSec route 0.0.0.0/0 via IPSec1 Tunnel interface.
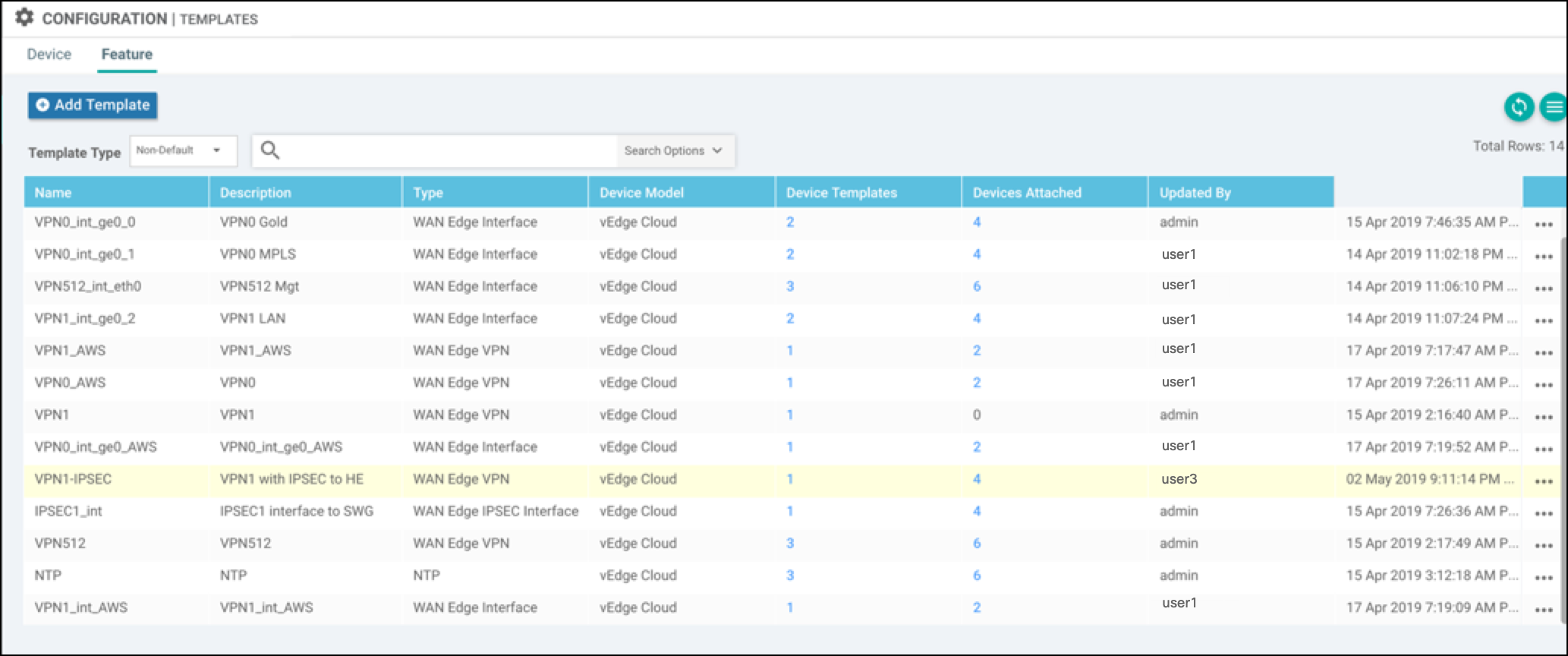
- Add one more IPSec Tunnel interface (for example, IPSec2), and set that as the secondary tunnel interface.
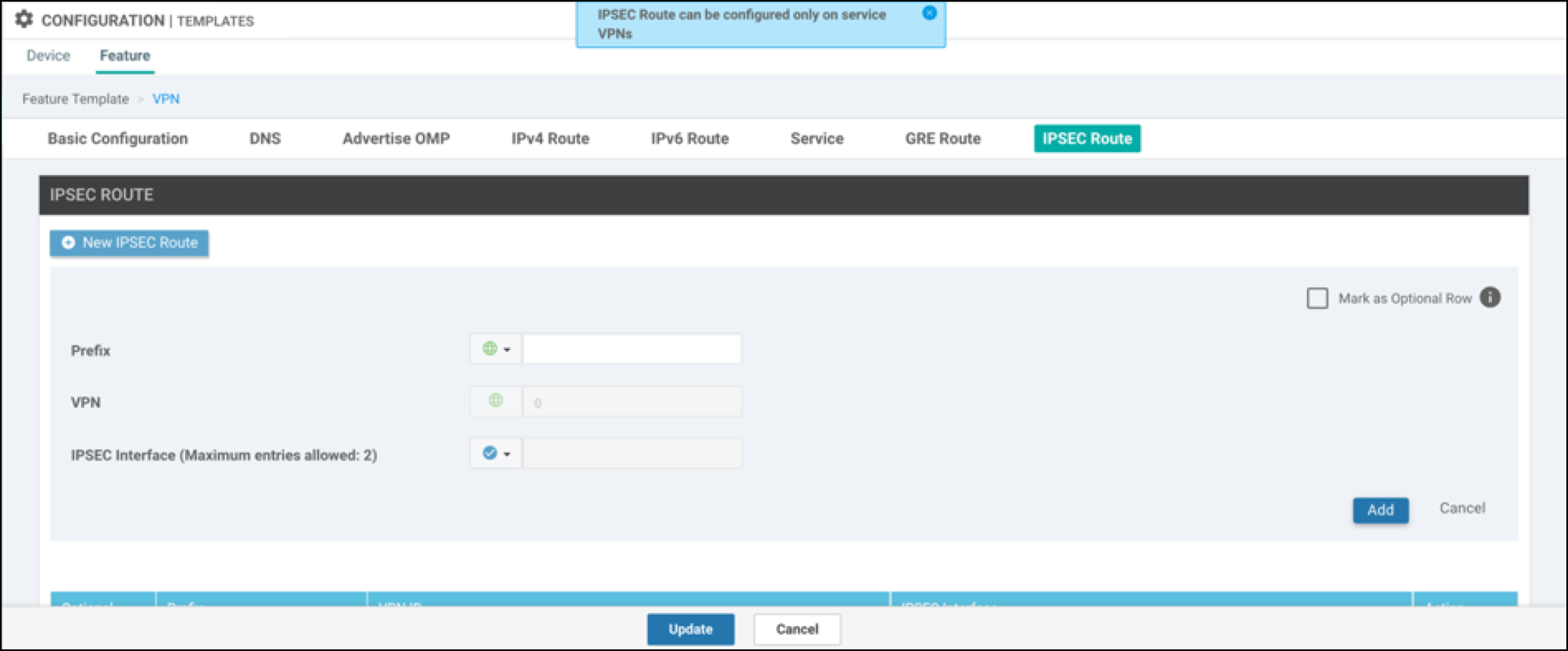
In this example, the default IPSec route is set to the ipsec1 tunnel interface.
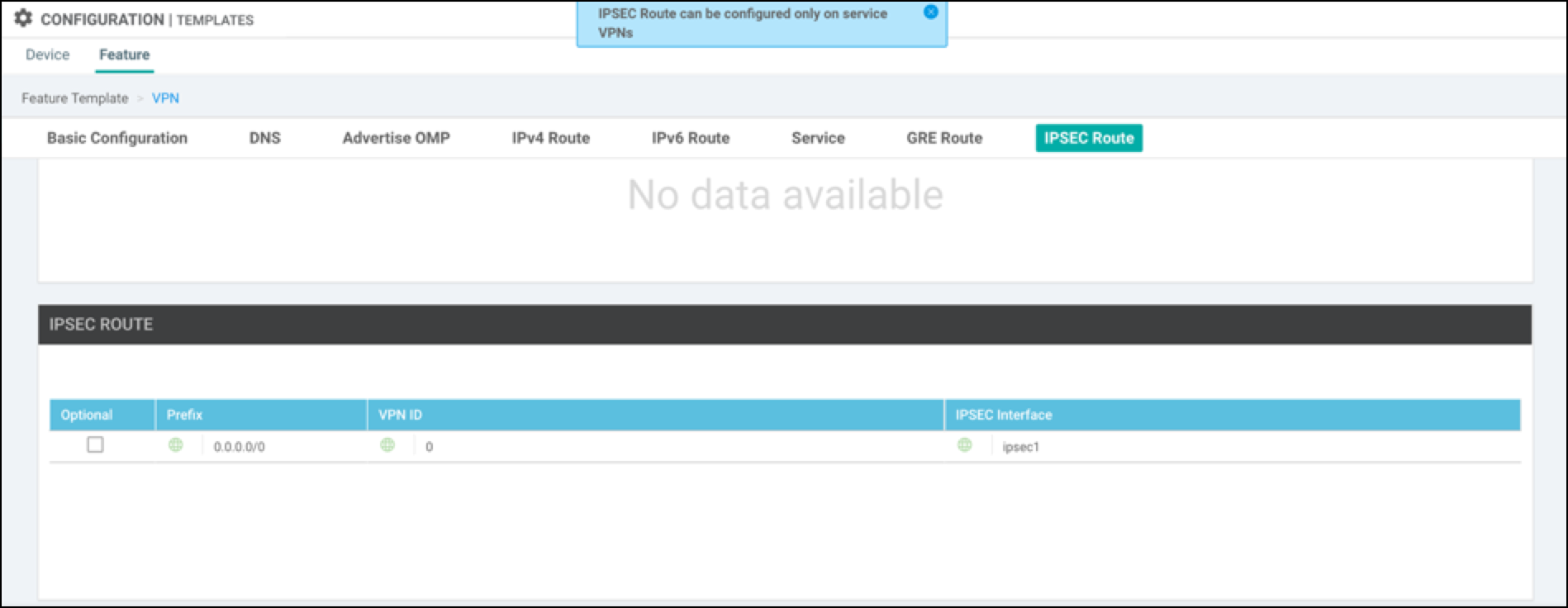
- Save configuration changes.
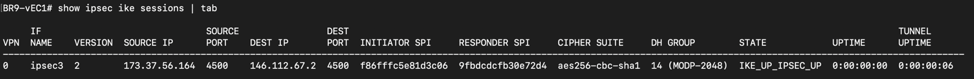
- Log into the vManage console and navigate to Monitor > Network > vEdge > Device.
- Choose a device, then choose Interface to check the status of the IPSec tunnel for ipsec1.
Alternatively, the following is an example of checking the tunnel status through the CLI.
Network Tunnel Configuration < Configure Tunnels Manually with Viptela vEdge > Configure Tunnels Manually with Viptela cEdge
Updated almost 2 years ago
