Manage Internal Networks
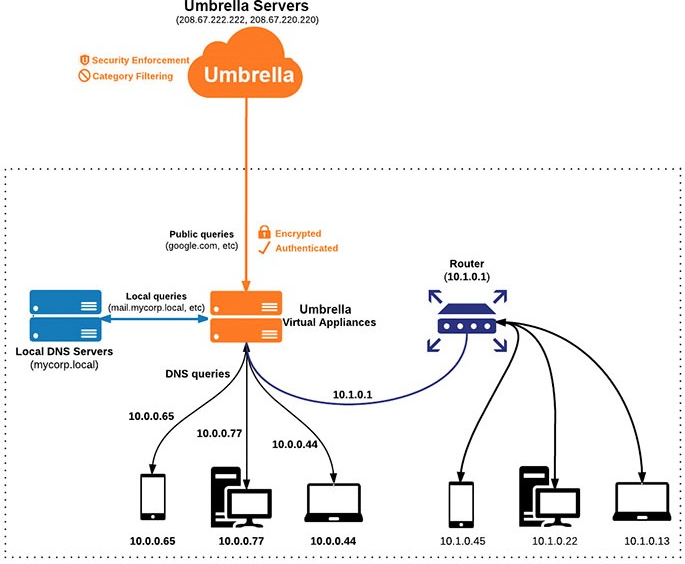
Internal Networks allow Umbrella to manage traffic sent from computers on the subnets or internal IP addresses of your networks. You must associate an Internal Network with an Umbrella Site, Network, or Network Tunnel. Once you add an Internal Network, you can monitor and filter traffic received by Umbrella from computers on the subnets or internal IP addresses of your networks.
Table of Contents
- Prerequisites
- Before You Begin
- Internal Network Associations
- Procedure
- Apply Policies to Internal Network
Prerequisites
- Full admin access to the Umbrella dashboard. See Manage User Roles.
Before You Begin
If you intend to implement Active Directory integration, in addition to Umbrella Virtual Appliances (VAs), see Connect Multiple Active Directory Domains to Umbrella.
Note: For Internal Networks with DNS-layer security, Umbrella requires Site and VA deployments.
Internal Network Associations
Depending on the Umbrella deployments in your organization, you must associate each Internal Network with either a Site, Network, or Network Tunnel.
| Umbrella Traffic Forwarder | Use Cases |
|---|---|
| Site | For use with Umbrella Virtual Appliances (VAs) to identify DNS traffic based on the internal source IP. |
| Network | For use with Umbrella Secure Web Gateway (SWG) to identify web requests based on the internal source IP. Requires a proxy chaining configuration with X-Forwarded-For headers enabled. See the Manage Proxy Chaining documentation for more information. |
| Network Tunnel | For use with the Umbrella Secure Web Gateway (SWG) and Cloud-delivered Firewall (CDFW) to identify web traffic based on the internal source IP. Requires a Network Tunnel (IPSec) connection to Umbrella. See the Network Tunnel Configuration documentation for more information. |
Procedure
In Umbrella, add an IP address or IP address range to create an Internal Network identity.
- Navigate to Deployments > Configuration > Internal Networks and click Add.

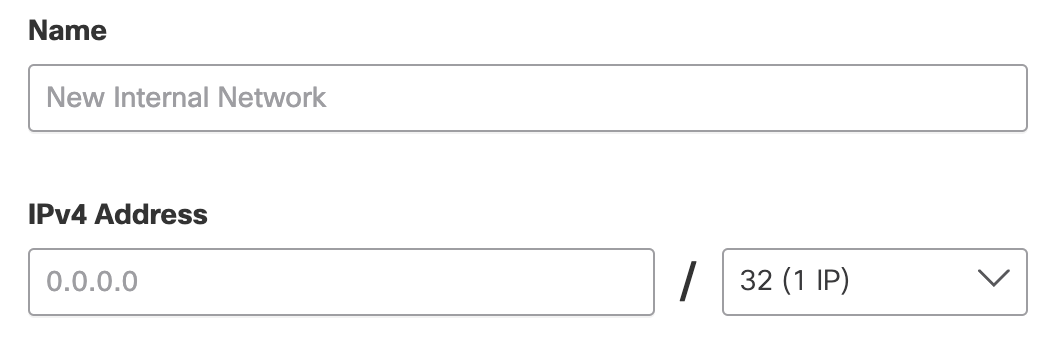
- Enter a Name for the internal network and an IPv4 Address or address range.
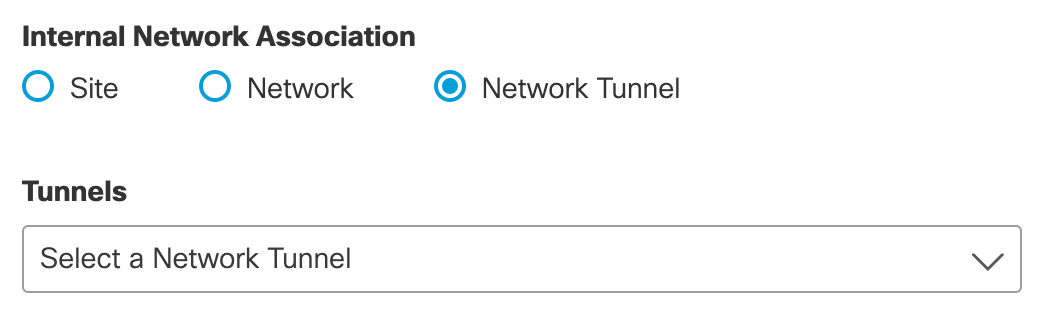
- For Internal Network Association, choose Site, Network, or Network Tunnel.
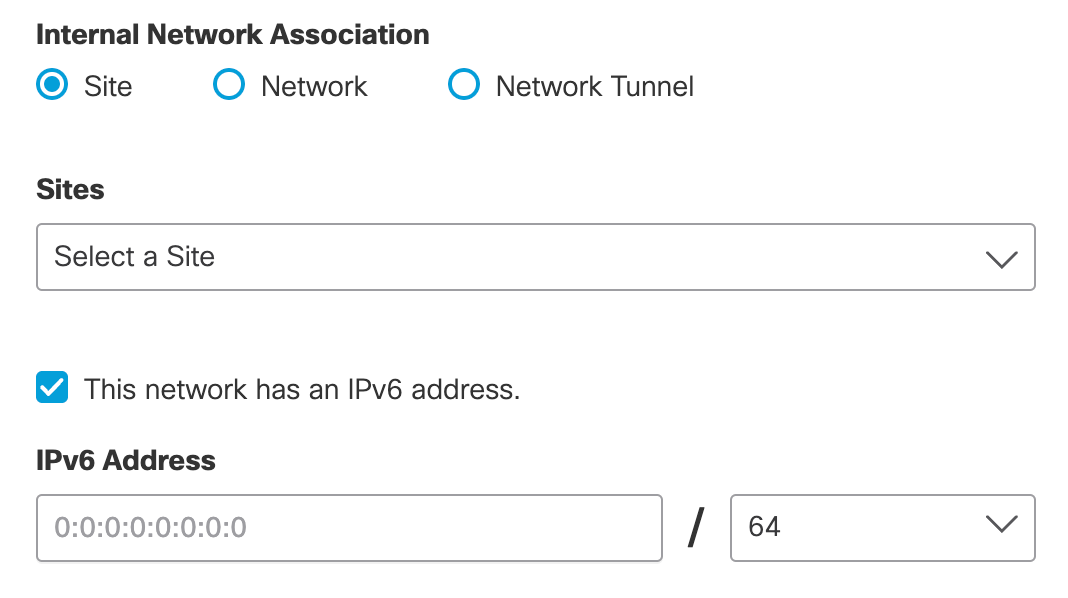
a. Site—From the drop-down menu, select a site to associate with the Internal Network.
If you have endpoints with IPv6 addresses in a site, you can add them to the network. Check This network has an IPv6 address and enter the IPv6 address or IPv6 address range for the network.
Note: Umbrella supports only dual-stack networks. An IPv6 network must co-exist with an IPv4 network, and you cannot create an IPv6-only network.
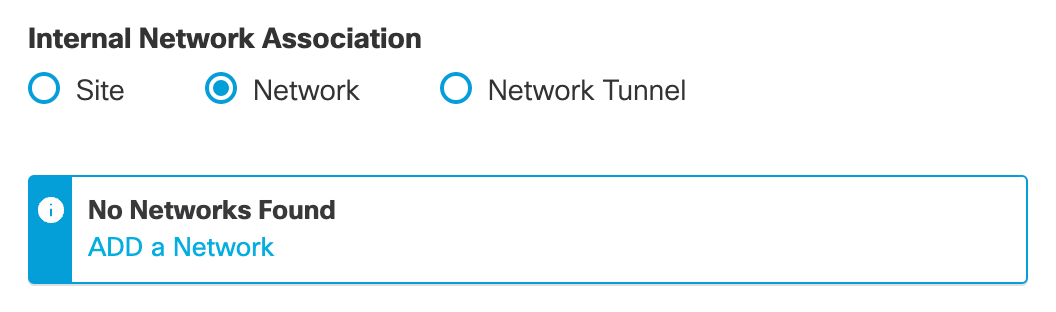
b. Network—From the drop-down menu, select a specific network to associate with the Internal Network, or click Add a Network.
c. Network Tunnel—From the drop-down menu, select a specific network tunnel or choose all of your organization's tunnels to associate with the Internal Network.
- Click Save.
Note: If you are unable to save your changes, check that the IP address range is valid. The final octet of your IP range should match the mask for that range. More information about subnet masks is available from many third-party websites.
Apply Policies to Internal Network
You can identify and filter the traffic from the IP address of the Internal Network in the Activity Search report. Umbrella uses the Internal Network's IP address to create policies for security and category filtering.
- A DNS policy applies to an Internal Network deployed with a Site. For more information, Assign a DNS Policy to Your Site.
- A Web policy applies to an Internal Network deployed with a Network or Network Tunnel. For more information, see Manage the Web Policy.
Manage Sites < Manage Internal Networks > Assign a DNS Policy to Your Site
Updated almost 2 years ago
